TrojanSpy.Win64.XEELASTEAL.A
UDS:Trojan-PSW.Win64.Agent.a (KASPERSKY)
Windows


Threat Type: Trojan Spy
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It logs a user's keystrokes to steal information.
TECHNICAL DETAILS
Arrival Details
This Trojan Spy arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan Spy drops the following copies of itself into the affected system:
- %AppDataLocal%\WindowsUpdateChecker\AutoUpdater.exe
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It drops the following files:
- %System Root%\__tmp_rar_sfx_access_check_{Random}
- %System Root%\şirket-ruhsat.pdf.exe → information stealer
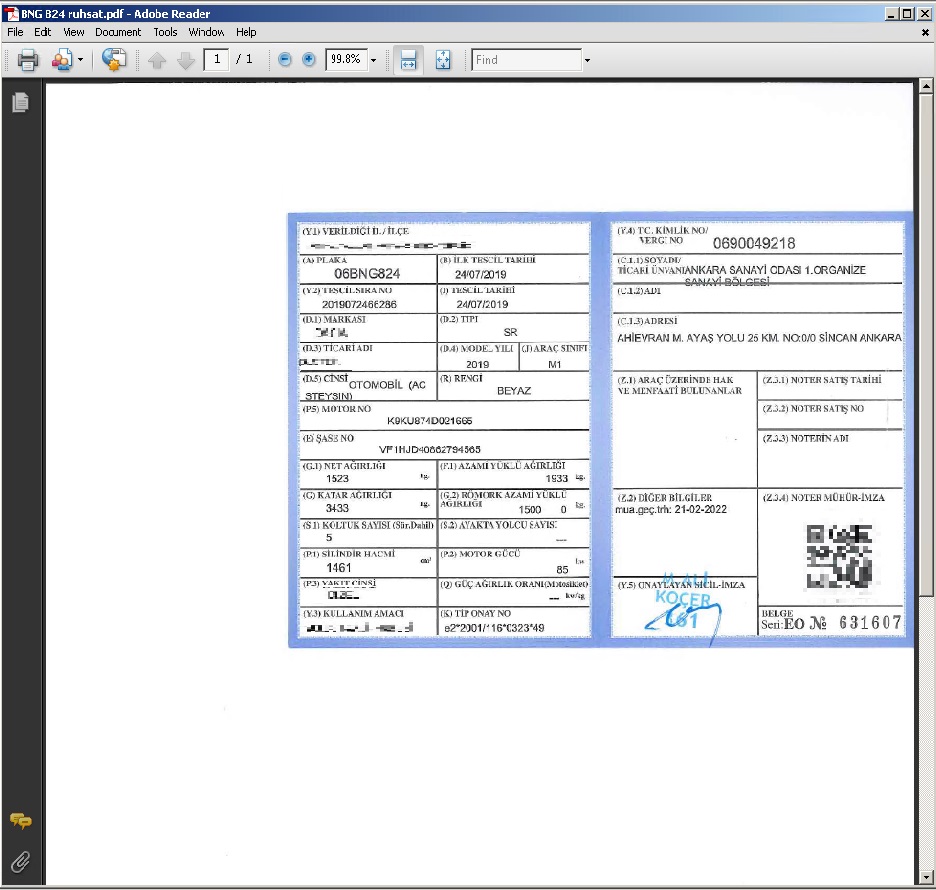
- %System Root%\BNG 824 ruhsat.pdf → serves as a decoy pdf file
- %User Temp%\login_data_copy.db
(Note: %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- "{Path To Default PDF Document Reader}" "%System Root%\BNG 824 ruhsat.pdf"
- %System Root%\şirket-ruhsat.pdf.exe
- %System%\cmd.exe /c "ver"
- wmic csproduct get uuid
- taskkill /IM chrome.exe
- %System%\cmd.exe /c "powershell.exe -NoProfile -ExecutionPolicy Bypass -EncodedCommand {Base64 Encoded Command}"
- %System%\cmd.exe /c "tasklist /FO LIST"
- powershell.exe Get-Clipboard
- powershell.exe -Command "$clipboardData = Get-Clipboard -Format Image $destinationPath = \"%User Temp%\{UUID}\last_clipboard_image.png\" $clipboardData.Save($destinationPath)"
- %System%\cmd.exe /c "echo ####System Info#### & systeminfo & echo ####System Version#### & ver & echo ####Host Name#### & hostname & echo ####Environment Variable#### & set & echo ####Logical Disk#### & wmic logicaldisk get caption,description,providername & echo ####User Info#### & net user & echo ####Startup Info#### & wmic startup get caption,command & echo ####Firewallinfo#### & netsh firewall show state"
- netsh.exe netsh wlan export profile key=clear
- %System%\cmd.exe /c "netsh wlan show profile"
- %System%\cmd.exe /c "netsh wlan show profile {profile} key=clear"
- schtasks /create /f /sc onlogon /rl highest /tn "AutoUpdateChecker" /tr "%AppData%\WindowsUpdateChecker\AutoUpdater.exe"
(Note: %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.. %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It creates the following folders:
- %User Temp%\{UUID}
- %User Temp%\{UUID}\Passwords
- %User Temp%\{UUID}\Cards
- %User Temp%\{UUID}\Cookies
- %User Temp%\{UUID}\Downloads
- %User Temp%\{UUID}\Historys
- %User Temp%\{UUID}\Firefox
- %User Temp%\{UUID}\Instagram
- %User Temp%\{UUID}\Twitter
- %User Temp%\{UUID}\Tiktok
- %User Temp%\{UUID}Reddit
- %User Temp%\{UUID}\Discord
- %User Temp%\{UUID}\Steam
- %User Temp%\{UUID}\Roblox
- %AppDataLocal%\WindowsUpdateChecker
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Exela
Process Termination
This Trojan Spy terminates the following processes if found running in the affected system's memory:
