Ransom.Win32.MIMIC.A
UDS:Trojan-Ransom.Win32.Mimic.q (KASPERSKY)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It deletes registry entries, causing some applications and programs to not function properly.
It encrypts files with specific file extensions. It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %User Temp%\7ZipSfx.000\7za.exe
- %User Temp%\7ZipSfx.000\Everything.exe
- %User Temp%\7ZipSfx.000\Everything32.dll
- %User Temp%\7ZipSfx.000\Everything64.dll
- %User Temp%\7ZipSfx.000\Everything.ini
- %User Temp%\7ZipSfx.000\Everything2.ini
- %User Temp%\7ZipSfx.000\Horsesperm.exe
- %User Temp%\7ZipSfx.000\sdel.exe
- %User Temp%\7ZipSfx.000\sdel64.exe
- %User Temp%\7ZipSfx.000\session.tmp
- %User Temp%\7ZipSfx.000\Defender.exe
- %AppDataLocal%\{GUID}\7za.exe → Copy file
- %AppDataLocal%\{GUID}\Everything.exe → Copy file
- %AppDataLocal%\{GUID}\Everything32.dll → Copy file
- %AppDataLocal%\{GUID}\Everything64.dll → Copy file
- %AppDataLocal%\{GUID}\Everything.ini → Copy file
- %AppDataLocal%\{GUID}\Everything2.ini → Copy file
- %AppDataLocal%\{GUID}\Horsesperm.exe → Copy file
- %AppDataLocal%\{GUID}\sdel.exe → Copy file
- %AppDataLocal%\{GUID}\sdel64.exe → Copy file
- %AppDataLocal%\{GUID}\session.tmp → Copy file
- %AppDataLocal%\{GUID}\Defender.exe → Copy file
- {All affected directories}\Bigspermhorseballs_Decryption.txt
- %UserTemp%\session.tmp
- %UserTemp%\{Random Letters}.{Random Letters}.ps1 → It Deletes after
- %UserTemp%\{Random Letters}.{Random Letters}.psm1 → It Deletes after
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- "%UserTemp%\7ZipSfx.000\7za.exe" x -y -p23980242011156913804 Everything64.dll
- "%UserTemp%\7ZipSfx.000\7za.exe" i
- cmd.exe /c DC.exe /D
- "%AppDataLocal%\{GUID}Defender.exe"
- "%AppDataLocal%\{GUID}Defender.exe" -e watch -pid {PID of Defender.exe} -!
- "%AppDataLocal%\{GUID}Defender.exe" -e ul1
- "%AppDataLocal%\{GUID}Defender.exe" -e ul2
- "%Program Files%\Everything\Everything.exe" -startup
- powercfg.exe -H off
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 1} {GUID Group} {GUID Setting 1} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 1} {GUID Group} {GUID Setting 2} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 1} {GUID Group} {GUID Setting 3} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 1} {GUID Group} {GUID Setting 1} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 1} {GUID Group} {GUID Setting 2} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 1} {GUID Group} {GUID Setting 3} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 2} {GUID Group} {GUID Setting 1} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 2} {GUID Group} {GUID Setting 2} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 2} {GUID Group} {GUID Setting 3} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 2} {GUID Group} {GUID Setting 1} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 2} {GUID Group} {GUID Setting 2} 0"
- "powercfg.exe -SETACVALUEINDEX {Power scheme GUID 2} {GUID Group} {GUID Setting 3} 0"
- "powercfg.exe -S {Power scheme GUID 1}"
- "powercfg.exe -S {Power scheme GUID 2}"
- "powershell.exe -ExecutionPolicy Bypass ""Get-VM | Stop-VM"""
- "powershell.exe -ExecutionPolicy Bypass ""Get-VM | Select-Object vmid | Get-VHD | %{Get-DiskImage -ImagePath $_.Path; Get-DiskImage -ImagePath $_.ParentPath} | Dismount-DiskImage"""
- "powershell.exe -ExecutionPolicy Bypass ""Get-Volume | Get-DiskImage | Dismount-DiskImage"""
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000(32-bit), Server 2003(32-bit), XP, Vista(64-bit), 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit) , or C:\Program Files (x86) in Windows XP(64-bit), Vista(64-bit), 7(64-bit), 8(64-bit), 8.1(64-bit), 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It creates the following folders:
- %AppDataLocal%\{GUID}
- %System Root%\temp
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).. %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- oooiheWoeohohLeooho
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
Defender = %AppDataLocal%\{GUID}\Defender.exe
Other System Modifications
This Ransomware modifies the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\VSS
Start = 4
(Note: The default value data of the said registry entry is 3.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\SDRSVC
Start = 4
(Note: The default value data of the said registry entry is 3.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\wbengine
Start = 4
(Note: The default value data of the said registry entry is 3.)
