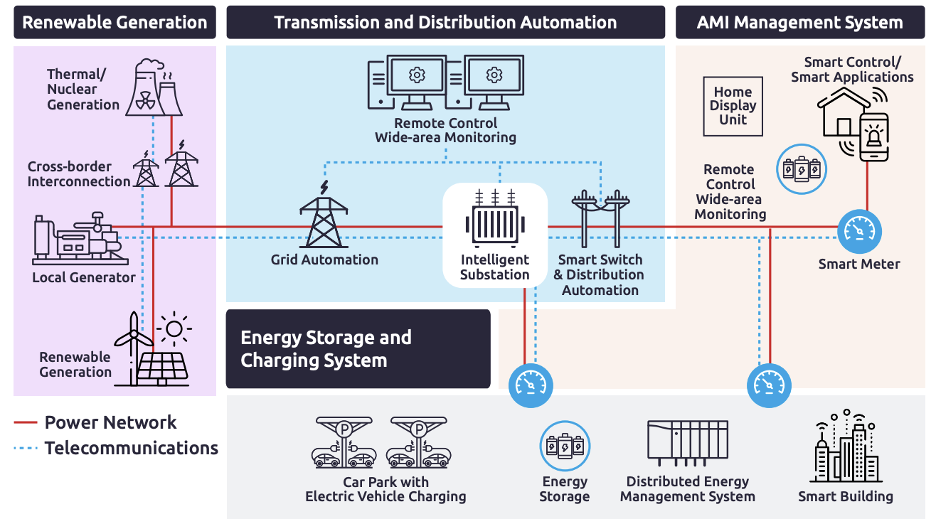
As the need for reliable and affordable energy sources grows, countries worldwide are increasingly turning to smart grids. Smart grids revolutionize how society accesses energy, enabling higher efficiency, reliability, and cost-effective management of energy resources. But these advancements come with a risk—smart grid infrastructures are highly vulnerable to cyberattacks, leading to costly consequences if left unprotected.
Drawing on the Achieving Energy Transformation: Building a Cyber Resilient Smart Grid
Report released on April 2023 from TXOne Networks, a Trend Micro's affiliated company dedicated to OT security. This blog will discuss key vulnerabilities in smart grids. It also discusses the associated cybersecurity standards and countermeasures that must be taken to protect this vital infrastructure from malicious activities.
Smart Grid Vulnerabilities
Today’s smart grids face several vulnerabilities related to devices, communication networks, and system operations. Here are some of the vulnerabilities highlighted in the paper:
Renewable power generation
Renewable power generation, such as wind and solar, plays a critical role in the smart grid, but they also introduce new vulnerabilities that attackers can exploit. The following are some of the vulnerabilities associated with renewable power generation:
- Vulnerabilities in Wind Power Control Equipment: Wind turbines are controlled by industrial control systems that may have vulnerabilities that attackers can exploit. For example, attackers could manipulate the control systems to change the output of the wind turbines, causing imbalances in the grid and potentially leading to blackouts.
- Vulnerabilities in Solar Power Generation: Solar power generation systems also rely on industrial control systems, which may have vulnerabilities that attackers can exploit. For example, attackers could manipulate the control systems to cause the solar panels to overproduce or underproduce energy, causing imbalances in the grid.
Distribution Automation (DA) and Feeder Automation (FA)
These are critical components of the smart grid that automate power distribution from the substation to customers. However, they are also vulnerable to attacks due to the following reasons:
- Insecure Industrial Control Protocols: DA and FA systems use industrial control protocols that may not have security features, making them vulnerable to attacks. For example, attackers could use unauthenticated commands to manipulate the DA and FA systems, causing power outages or other disruptions.
- Risk of Remote Service Vulnerabilities: Many DA and FA systems are connected to remote services, such as cloud-based applications, which can be vulnerable to attacks. Attackers could exploit vulnerabilities in these remote services to gain access to the DA and FA systems and cause disruptions.
Energy Storage System Management
It is an essential component of the smart grid that enables the storage of excess energy from renewable sources for later use. However, they are also vulnerable to attacks due to the following reasons:
- Insecure Communication Protocols: Energy storage systems use communication protocols to communicate with other smart grid components. These protocols may not have security features, making them vulnerable to attacks. For example, attackers could intercept the communication between the energy storage system and other smart grid components, leading to unauthorized access or control of the system.
- Physical Security Risks: Energy storage systems may be located in remote or unsecured locations, making them vulnerable to physical attacks. Attackers could damage or destroy the energy storage systems, leading to power outages or other disruptions.
Advanced Metering Infrastructure (AMI) Management System
This is another critical component of the smart grid that enables collecting and transmitting energy usage data from smart meters to utilities. However, they are also vulnerable to attacks due to the following reasons:
- Insecure Communication Protocols: AMI systems use communication protocols to transmit data between smart meters and utilities. These protocols may not have security features, making them vulnerable to attacks. For example, attackers could intercept the communication between the smart meters and utilities, leading to unauthorized access or control of the system.