- chrome.exe
Dropping Routine
This Trojan Spy drops the following files wherein it saves the information it gathers:
- %User Temp%\{UUID}\Passwords\Passwords.txt
- %User Temp%\{UUID}\Cards\Cards.txt
- %User Temp%\{UUID}\Cookies\Cookies.txt
- %User Temp%\{UUID}\Downloads\Downloads.txt
- %User Temp%\{UUID}\Historys\Historys.txt
- %User Temp%\{UUID}Firefox\History.txt
- %User Temp%\{UUID}\Firefox\Cookies.txt
- %User Temp%\{UUID}\Instagram\instagram.txt
- %User Temp%\{UUID}\Twitter\Twitter.txt
- %User Temp%\{UUID}\Tiktok\Tiktok.txt
- %User Temp%\{UUID}Reddit\Reddit.txt
- %User Temp%\{UUID}\Discord\Discord.txt
- %User Temp%\{UUID}\Steam\Steam.txt
- %User Temp%\{UUID}\Roblox\Roblox.txt
- %User Temp%\{UUID}\Display({Index of Display}).png
- %User Temp%\{UUID}\active_window.txt
- %User Temp%\{UUID}\process_list.txt
- %User Temp%\{UUID}\last_clipboard_text.txt
- %User Temp%\{UUID}\last_clipboard_image.png
- %User Temp%\{UUID}\system_info.txt
- %User Temp%\{UUID}\Wifi.txt
- %User Temp%\{UUID}.zip
- %User Temp%\key_logs.txt
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Information Theft
This Trojan Spy gathers the following data:
- Browser Data (e.g. Browsing History, Cookies, Credit Card Information, Download History, Log In Credentials)
- Brave
- Chrome
- Edge
- Firefox (Browsing History and Cookies only)
- Opera
- Opera GX
- Vivaldi
- Online Account Information
- Discord
- Billing Information
- Biography
- Multifactor Authentication Status
- Phone Number
- Profile Picture
- Subscription Type
- Token
- User ID
- Username
- Instagram
- Biography
- Full Name
- Profile Picture
- Profile URL
- Session ID
- Username
- Verification Status
- Reddit
- Coins
- Comment Karma
- Gold Status
- Moderator Status
- Profile Picture
- Profile URL
- Total Karma
- Username
- Roblox
- Email Verification Status
- Profile Picture
- Profile URL
- Robux Count
- User ID
- Username
- Steam
- Account Creation Date
- Player Level
- Profile Picture
- Profile URL
- Steam ID
- Username
- Tiktok
- Coins
- Phone Number
- Profile URL
- User ID
- Username
- Twitter
- Account Creation Date
- Biography
- Follower Count
- Following Count
- Profile Picture
- Profile URL
- Screen Name
- Total Tweets
- Username
- Verification Status
- Discord
- System Information
- Active Window
- BIOS Version
- Boot Time
- Clipboard Data
- Domain
- Environment Variables
- Hostname
- Input Locale
- Installed Updates
- Logon Server
- Manufacturer
- Model
- Network Cards
- Running Processes
- Screenshot Of All Connected Displays
- Startup Programs
- System Locale
- Time Zone
- Type
- User Accounts
- Virtual Memory Information
- Wifi Network Credentials
- Windows Firewall Status
- OS Information
- Name
- Version
- Manufacturer
- Configuration
- Build Type
- Registered Owner
