Trojan.HTML.DLOADR.VWEF
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It does not have any file infection routine.
It does not have any propagation routine.
It does not have any backdoor routine.
It does not have any information-stealing capability.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Infection Points
This Trojan does not have any file infection routine.
Propagation
This Trojan does not have any propagation routine.
Backdoor Routine
This Trojan does not have any backdoor routine.
Rootkit Capabilities
This Trojan does not have rootkit capabilities.
Download Routine
This Trojan accesses the following websites to download files:
- https://bit.ly/{BLOCKED}x, which redirects to:
http://data.{BLOCKED}ews.club:8080/open?id=mFUbNFblIJmSb9c%2BJEXIr5pN2CfgrYUlLghqsNVHd%2Bo%3D
Information Theft
This Trojan does not have any information-stealing capability.
Other Details
This Trojan does the following:
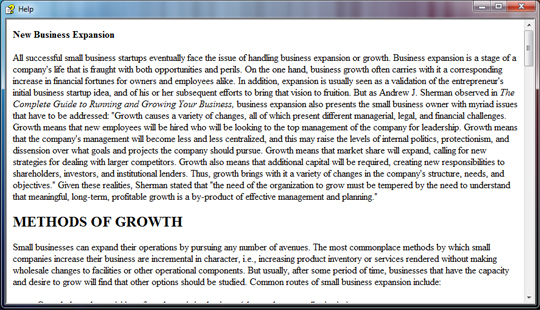
- Displays the following window:
NOTES:
However, as of this writing, the said sites are inaccessible.
It does not exploit any vulnerability.
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as Trojan.HTML.DLOADR.VWEF. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


