Spam Emails Deliver Malware Via Password-Protected Google Drive, Google Docs Archives
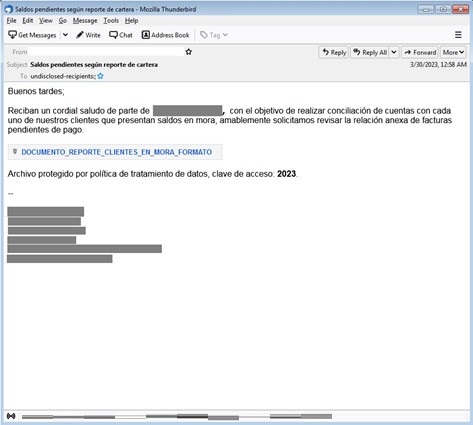
Recently, we observed spam emails that
targeted users in Latin America. The emails, which were written in Spanish, informed
victims about an outstanding balance or a pending payment. The emails contain
Google Drive or Google Docs URLs that have the “export=download” parameter,
which will automatically initiate the downloading of the malicious file once
the victim selects the link.
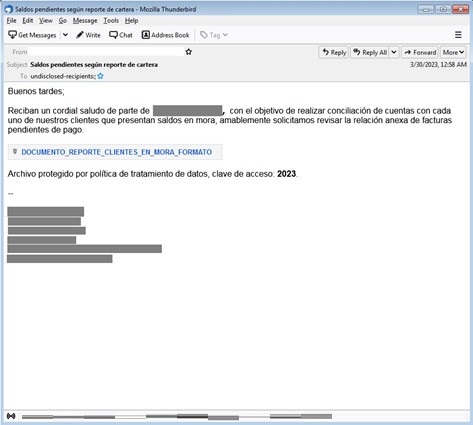
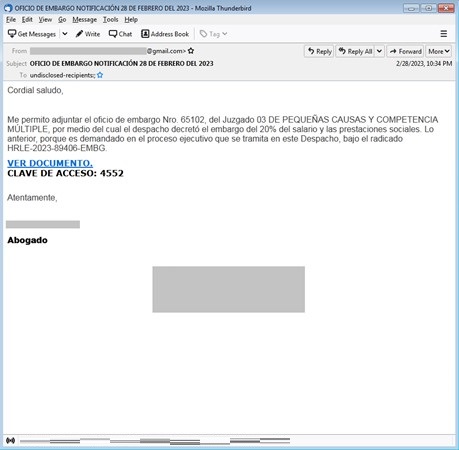
The downloaded file is a password-protected archive, which is a common tactic that malicious actors use for detection evasion purposes. The attackers provide the password for the password-protected archive in the email copy.
A variety of threats have been delivered in this campaign, including REMCOS, and ASYNCRAT, which can give attackers unauthorized access to a victim's machine.
These
spam emails are already blocked by Trend Micro Email Security solutions. To
remain protected against malware-laden spam campaigns, users should avoid downloading
and opening files that come from unfamiliar senders.
The following URLs automatically download password-protected files to victim machines:
- hxxps[://]docs[.]google[.]com/uc?export=download&id=1wCjfcFW07h52cYbq444tGXFcrRsHZWLU
- hxxps[://]docs[.]google[.]com/uc?export=download&id=1yKA5HQq8HdOnutz9ngHXKWqE5oaEvytK
- hxxps[://]docs[.]google[.]com/uc?export=download&id=1yP3k2sumYo0UhFtuN6BGhH1XT7fIXCBZ
- hxxps[://]docs[.]google[.]com/uc?export=download&id=1CjztaC5-91V3jPBZXBYX9wCH5eNbVVSk
- hxxps[://]docs[.]google[.]com/uc?export=download&id=1Cb2tUlplO2UrmIy428mNIAP8UYUyGfic
- hxxps[://]docs[.]google[.]com/uc?export=download&id=1HMXnq5M6Qxwn-XDuZ1u92N8cmoWMAFL-
- hxxps[://]drive[.]google[.]com/uc?id=1Mi99157eA5aC4kpdY8Egdbad_GA3Uq0f&export=download&authuser=0
- hxxps[://]drive[.]google[.]com/uc?id=18yTuJ-NMh4O0rjyOU9fOx0dXT8514Kzn&export=download&authuser=0
- hxxps[://]drive[.]google[.]com/uc?id=1sJCcU38cLgUgXu4-FYjOjAkSbH45N0qY&export=download&authuser=0
- ENGINE:9.0.1004
- PATTERN:2.7544.000