- Registered Organization
- Product ID
- Original Install Date
- CPU Information
- Name
- Count
- Frequency
- Manufacturer
- Memory Information
- Slot
- Capacity
- Manufacturer
- Part Number
- Speed
- Type
- GPU Information
- Name
- Memory
- Usage
- Logical Disk Information
- Disk Name
- Mount Point
- File System Type
- Capacity
- Used Space
- Free Space
- Usage Percentage
It logs a user's keystrokes to steal information.
Stolen Information
This Trojan Spy sends the gathered information via HTTP POST to the following URL:
- https://{BLOCKED}d.com/api/webhooks/1139506512302194789/X_VYZdAHscWQNKWvya9KWqqqTK6UjVvS86_kUy8P8OyCcPhKykCQpEqf93S_qDFVuzp8
Other Details
This Trojan Spy does the following:
- It displays the following as a decoy document:
- It terminates itself when the affected system's UUID is one of the following:
- 00000000-0000-0000-0000-000000000000
- 00000000-0000-0000-0000-AC1F6BD048FE
- 00000000-0000-0000-0000-AC1F6BD04972
- 00000000-0000-0000-0000-AC1F6BD04C9E
- 032E02B4-0499-05C3-0806-3C0700080009
- 03DE0294-0480-05DE-1A06-350700080009
- 11111111-2222-3333-4444-555555555555
- 129B5E6B-E368-45D4-80AB-D4F106495924
- 44B94D56-65AB-DC02-86A0-98143A7423BF
- 49434D53-0200-9036-2500-369025000C65
- 49434D53-0200-9036-2500-369025003AF0
- 49434D53-0200-9036-2500-36902500F022
- 49434D53-0200-9065-2500-65902500E439
- 4C4C4544-0050-3710-8058-CAC04F59344A
- 4D4DDC94-E06C-44F4-95FE-33A1ADA5AC27
- 5BD24D56-789F-8468-7CDC-CAA7222CC121
- 63203342-0EB0-AA1A-4DF5-3FB37DBB0670
- 6608003F-ECE4-494E-B07E-1C4615D1D93C
- 67E595EB-54AC-4FF0-B5E3-3DA7C7B547E3
- 6F3CA5EC-BEC9-4A4D-8274-11168F640058
- 71DC2242-6EA2-C40B-0798-B4F5B4CC8776
- 777D84B3-88D1-451C-93E4-D235177420A7
- 79AF5279-16CF-4094-9758-F88A616D81B4
- 7AB5C494-39F5-4941-9163-47F54D6D5016
- 8B4E8278-525C-7343-B825-280AEBCD3BCB
- 8F384129-F079-456E-AE35-16608E317F4F
- A15A930C-8251-9645-AF63-E45AD728C20C
- ADEEEE9E-EF0A-6B84-B14B-B83A54AFC548
- B1112042-52E8-E25B-3655-6A4F54155DBF
- C7D23342-A5D4-68A1-59AC-CF40F735B363
- D9142042-8F51-5EFF-D5F8-EE9AE3D1602A
- E6833342-780F-56A2-6F92-77DACC2EF8B3
- EB16924B-FB6D-4FA1-8666-17B91F62FB37
- It terminates itself if the affected system's computer name is one of the following:
- 3u2v9m8
- 6C4E733F-C2D9-4
- 8Nl0ColNQ5bq
- 8VizSM
- Abby
- ARCHIBALDPC
- B30F0242-1C6A-4
- BEE7370C-8C0C-4
- COMPNAME_4491
- d1bnJkfVlH
- DESKTOP-1PYKP29
- DESKTOP-1Y2433R
- DESKTOP-5OV9S0O
- DESKTOP-7XC6GEZ
- DESKTOP-B0T93D6
- DESKTOP-BQISITB
- DESKTOP-D019GDM
- DESKTOP-NAKFFMT
- DESKTOP-NNSJYNR
- DESKTOP-TKGQ6GH
- DESKTOP-VRSQLAG
- DESKTOP-WG3MYJS
- DESKTOP-WI8CLET
- Frank
- george
- HEUeRzl
- hmarc
- JOANNA
- John
- JOHN-PC
- JOHN-PC
- Julia
- JULIA-PC
- KATHLROGE
- kEecfMwgj
- Lisa
- LISA-PC
- lmVwjj9b
- ORELEEPC
- patex
- Peter Wilson
- PqONjHVwexsS
- PxmdUOpVyx
- Q9IATRKPRH
- QarZhrdBpj
- RALPHS-PC
