HackTool.Win32.RADMIN.GL
N/A
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Hacking Tool may arrive bundled with malware packages as a malware component. It may be dropped by other malware.
TECHNICAL DETAILS
Arrival Details
This Hacking Tool may arrive bundled with malware packages as a malware component.
It may be dropped by the following malware:
Installation
This Hacking Tool adds the following folders:
- %Application Data%\DNS Agent
- %Application Data%\DNS Agent\Logs
- %User Temp%\svchîst.madExcept
- %All Users Profile%\Domain name system servis
- %All Users Profile%\Domain name system servis\printer_output
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Roaming on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %All Users Profile% is the common user's profile folder, which is usually C:\Documents and Settings\All Users on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\ProgramData on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit). )
It drops the following files:
- %All Users Profile%\Domain name system servis\install.log
- when parameter /silentinstall and /silentuninstall is used
(Note: %All Users Profile% is the common user's profile folder, which is usually C:\Documents and Settings\All Users on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\ProgramData on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit). )
Autostart Technique
This Hacking Tool adds and runs the following services:
- Name: DNS-Service
- Description: Domain name system service.
- Path: %System%\drivers\svchîst.exe
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
Other System Modifications
This Hacking Tool deletes the following folders:
- %User Temp%\svchîst.madExcept
- deleted for every parameter used
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Other Details
This Hacking Tool does the following:
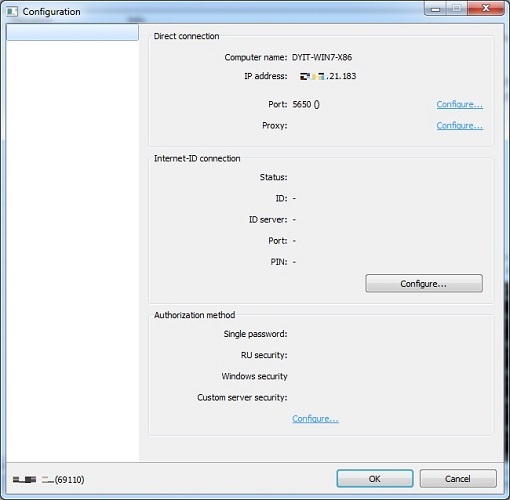
- It has capabilities of the following depending on its configuration:
- Install/Uninstall Monitor Driver
- Install/Uninstall Domain Printing
- Enable/Disable and/or configure the following settings:
- Port Connection
- Set Port Number
- Use IPv6
- Integrate with the system firewall at startup
- Proxy Server
- Set Proxy Type to one of the following:
- HTTP
- SOCKS4
- SOCKS4A
- SOCKS5
- Set Proxy's IP and Port Number
- Enable/Disable NTLM authentication
- Set Username, Password, and Domain if Proxy is Password-Protected
- Internet ID
- Generate new ID
- Select Internet ID Server
- Popup menu of the system tray icon
- Notification Panel
- Balloon Hints
- Sounds
- Event Logs
- Password Protect Settings
- Password Protect Callback Settings
- Password Protect Internet-ID Settings
- Capturing RDP Sessions
- Internet-ID and Callback Connections
- Legacy Capture Mode
- Auto Connect
- Set auto connect interval (seconds)
- Single Password
- Set Password
- Domain Utilities Security
- Add and edit users' profile
- Windows Security
- Modify access control and permissions
- Custom Server Security
- Add/Edit/Remove servers
- Two Faction Authentication
- User Permission
- Auto deny/allow after timeout
- Set timeout (seconds)
- Whitelist and Blacklist IP Addresses
- Add/Edit/Remove Single IP
- Add/Edit/Remove IP range
- Connection modes
- Domain Control
- Domain Screen
- File Transfer
- Redirect Connections
- Telnet
- Domain Execute
- Task Manager
- Shutdown
- Domain Upgrade
- Preview Screen Capture
- Device Manager
- Chat
- Screen Recorder
- Text Message
- Domain Registry
- Audio & Video Chat
- Domain Settings
- Domain Printing
- RDP
- Create and export a certificate as .pem file
It accepts the following parameters:
- /silentinstall - install the Host service
- /silentuninstall - uninstall the Host
- /firewall - integrate with the Windows XP / Vista / 7
- /start - start the server
- /stop - stop the server
- /config - open the settings window with password
- /config /user - open the settings window
- /printerinstall - install the RMS virtual printer.
- /printeruninstall - uninstall the RMS virtual printer
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Identify and terminate files detected as HackTool.Win32.RADMIN.GL
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Restart in Safe Mode
Step 5
Search and delete this file
- %All Users Profile%\Domain name system servis\install.Logs
Step 6
Search and delete these folders
- %Application Data%\DNS Agent
- %Application Data%\DNS Agent\Logs
- %User Temp%\svchîst.madExcept
- %All Users Profile%\Domain name system servis
- %All Users Profile%\Domain name system servis\printer_output
Step 7
Scan your computer with your Trend Micro product to delete files detected as HackTool.Win32.RADMIN.GL. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