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Control\FileSystem
LongPathEnabled = 1
(Note: The default value data of the said registry entry is 0.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
DataCollection
AllowTelemetry = 0
(Note: The default value data of the said registry entry is 3.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
ConsentPromptBehaviorAdmin = 0
(Note: The default value data of the said registry entry is 5.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
ConsentPromptBehaviorAdmin = 0
(Note: The default value data of the said registry entry is 3.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
PromptOnSecureDesktop = 0
(Note: The default value data of the said registry entry is 1.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLUA = 0
(Note: The default value data of the said registry entry is 1.)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
shutdownwithoutlogon = 0
(Note: The default value data of the said registry entry is 1.)
It deletes the following registry entries:
HKEY_CURRENT_USER\Software\Policies\
Microsoft\Windows
System = DisableCMD
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows
System = DisableCMD
Process Termination
This Ransomware terminates the following services if found on the affected system:
- AcronisAgent
- ARSM
- backup
- BackupExecAgentAccelerator
- BackupExecAgentBrowser
- BackupExerDiveciMediaService
- BackupExecJobEngine
- BackupExecManagementService
- BackupExecRPCService
- BackupExecVSSProvider
- CASAD2DWebSvc
- ccEvtMgr
- ccSetMgr
- Culserver
- dbeng8
- dbsrv12
- DefWatch
- FishbowlMySQL
- GxBlr
- GxCIMgr
- GxCUD
- GxFWD
- GxVss
- memtas
- mepocs
- msexchange
- MSExchange$
- msftesql-Exchange
- msmdsrv
- MSSQL
- MSSQL$
- MSSQL$KAV_CS_ADMIN_KIT
- MSSQL$MICROSOFT##SSEE
- MSSQL$MICROSOFT##WID
- MSSQL$SBMONITORING
- MSSQL$SHAREPOINT
- MSSQL$VEAMSQL2012
- MSSQLFDLauncher$SBSMONITORING
- MSSQLFDLauncher$SHAREPOINT
- MSSQLServerADHelper100
- MVArmor
- MVarmor64
- svc$
- sophos
- RTVscan
- MySQL57
- PDVFSService
- QBCFMonitorService
- QBFCService
- QBIDService
- QBVSS
- SavRoam
- SQL
- SQLADHLP
- sqlagent
- SQLAgent$KAV_CS_ADMIN_KIT
- SQLAgent$SBSMONITORING
- SQLAgent$SHAREPOINT
- SQLAgent$VEEAMSQL2012
- sqlbrowser
- SqlServr
- SQLWriter
- stc_raw_agent
- tomcat6
- veeam
- VeeamDeploymentService
- VeamNFSSvc
- vmware-converter
- vmware-usbarbitator64
- VSNAPVSS
- vss
- wrapper
- WSBExchange
- YooBackup
- YooIT
It terminates the following processes if found running in the affected system's memory:
- agentsvc.exe
- AutodeskDesktopApp.exe
- axlbridge.exe
- bedbh.exe
- benetns.exe
- bengien.exe
- beserver.exe
- CoreSync.exe
- Creative Cloud.exe
- dbeng50.exe
- dbsnmp.exe
- encsvc.exe
- EnterpriseClient.exe
- fbguard.exe
- fbserver.exe
- fdhost.exe
- fdlauncher.exe
- httpd.exe
- isqlplussvc.exe
- msaccess.exe
- MsDtSrvr.exe
- msftesql.exe
- mspub.exe
- mydesktopqos.exe
- mydesktopservice.exe
- mysqld.exe
- mysqld-nt.exe
- mysqld-opt.exe
- ocautoupds.exe
- ocomm.exe
- ocssd.exe
- oracle.exe
- pvlsvr.exe
- node.exe
- java.exe
- python.exe
- wpython.exe
- QBDBMgr.exe
- QBDBMgrN.exe
- QBIDService.exe
- qbupdate.exe
- QBW32.exe
- QBW64.exe
- Raccine.exe
- Raccine_x86.exe
- RaccineElevatedCfg.exe
- RaccineSettings.exe
- VeeamDeploymentSvc.exe
- RAgui.exe
- raw_agent_svc.exe
- SimplyConnectionManager.exe
- sqbcoreservice.exe
- sql.exe
- sqlagent.exe
- sqlbrowser.exe
- sqlmangr.exe
- sqlservr.exe
- sqlwriter.exe
- Ssms.exe
- Sysmon.exe
- Sysmon64.exe
- tbirdconfig.exe
- tomcat6.exe
- vsnapvss.exe
- vxmon.exe
- wdswfsafe.exe
- wsa_service.exe
- wxServer.exe
- wxServerView.exe
- xfssvccon.exe
Other Details
This Ransomware adds the following registry keys:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion
Image File Execution Options = {list of processes to be terminated}