- RDhJ0CNFevzX
- SERVER1
- w0fjuOVmCcP5A
- WDAGUtilityAccount
- WILEYPC
- WIN-5E07COS9ALR
- WINZDS-21T43RNG
- WORK
- XC64ZB
- It connects to the following URLs while using the acquired browser cookies to retrieve online account information:
- https://{BLOCKED}agram.com/api/v1/accounts/current_user/?edit=true
- https://{BLOCKED}r.com/i/api/1.1/account/update_profile.json
- https://{BLOCKED}ok.com/passport/web/account/info/?aid=1459&app_language=de-DE&app_name=tiktok_web&battery_info=1&browser_languagede-DE&browser_name=Mozilla&browser_online=true&browser_platform=Win32&browser_version=5.0%20%28Windows%20NT%2010.0%3B%20Win64%3B%20x6%29%20AppleWebKit%2F537.36%20%28KHTML%2C%20like%20Gecko%29%20Chrome%2F112.0.0.0%20Safari%2F537.36&channel=tiktok_web&cookie_enabled=tue&device_platform=web_pc&focus_state=true&from_page=fyp&history_len=2&is_fullscreen=false&is_page_visible=true&os=windows&priority_rgion=DE&referer=®ion=DE&screen_height=1080&screen_width=1920&tz_name=Europe%2FBerlin&webcast_language=de-DE
- https://{BLOCKED}t.tiktok.com/webcast/wallet_api/diamond_buy/permission/?aid=1988&app_language=de-DE&app_name=tiktok_web&battery_inf=1&browser_language=de-DE&browser_name=Mozilla&browser_online=true&browser_platform=Win32&browser_version=5.0%20%28Windows%20NT%2010.%3B%20Win64%3B%20x64%29%20AppleWebKit%2F537.36%2%28KHTML%2C%20like%20Gecko%29%20Chrome%2F112.0.0.0%20Safari%2F537.36&channel=tiktok_web&cookie_enabled=true
- https://{BLOCKED}ts.reddit.com/api/access_token
- https://{BLOCKED}blox.com/my/account/json
- https://{BLOCKED}y.roblox.com/v1/users/{User ID}/currency
- https://{BLOCKED}ails.roblox.com/v1/users/avatar?userIds={User ID}&size=420x420&format=Png&isCircular=false
- https://{BLOCKED}eampowered.com/ISteamUser/GetPlayerSummaries/v0002/?key=440D7F4D810EF9298D25EDDF37C1F902&steamids={Steam ID}
- https://{BLOCKED}eampowered.com/IPlayerService/GetSteamLevel/v1/?key=440D7F4D810EF9298D25EDDF37C1F902&steamid={Steam ID}
- https://{BLOCKED}d.com/api/v8/users/@me
- https://{BLOCKED}d.com/api/v6/users/@me/billing/payment-sources
- https://{BLOCKED}scordapp.com/avatars/{Discord ID}/{Discord Profile Picture URL}.png
It adds the following scheduled tasks:
- Task Name: AutoUpdateChecker
- Trigger: At log on of any user
- Action: Start a Program - %AppDataLocal%\WindowsUpdateChecker\AutoUpdater.exe
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- Troj.Win32.TRX.XXPE50FFF078
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Deleting Scheduled Tasks while in Safe Mode
- Still in safe mode, the following {Task Name}-{Task to be run} listed should be used in the steps identified below:
- Task Name: AutoUpdateChecker
Task to be run: %AppDataLocal%\WindowsUpdateChecker\AutoUpdater.exe
- Task Name: AutoUpdateChecker
- For Windows 7 and Server 2008 (R2) users, click Start>Computer.