- Unauthorized Access: AMI systems may be accessible to unauthorized personnel, making them vulnerable to attacks. Attackers could gain physical access to the AMI systems and tamper with the smart meters or the data collected by the system.
Addressing these vulnerabilities is crucial for the resilience and security of the smart grid. Implementing robust cybersecurity measures can significantly mitigate these vulnerabilities and safeguard against cyber threats.
NERC CIP Standards
There are multiple standards and regulations involved in smart grid security, and this blog picked up NERC-CIP as a representative example. NERC CIP Standards is mandatory for electric utilities in North America; these standards protect the bulk power system against cyber threats with requirements for risk assessment, access controls, incident response, and vulnerability assessments.
Here are some NERC CIP Standards:
| Number | Title | Effective date of Standard |
| CIP-002-5.1a | BES Cyber System Categorization | 12/27/2016 |
| CIP-003-8 | Security Management Controls | 4/1/2020 |
| CIP-004-6 | Personnel & Training | 7/1/2016 |
| CIP-005-7 | Electronic Security Perimeter(s) | 10/1/2022 |
| CIP-006-6 | Physical Security of BES Cyber Systems | 7/1/2016 |
| CIP-007-6 | System Security Management | 7/1/2016 |
| CIP-008-6 | Incident Reporting and Response Planning | 1/1/2021 |
| CIP-009-6 | Recovery Plans for BES Cyber Systems | 7/1/2016 |
| CIP-010-4 | Configuration Change Management and Vulnerability Assessments | 10/1/2022 |
| CIP-011-2 | Information Protection | 7/1/2016 |
| CIP-012-1 | Communication Between Control Centers | 7/1/2022 |
| CIP-013-2 | Supply Chain Risk Management | 10/1/2022 |
| CIP-014-3 | Physical Security | 6/16/2022 |
Not all of these apply to renewable energy, but they are baselines of cybersecurity for electric utilities. Some examples of cyber hygiene with reference to this are described below.
- Implementing robust authentication and access controls: This includes strong passwords, multi-factor authentication, and limiting access privileges to only authorized personnel to prevent unauthorized access to smart grid systems.
- Regularly updating and patching software and systems: This helps to address known vulnerabilities and protect against known exploits. Keeping all software, firmware, and systems up-to-date with the latest security patches and updates is essential.
- Conducting regular security assessments and audits: This includes vulnerability assessments, penetration testing, and security audits to identify and address any potential weaknesses or vulnerabilities in the smart grid infrastructure.
- Establishing incident response plans: A well-defined plan helps quickly detect, respond to, and mitigate cybersecurity incidents or breaches in smart grid systems.
- Implementing network segmentation and isolation: This helps to limit the potential impact of a cybersecurity breach by isolating critical systems and minimizing lateral movement within the network.
- Encrypting communication and data: Encrypting data in transit and at rest helps to protect against unauthorized access and data breaches. Encryption should be implemented for communication between devices, networks, and systems in the smart grid infrastructure.
- Training and educating personnel: Providing regular training and education to employees and stakeholders involved in the operation and maintenance of the smart grid systems helps to raise awareness about cybersecurity best practices and the importance of adhering to cybersecurity policies and procedures.
- Implementing backup and disaster recovery plans: Regular backups of critical data and systems, and a well-defined disaster recovery plan in place, helps to quickly recover from any cybersecurity incident or system failure.
Countermeasures
In addition, safeguarding smart grids and other critical infrastructure from cyber threats requires a proactive and comprehensive approach to cybersecurity. Zero Trust principles can significantly enhance the cybersecurity posture of Operational Technology (OT) environments, such as those found in smart grids.
Zero Trust for OT involves implementing stringent access controls, continuous monitoring, and authentication mechanisms to ensure the highest level of security for OT networks. By adopting a Zero Trust approach, organizations can minimize the risk of unauthorized access, lateral movement within the network, and other cyber threats, ultimately protecting the integrity, availability, and confidentiality of OT systems.
Trend Micro offers a range of solutions that can expand cybersecurity capabilities between IT and OT environments. Our expertise in securing both IT and OT environments allows for a holistic approach to cybersecurity, addressing vulnerabilities across the entire smart grid ecosystem. You can watch a video explaining the journey from OT Zero Trust to cross-domain XDR here.
With innovative solutions, organizations can implement robust authentication and access controls, conduct continuous monitoring and auditing, and establish incident response plans to effectively safeguard OT networks from cyber threats.
To learn more about achieving energy transformation and building a cyber-resilient smart grid, refer to the full report by TXOne Networks, "Achieving Energy Transformation: Building a Cyber-Resilient Smart Grid."