HKEY_LOCAL_MACHINE\SOFTWARE
Classes = mimicfile
HKEY_LOCAL_MACHINE\SOFTWARE
Classes = .bigspermhorseballs
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
HidePowerOptions = 1
HKEY_CURRENT_USER\Software\Policies\
Microsoft\Windows\CurrentVersion\
Policies\Explorer
HidePowerOptions = 1
HKEY_CURRENT_USER\Software\Policies\
Microsoft\Windows\CurrentVersion\
Policies\Explorer
NoClose = 1
HKEY_CURRENT_USER\Software\Policies\
Microsoft\Windows\CurrentVersion\
Policies\Explorer
StartMenuLogOff = 1
It requires the following additional components to properly run:
- Everything32.dll
- Everything64.dll
It does the following:
- Activating anti-kill measures
- Activating anti-shutdown measures
- Bypassing User Account Control (UAC)
- Collecting system information
- Creating persistence via the RUN key
- Disabling Windows Defender
- Disabling Windows Telemetry
- Disabling sleep mode and shutdown of the system
- Inhibiting System Recovery
- Removing Indicators
- Terminating processes and services
- Unmounting Virtual Drives
It accepts the following parameters:
- -dir → directory for encryption
- -e all → encrypt all (default)
- -e Local → encrypt local files
- -e net → encrypt files on network shares
- -e watch
- -e ul1 → unlock certain memory addresses from another process
- -e ul2 → unlock certain memory addresses from another process
- -prot → protects the ransomware from being killed
- -pid → process identifier (PID) of the previously-running ransomware.
Ransomware Routine
This Ransomware encrypts files with the following extensions:
- sql
- sqlite
- sqlite3
- sqlitedb
- mdf
- mdb
- adb
- db
- db3
- dbf
- dbs
- udb
- dbv
- dbx
- edb
- exb
- 1cd
- fdb
- idb
- mpd
- myd
- odb
- xls
- xlsx
- doc
- docx
- bac
- bak
- back
- zip
- rar
- dt
It avoids encrypting files with the following strings in their file name:
- restore-my-files.txt
- boot.ini
- bootfont.bin
- desktop.ini
- iconcache.db
- io.sys
- ntdetect.com
- ntldr
- ntuser.dat
- ntuser.ini
- thumbs.db
- session.tmp
- Bigspermhorseballs_Decryption.txt
- Defender.exe
It avoids encrypting files with the following strings in their file path:
- steamapps
- Cache
- Boot
- Chrome
- Firefox
- Mozilla
- Mozilla Firefox
- Microsoft Edge
- Internet Explorer
- Tor Browser
- Opera
- Opera Software
- Common Files
- Config
- Msi
- Intel
- Microsoft
- Microsoft Shared
- Microsoft.NET
- MSBuild
- MSOCache
- Packages
- PerfLogs
- ProgramData
- System Volume Information
- tmp
- Temp
- USOShared
- Windows
- Windows Defender
- Windows Journal
- Windows NT
- Windows Photo Viewer
- Windows Security
- Windows.old
- WindowsApps
- WindowsPowerShell
- WINNIT
- $WINDOWS.~BT
- $Windows.~WS
- %Public%
- %AppDataLocal%\{GUID}
(Note: %Public% is the folder that serves as a repository of files or folders common to all users, which is usually C:\Users\Public in Windows Vista, 7, and 8.. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It appends the following extension to the file name of the encrypted files:
- .bigspermhorseballs
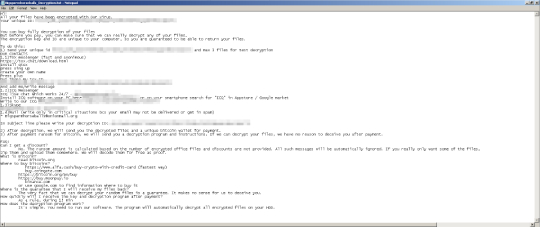
It drops the following file(s) as ransom note:
- Bigspermhorseballs_Decryption.txt
It avoids encrypting files with the following file extensions:
- bigspermhorseballs
- efi
- mui
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FSX031
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE
- Classes = mimicfile
- Classes = mimicfile
- In HKEY_LOCAL_MACHINE\SOFTWARE
- Classes = .bigspermhorseballs
- Classes = .bigspermhorseballs
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\{all entries ending in .exe}
- Debugger = %System%\Systray.exe
- Debugger = %System%\Systray.exe
- In In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer
- HidePowerOptions = 1
- HidePowerOptions = 1
- In In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
- HidePowerOptions = 1
- HidePowerOptions = 1
