JS_FBJACK.C
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This malware spreads via the Facebook chat feature. It entices users to click a link by saying that it leads to an execution video of Osama bin Laden.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
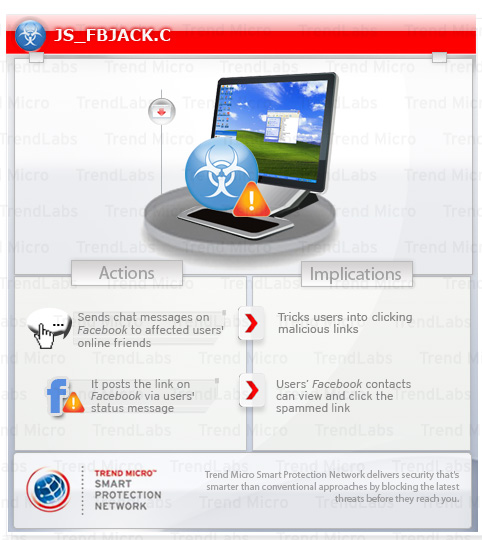
This malicious JavaScript sends an instant message to an affected user's online friends. It also posts a message on the affected user's Facebook Wall. It entices users to click the link contained in posted messages by using the news of Osama bin Laden's death.
TECHNICAL DETAILS
Arrival Details
This Trojan may be downloaded from the following remote sites:
- http://{BLOCKED}0.85.172/bl.js
Other Details
This Trojan connects to the following possibly malicious URL:
- http://{BLOCKED}ount.info/end.php
NOTES:
This malicious JavaScript is part of a Facebook spam campaign that spreads via the said website's chat feature. The said spam campaign uses the news of Osama bin Laden's death.
It sends the following chat message to affected user's online friends:
- "See the Osama Bin Laden EXECUTION Video! http://{BLOCKED}p.com/805u7p? "
This will leave you speechless
Osama Bin Laden EXECUTION Video!
http://{BLOCKED}ly.ws/e4lqeg?
Navy Seals raid Bin Ladens hideout and execute him!
http://{BLOCKED}dssz.co.cc/laden.png
- http://{BLOCKED}p.com/805u7p?
- http://{BLOCKED}ly.ws/e4lqeg
- http://{BLOCKED}ount.info/end.php
- http://{BLOCKED}dssz.co.cc/laden.png
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as JS_FBJACK.C. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


