WORM_MORCUT.A
Worm:Win32/Boychi.A (Microsoft), W32.Crisis (Symantec), Trojan-Dropper.Win32.Injector.fleh (Kaspersky)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm has the ability to mount to virtual disks. Doing so infects virtual environments that are set up on Windows operating systems.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
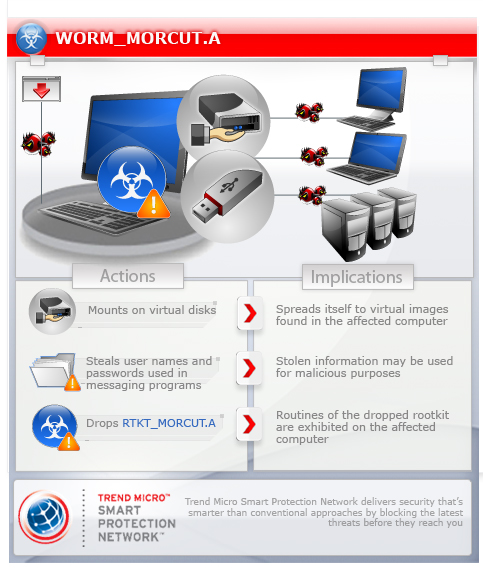
This worm finds VMware-related files on the affected computer and attempts to spread using the virtual disks found. It also spreads by dropping copies of itself in removable drives.
It steals user names and passwords used in messaging applications.
This worm may be dropped by other malware.
TECHNICAL DETAILS
Arrival Details
This worm may be dropped by the following malware:
- JAVA_MORCUT.A
Installation
This worm drops the following component file(s):
- %User Profile%\Local Settings\jlc3V7we\IZsROY7X.-MP - also detected by Trend Micro as WORM_MORCUT.A
- %User Profile%\Local Settings\jlc3V7we\t2HBeaM5.OUk - detected by Trend Micro as WORM64_MORCUT.A
- %User Profile%\Local Settings\jlc3V7we\WeP1xpBU.wA- - detected by Trend Micro as RTKT_MORCUT.A
- %User Profile%\Local Settings\jlc3V7we\6EaqyFfo.zIK - detected by Trend Micro as RTKT64_MORCUT.A
- %System%\drivers\ndisk.sys - detected by Trend Micro as either RTKT_MORCUT.A or RTKT64_MORCUT.A
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.. %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
It drops the following non-malicious files:
- %User Profile%\Local Settings\jlc3V7we\lUnsA3Ci.Bz7
- %User Profile%\Local Settings\jlc3V7we\eiYNz1gd.Cfp - configuration file
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.)
It creates the following folders:
- %User Profile%\Local Settings\jlc3V7we
(Note: %User Profile% is the current user's profile folder, which is usually C:\Windows\Profiles\{user name} on Windows 98 and ME, C:\WINNT\Profiles\{user name} on Windows NT, and C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003.)
It injects threads into the following normal process(es):
- Explorer.exe
Autostart Technique
This worm adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
*J7PugHy = "%System%\rundll32.exe "%User Profile%\Local Settings\jlc3V7we\IZsROY7X.-MP",F1dd208"
It registers its dropped component as a system service to ensure its automatic execution at every system startup. It does this by creating the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ndisk.sys
Type = "1"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ndisk.sys
Start = "1"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ndisk.sys
ErrorControl = "0"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ndisk.sys
ImagePath = "\??\%System%\drivers\ndisk.sys"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ndisk.sys
DisplayName = "ndisk.sys"
It registers its dropped component as a system service to ensure its automatic execution at every system startup. It does this by creating the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ndisk.sys
NOTES:
This worm reads the file %User Profile%\Application Data\VMWare\preferences.ini to get the list of VMware virtual machines the user uses. It then searches for the VMware virtual disk files associated with each virtual machine found. It then mounts each virtual machine one at a time as drive Z, and drops the following copies of itself:
- Z:\ProgramData\Microsoft\WIndows\Start Menu\Programs\Startup\{random file name}
- Z:\Documents and Settings\All Users\Start Menu\Programs\Startup\{random file name}
It checks drive D to drive Z for removable drives. For each removable drive found, it creates the following folder and drops a DESKTOP.INI file in it:
- {removable drive letter}:\Recycler
It drops the following copy of itself:
- {removable drive letter}:\Recycler\S-1-5-21-4125489612-33920608401-12510794-1000\mWgpX-al.exe
It also drops an AUTORUN.INF which contains the following strings:
[Autorun]
Action=Open folder to view files
Icon=%systemroot%\system32\shell32.dll,4
Shellexecute=.\Recycler\
S-1-5-21-4125489612-33920608401-12510794-1000\mWgpX-al.exe
It steals user names and password from the following applications and services:
- Google Talk
- Microsoft Outlook 2003
- Microsoft Outlook 2010
- MSN Messenger 7.0
- Opera
- Outlook Express
- Paltalk
- ThunderBird
- Windows Live Mail
- Windows Live Messenger
It has the ability to rename the files {malware path}\wmcore.001 and {malware path}\wmcore.002 to {malware path}\r5qCUwK0.Mi8 and {malware path}\Low_IHDm.fbT, respectively. It then copies the file {malware path}\r5qCUwK0.Mi8 to a connected Windows CE device as \{first folder}\2577\autorun.exe. It also copies {malware path}\Low_IHDm.fbT to the Windows CE device as \{first folder}\2577\autorun.zoo. It then executes the copied \{first folder}\2577\autorun.exe.
This worm is also capable of the following routines:
- Capture screenshots
- Get clipboard contents
- Get the following system information:
- Disk (free and total size)
- Locale Settings
- Memory (free and total size)
- OS Registration
- OS Version
- Processor
- Log keystrokes
- Monitor VOIP calls
- Record audio from the PC microphone
- Take pictures using the computer's webcam
It sends the information gathers to {BLOCKED}.{BLOCKED}.100.37.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 4
Restart in Safe Mode
Step 5
Search and delete this folder
- %User Profile%\Local Settings\jlc3V7we
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- ndisk.sys
- ndisk.sys
Step 7
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- *J7PugHy = "%System%\rundll32.exe "%User Profile%\Local Settings\jlc3V7we\IZsROY7X.-MP",F1dd208"
- *J7PugHy = "%System%\rundll32.exe "%User Profile%\Local Settings\jlc3V7we\IZsROY7X.-MP",F1dd208"
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_MORCUT.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