- In In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
- NoClose = 1
- NoClose = 1
- In In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
- StartMenuLogOff = 1
- StartMenuLogOff = 1
Step 6
Search and delete these folders
- %AppDataLocal%\{GUID}
- %System Root%\temp
Step 7
Search and delete these files
- %User Temp%\7ZipSfx.000\7za.exe
- %User Temp%\7ZipSfx.000\Everything.exe
- %User Temp%\7ZipSfx.000\Everything32.dll
- %User Temp%\7ZipSfx.000\Everything64.dll
- %User Temp%\7ZipSfx.000\Everything.ini
- %User Temp%\7ZipSfx.000\Everything2.ini
- %User Temp%\7ZipSfx.000\Horsesperm.exe
- %User Temp%\7ZipSfx.000\sdel.exe
- %User Temp%\7ZipSfx.000\sdel64.exe
- %User Temp%\7ZipSfx.000\session.tmp
- %User Temp%\7ZipSfx.000\Defender.exe
- %AppDataLocal%\{GUID}\7za.exe
- %AppDataLocal%\{GUID}\Everything.exe
- %AppDataLocal%\{GUID}\Everything32.dll
- %AppDataLocal%\{GUID}\Everything64.dll
- %AppDataLocal%\{GUID}\Everything.ini
- %AppDataLocal%\{GUID}\Everything2.ini
- %AppDataLocal%\{GUID}\Horsesperm.exe
- %AppDataLocal%\{GUID}\sdel.exe
- %AppDataLocal%\{GUID}\sdel64.exe
- %AppDataLocal%\{GUID}\session.tmp
- %AppDataLocal%\{GUID}\Defender.exe
- {All affected directories}\Bigspermhorseballs_Decryption.txt
- %UserTemp%\session.tmp
Step 8
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this only if you know how to or you can seek your system administrator’s help. You may also check out this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS
- Start = 4 (Change to default value: 3)
- Start = 4 (Change to default value: 3)
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\SDRSVC
- Start = 4 (Change to default value: 3)
- Start = 4 (Change to default value: 3)
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\wbengine
- Start = 4 (Change to default value: 3)
- Start = 4 (Change to default value: 3)
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\FileSystem
- LongPathEnabled = 1 (Change to default value: 0)
- LongPathEnabled = 1 (Change to default value: 0)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\DataCollection
- AllowTelemetry = 0 (Change to default value: 3)
- AllowTelemetry = 0 (Change to default value: 3)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- ConsentPromptBehaviorAdmin = 0 (Change to default value: 5)
- ConsentPromptBehaviorAdmin = 0 (Change to default value: 5)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- ConsentPromptBehaviorAdmin = 0 (Change to default value: 3)
- ConsentPromptBehaviorAdmin = 0 (Change to default value: 3)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- PromptOnSecureDesktop = 0 (Change to default value: 1)
- PromptOnSecureDesktop = 0 (Change to default value: 1)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLUA = 0 (Change to default value: 1)
- EnableLUA = 0 (Change to default value: 1)
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- shutdownwithoutlogon = 0 (Change to default value: 1)
- shutdownwithoutlogon = 0 (Change to default value: 1)
Step 9
Restore these deleted registry keys/values from backup
*Note: Only Microsoft-related keys/values will be restored. If the malware/grayware also deleted registry keys/values related to programs that are not from Microsoft, please reinstall those programs on your computer.
- In In HKEY_CURRENT_USER\Software\Policies\Microsoft\Windows
- System = DisableCMD
- System = DisableCMD
- In In HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows
- System = DisableCMD
- System = DisableCMD
Step 10
Restore encrypted files from backup.
Step 11
Scan your computer with your Trend Micro product to clean files detected as Ransom.Win32.MIMIC.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 12
Scan your computer with your Trend Micro product to delete files detected as Ransom.Win32.MIMIC.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


