Ransom.Win32.DOPPELPAYMER.TGACAP
HEUR:Trojan.Win32.Zenpak.vho (KASPERSKY); Gen:Variant.Razy.676552 (BITDEFENDER)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
Downloaded from the Internet
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It deletes itself after execution.
It drops files as ransom note.
TECHNICAL DETAILS
5,574,656 bytes
EXE
Yes
08 Jun 2020
Encrypts files, Displays message/message boxes
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %Application Data%\{Random Name} - dropped copy of itself
- When run with administrator privileges:
- %Application Data%\{Random}\{Dll Name from %System% directory}.dll - used to hijack processhacker via DLL side-loading and communicate with main malware process to terminate processes/services
- %Application Data%\{Random}\{Random Name 1} - detected as PUA.Win32.ProcHack.C
- %Application Data%\{Random}\{Random Name 2} - detected as PUA.Win32.ProcHack.B.component
- %System%\GroupPolicy\gpt.ini
- When ran without administrator privileges:
- %Application Data%\{Random Name}\{Random Name}.exe - dropped copy of itself
It adds the following processes:
- %Application Data%\{Random Name} {argument to execute} {Malware Filename}
- When ran with administrative privileges:
- %System%\bcedit.exe /set {default} safeboot minimal
- %System%\bcedit.exe /set default recoveryenabled no
- %System%\vssadmin.exe Delete Shadows /All /Quiet - delete shadow copy
- %Application Data%\{Random}\{Random Name 2} {argument} 1337039846
- When ran without administrative privileges:
- %System%\icacls.exe "C:\*" /grant:r Everyone:F /t /c /q - grant permission to access C directory
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{Random} = %Application Data%\{Random Name}\{Random Name}.exe
Other System Modifications
This Ransomware modifies the following registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
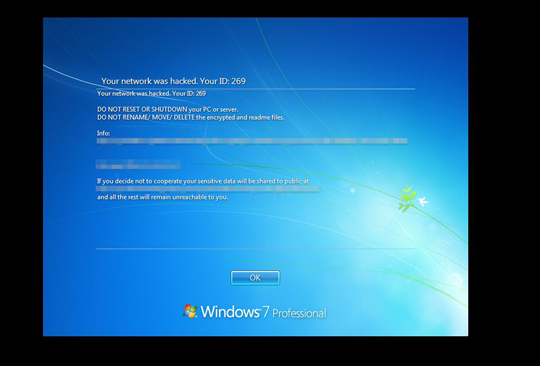
LegalNoticeCaption = Your network was hacked. Your ID: {ID}
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
LegalNoticeText = Your network was hacked. Your ID: {ID} DO NOT RESET OR SHUTDOWN your PC or server...DO NOT RENAME/ MOVE/ DELETE the encrypted and readme files Info:http://{BLOCKED}.onion/order/001f639d-ddcd-50a6-9b48-8ed9b1ec7448 {BLOCKED}port@protonmail.com....Ifyou decide not to cooperate your sensitive data will be shared to public at http://{BLOCKED}.onion ..and all the rest will remain unreachable to you
Adware Routine
This Ransomware deletes itself after execution.
Other Details
This Ransomware does the following:
- When ran with administrator privileges, it will do the following:
- Adds the following service:
Service Name: KProcessHacker3
Image Path: %Application Data%\{Random}\{Random Name 2} - It tries to look for services running in the machine and tries to disable some of them. Below are some of the services it tries to disable:
- SDRSVC
- sstpsvc
- StorSVC
- swprv
- wbengine
- ui0detect
- Based on the services it tries to look for in the machine, it will try to take ownership of this service using the following command:
- %System%\takeown.exe /F %System%\{file name}.exe
- %System%\icacls.exe %System%\{file name}.exe /reset
- It will then rename the original file name to {file name}.exe-0, and replace the original file with its copy.