- For Windows 8, 8.1, 10, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- %System%\Tasks\{Task Name}
- Once located, select the file then press SHIFT+DELETE to delete it.
- Open Registry Editor. To do this:
- For Windows 7 and Server 2008 (R2) users, click the Start button, type regedit in the Search input field, and press Enter.
- For Windows 8, 8.1, 10, and Server 2012 (R2) users, right-click on the lower left corner of the screen, click Run, type regedit in the text box
- In the left panel of the Registry Editor window, double-click the following:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tree>{Task Name}
- Locate the created entry and take note of the registry value's data:
- ID={Task Data}
- After taking note of the data, delete the registry key:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tree>{Task Name}
- In the left panel of the Registry Editor window, double-click the following:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tasks
- Still in the left panel, locate and delete the registry key with the same name as the located Task Data in step #6:
- ={Task Data}
- Close Registry Editor.
Step 6
Search and delete these files
- %AppDataLocal%\WindowsUpdateChecker\AutoUpdater.exe
- %System Root%\__tmp_rar_sfx_access_check_{Random}
- %System Root%\BNG 824 ruhsat.pdf
- %System Root%\şirket-ruhsat.pdf.exe
- %User Temp%\login_data_copy.db
- %User Temp%\{UUID}\Passwords\Passwords.txt
- %User Temp%\{UUID}\Cards\Cards.txt
- %User Temp%\{UUID}\Cookies\Cookies.txt
- %User Temp%\{UUID}\Downloads\Downloads.txt
- %User Temp%\{UUID}\Historys\Historys.txt
- %User Temp%\{UUID}Firefox\History.txt
- %User Temp%\{UUID}\Firefox\Cookies.txt
- %User Temp%\{UUID}\Instagram\instagram.txt
- %User Temp%\{UUID}\Twitter\Twitter.txt
- %User Temp%\{UUID}\Tiktok\Tiktok.txt
- %User Temp%\{UUID}Reddit\Reddit.txt
- %User Temp%\{UUID}\Discord\Discord.txt
- %User Temp%\{UUID}\Steam\Steam.txt
- %User Temp%\{UUID}\Roblox\Roblox.txt
- %User Temp%\{UUID}\Display({Index of Display}).png
- %User Temp%\{UUID}\active_window.txt
- %User Temp%\{UUID}\process_list.txt
- %User Temp%\{UUID}\last_clipboard_text.txt
- %User Temp%\{UUID}\last_clipboard_image.png
- %User Temp%\{UUID}\system_info.txt
- %User Temp%\{UUID}\Wifi.txt
- %User Temp%\{UUID}.zip
- %User Temp%\key_logs.txt
Step 7
Search and delete these folders
- %User Temp%\{UUID}
- %User Temp%\{UUID}\Passwords
- %User Temp%\{UUID}\Cards
- %User Temp%\{UUID}\Cookies
- %User Temp%\{UUID}\Downloads
- %User Temp%\{UUID}\Historys
- %User Temp%\{UUID}\Firefox
- %User Temp%\{UUID}\Instagram
- %User Temp%\{UUID}\Twitter
- %User Temp%\{UUID}\Tiktok
- %User Temp%\{UUID}Reddit
- %User Temp%\{UUID}\Discord
- %User Temp%\{UUID}\Steam
- %User Temp%\{UUID}\Roblox
- %AppDataLocal%\WindowsUpdateChecker
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TrojanSpy.Win64.XEELASTEAL.A . If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



