Trojan.JS.NODSTER.A
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This malware is part of the fileless botnet Novter that is delivered via the KovCoreG malvertising campaign.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be downloaded by other malware/grayware from remote sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be downloaded by the following malware/grayware from remote sites:
- Trojan.Win32.Novter.A
Installation
This Trojan drops the following files:
- %System%\IsAdm.txt - to test the user if it has admin privileges, deleted afterwards if successful.
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
Other Details
This Trojan does the following:
- On Windows 7, it downloads and installs the following Windows update saved as {Malware Path}\SystemInfoConfig\Windows6.1-KB3033929-{x86|x64}.msu from the following URLs:
- https://download.{BLOCKED}ft.com/download/C/8/7/C87AE67E-A228-48FB-8F02-B2A9A1238099/Windows6.1-KB3033929-x64.msu
- https://download.{BLOCKED}ft.com/download/3/7/4/37473F39-5728-4153-9A25-64C09DE9ED52/Windows6.1-KB3033929-x86.msu
- If executed as admin and the value of HKLM\Software\ttl\ttl is not 64, it executes the following commands:
- netsh.exe interface tcp set heuristics ws=disabled
- reg.exe add HKLM\SYSTEM\CurrentControlSet\services\Tcpip\Parameters /v DefaultTTL /t REG_DWORD /d 0x40 /f
- reg.exe add HKLM\SYSTEM\CurrentControlSet\services\Tcpip\Parameters /v Tcp1323Opts /t REG_DWORD /d 0x02 /f
- reg.exe add HKLM\Software\ttl /v ttl /t REG_DWORD /d 0x40 /f
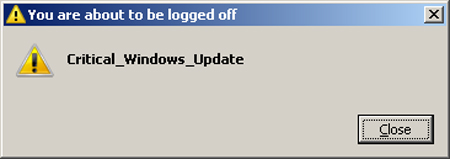
- To apply the changes done by this malware, it displays the ff. message and shuts down the computer after two minutes:
- It downloads node.exe from https://{BLOCKED}js.org/dist/latest-v10.x/win-x86/node.exe and saved as {malware path}\SystemInfoConfig\node.exe
- It checks for the following presence of files:
- {malware path}\SystemInfoConfig\app.js
- {malware path}\SystemInfoConfig\divergent.exe
- {malware path}\SystemInfoConfig\mdivergent.exe
- {malware path}\SystemInfoConfig\WinDivert.dll
- {malware path}\SystemInfoConfig\WinDivert32.sys
- {malware path}\SystemInfoConfig\WinDivert64.sys
If one of the files is absent, it drops {malware path}\SystemInfoConfig\{numbers}.zip containing the following files and folders:- {current or malware path}\SystemInfoConfig\node_modules
- {current or malware path}\SystemInfoConfig\app.js
- {current or malware path}\SystemInfoConfig\constants.js
- {current or malware path}\SystemInfoConfig\divergent.exe
- {current or malware path}\SystemInfoConfig\mdivergent.exe
- {current or malware path}\SystemInfoConfig\socks4a.js
- {current or malware path}\SystemInfoConfig\WinDivert.dll
- {current or malware path}\SystemInfoConfig\WinDivert32.sys
- {current or malware path}\SystemInfoConfig\WinDivert64.sys
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\lib
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\lib\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\lib\manager.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\lib\on.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\lib\socket.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\lib\url.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-emitter
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-binary2
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\isarray
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ms
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\safe-buffer
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\to-array
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ultron
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\yeast
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\.travis.yml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\LICENCE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\test
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\after\test\after-test.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\LICENCE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\test
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\arraybuffer.slice\test\slice-buffer.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\.travis.yml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\coverage.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov.info
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\async-throttle
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\base.css
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\index.html
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\prettify.css
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\prettify.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\sort-arrow-sprite.png
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\sorter.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\async-throttle\index.html
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\async-limiter\coverage\lcov-report\async-throttle\index.js.html
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\test
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\backo2\test\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\.travis.yml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\lib
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\LICENSE-MIT
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\base64-arraybuffer\lib\base64-arraybuffer.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\example.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\better-assert\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.zuul.yml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\test
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\blob.iml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\inspectionProfiles
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\markdown-navigator
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\markdown-navigator.xml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\modules.xml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\vcs.xml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\workspace.xml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\inspectionProfiles\profiles_settings.xml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\.idea\markdown-navigator\profiles_settings.xml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\blob\test\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\callsite\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-bind\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-emitter\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-emitter\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-emitter\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-emitter\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-emitter\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\test
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\component-inherit\test\inherit.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\.coveralls.yml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\.eslintrc
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\.travis.yml
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\CHANGELOG.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\karma.conf.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\node.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\src
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\src\browser.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\src\debug.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\src\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\debug\src\node.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\engine.io.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\socket.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transport.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transports
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\xmlhttprequest.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transports\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transports\polling-jsonp.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transports\polling-xhr.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transports\polling.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-client\lib\transports\websocket.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\lib
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\lib\browser.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\lib\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\lib\keys.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\engine.io-parser\lib\utf8.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-binary2\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-binary2\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-binary2\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-binary2\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-binary2\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\has-cors\test.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\indexof\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\isarray\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\isarray\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\isarray\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ms\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ms\license.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ms\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ms\readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\component.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\test
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\object-component\test\object.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseqs\test.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\History.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\Makefile
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\parseuri\test.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\safe-buffer\index.d.ts
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\safe-buffer\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\safe-buffer\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\safe-buffer\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\safe-buffer\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser\binary.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser\is-buffer.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\socket.io-parser\Readme.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\to-array\.npmignore
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\to-array\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\to-array\LICENCE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\to-array\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\to-array\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ultron\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ultron\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ultron\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ultron\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\.DS_Store
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\BufferUtil.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\Constants.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\ErrorCodes.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\EventTarget.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\Extensions.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\PerMessageDeflate.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\Receiver.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\Sender.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\Validation.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\WebSocket.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\ws\lib\WebSocketServer.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\autotest.watchr
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\example
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\lib
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\README.md
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\example\demo.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\lib\XMLHttpRequest.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-constants.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-events.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-exceptions.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-headers.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-redirect-302.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-redirect-303.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-redirect-307.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-request-methods.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\test-request-protocols.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\xmlhttprequest-ssl\tests\testdata.txt
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\yeast\index.js
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\yeast\LICENSE
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\yeast\package.json
- {current or malware path}\SystemInfoConfig\node_modules\socket.io-client\node_modules\yeast\README.md
- Once the files are extracted and the updates are installed, it executes the following commands:
- {divergent.exe | mdivergent.exe}
- node.exe .\app.js {base-64 encoded address = {BLOCKED}.{BLOCKED}.117.194}
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Identify and terminate files detected as Trojan.JS.NODSTER.A
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\Tcpip\Parameters
- DefaultTTL = 64
- DefaultTTL = 64
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\Tcpip\Parameters
- Tcp1323Opts = 2
- Tcp1323Opts = 2
- In HKEY_LOCAL_MACHINE\SOFTWARE\ttl
- ttl = 64
- ttl = 64
Step 5
Search and delete this folder
- {malware path}\SystemInfoConfig
Step 6
Scan your computer with your Trend Micro product to delete files detected as Trojan.JS.NODSTER.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