- It will then restart the machine in safe mode and prevent the user from logging in
- It renames the following file when found in the machine:
- %Windows%\Microsoft.NET\Framework64\v4.0.30319\SMSvcHost.exe renamed to %Windows%\Microsoft.NET\Framework64\v4.0.30319\SMSvcHost.exe_
- Adds the following service:
- When ran without administrator privileges, it will do the following:
- It will only install its autorun registry when ran without administrative privileges
- It requires to be executed with the following argument in order to proceed with its malicious routine:
- zTWqycy0yqmFLUBlyMF2859f
- It uses the following information to generate random characters for the file name it will drop:
- Computer Name
- It enumerates registry keys to gather system information
- It will encrypt files found in the following set of drives in the affected system:
- Network Drives
- Fixed Drives
- Removable Drives
- It uses the following set of commands to gather the network drives connected to the system and connect to the following network drives to encrypt it's files:
- %System%\net.exe view igmp.mcast.net
- %System%\arp.exe -a
- %System%\nslookup.exe {IP address}
- It changes the passwords of all the users in the affected system
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- V01.lo*
- V01.ch*
- V01res*.jrs
- RacWmi*.sdf
- Web*V01.dat
- default.rdp
- NTUSER.DA*
- *.lnk
- *.ico
- *.ini
- *.msi
- *.chm
- *.lng
- *.inf
- *.hlf
- *.sys
- *.ttf
- *.cmd
- .DLL
- .exe
- schre*.bat
- svsho*.exe
It avoids encrypting files with the following strings in their file path:
- System Volume Information
- $Recycle.Bin
- WebCache
- Caches
- VirtualStore
It appends the following extension to the file name of the encrypted files:
- .doppeled
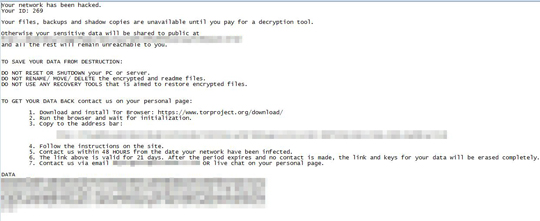
It drops the following file(s) as ransom note:
- {Encrypted File Name}.how2decrypt.txt
SOLUTION
9.850
15.922.05
10 Jun 2020
15.923.00
11 Jun 2020
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
-
Troj.Win32.TRX.XXPE50FFF036
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services
- KProcessHacker3 (For the created service when ran with administrative privileges)
- KProcessHacker3 (For the created service when ran with administrative privileges)
Step 6
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {Random} = %Application Data%\{Random Name}\{Random Name}.exe
- {Random} = %Application Data%\{Random Name}\{Random Name}.exe
Step 7
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this only if you know how to or you can seek your system administrator’s help. You may also check out this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- From: LegalNoticeCaption = Your network was hacked. Your ID: {ID}
To: LegalNoticeCaption = {Default}
- From: LegalNoticeCaption = Your network was hacked. Your ID: {ID}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- From: LegalNoticeText = Your network was hacked. Your ID: {ID} DO NOT RESET OR SHUTDOWN your PC or server...DO NOT RENAME/ MOVE/ DELETE the encrypted and readme files Info:{BLOCKED}.onion/order/001f639d-ddcd-50a6-9b48-8ed9b1ec7448 {BLOCKED}port@protonmail.com....Ifyou decide not to cooperate your sensitive data will be shared to public at http://{BLOCKED}onion ..and all the rest will remain unreachable to you
To: LegalNoticeText = {Default}
- From: LegalNoticeText = Your network was hacked. Your ID: {ID} DO NOT RESET OR SHUTDOWN your PC or server...DO NOT RENAME/ MOVE/ DELETE the encrypted and readme files Info:{BLOCKED}.onion/order/001f639d-ddcd-50a6-9b48-8ed9b1ec7448 {BLOCKED}port@protonmail.com....Ifyou decide not to cooperate your sensitive data will be shared to public at http://{BLOCKED}onion ..and all the rest will remain unreachable to you
Step 8
Search and delete these files
- %Application Data%\{Random Name}
- %Application Data%\{Random}\{Dll Name from %System% directory}.dll
- %Application Data%\{Random}\{Random Name 1}
- %Application Data%\{Random}\{Random Name 2}
- %System%\GroupPolicy\gpt.ini
- %Application Data%\{Random Name}\{Random Name}.exe
- {Encrypted File Name}.how2decrypt.txt
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.DOPPELPAYMER.TGACAP. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 10
Restore encrypted files from backup.
Step 11
Since this malware cannot be removed in normal and safe mode, it is necessary to restart using the Windows Recovery Console. To restart the system using the Windows Recovery Console:
• On Windows 7 and Server 2008 (R2) systems:
- Insert your Windows Installation DVD in the DVD drive, then Press the restart button.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to select the installation language. Then on the Install Windows window, choose your language, locale, and keyboard layout or input method. Click Next, then click Repair your computer.
- Select Use recovery tools that can help fix problems starting Windows. Select your installation of Windows. Click Next.
- If the Startup Repair window appears, click Cancel, Yes, then Finish.
- In the System Recovery Options window, click Command Prompt.
- In the Command Prompt window, type the following then press Enter:
- bcedit.exe /set {default} recoveryenabled Yes
- bcdedit.exe /deletevalue {current} safeboot
(Note: In Windows 7, all local drives will be assigned one more than normal. For example, the C: drive becomes D:.) - Type exit and press Enter to close the Command Prompt window.
- Click Restart to restart the system normally.
• On Windows 8, 8.1, 10, and Server 2012 systems:
- Insert your Windows Installation DVD in the DVD drive, then restart your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to select the keyboard layout. Then on the Windows Setup window, choose your language, locale, and input method. Click Next, then click Repair your computer.
- Click Troubleshoot>Advanced Options>Command Prompt.
- In the Command Prompt window, type the following then press Enter:
- bcedit.exe /set {default} recoveryenabled Yes
- bcdedit.exe /deletevalue {current} safeboot
- Type exit and press Enter to close the Command Prompt window.
- Click Continue to restart the system normally.
NOTES:
Note: Step 11 is necessary only if the malware is running under administrative privileges. After step 11, restart in normal mode and proceed to the remaining steps.
Did this description help? Tell us how we did.

