WORM_KELIHOS.SM
Backdoor:Win32/Kelihos.A (Microsoft); W32.Waledac.B (Symantec)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm uses social engineering methods to lure users into performing certain actions that may, directly or indirectly, cause malicious routines to be performed. Specifically, it makes use of spam messages disguised as electronic greeting cards.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
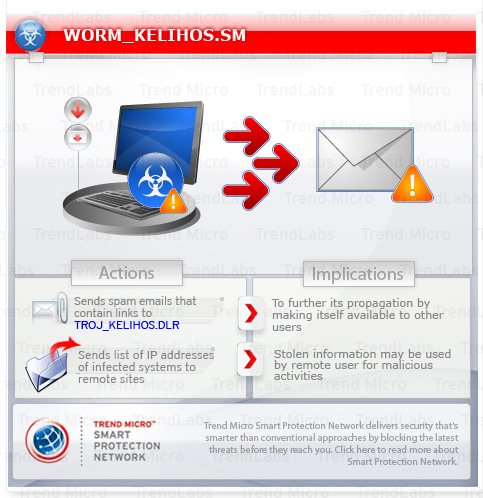
This worm sends out spam emails which contain links to TROJ_KELIHOS.DLR. It may also be downloaded from remote sites by other malware.
When executed, it connects to other computers infected with this worm through TCP port 80. It then gets the list of IP addresses the remote computer has logged and adds them to the list of IP addresses it connects to. It sends a list of IP addresses of infected systems once it receives remote connection via the same port.
This worm also executes with the parameter <i>/loggs99</i> to log its activities. It then saves its log file onto the infected system.
This worm may be downloaded from remote sites by other malware.
TECHNICAL DETAILS
Arrival Details
This worm may be downloaded from remote site(s) by the following malware:
- TROJ_KELIHOS.DLR
It may be downloaded from the following remote sites:
- http://{BLOCKED}.240.36/flash2.exe
Installation
This worm creates the following folders:
- %System Root%\All Users\Application Data\boost_interprocess
- %System Root%\All Users\Application Data\boost_interprocess\{current date and time}
(Note: %System Root% is the root folder, which is usually C:\. It is also where the operating system is located.)
Autostart Technique
This worm adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
SmartIndex = {malware path and file name}
Other System Modifications
This worm adds the following registry keys:
HKEY_CURRENT_USER\Software\Google
It adds the following registry entries:
HKEY_CURRENT_USER\Software\Google
ID = 50
HKEY_CURRENT_USER\Software\Google
ID2 = {random values}
HKEY_CURRENT_USER\Software\Google
ID3 = {random values}
HKEY_CURRENT_USER\Software\Google
AppID = {random characters}
Backdoor Routine
This worm opens the following port(s) where it listens for remote commands:
- TCP port 1508
- TCP port 1541
- TCP port 80
Other Details
This worm does the following:
- Sends out spam e-mails which contain links to TROJ_KELIHOS.DLR. This Trojan, in turn, downloads WORM_KELIHOS.SM.
Note, however, that the binaries downloaded from the link may change depending on what infected machine they are retrieved, which changes.
It sends a GET request to the server to download an encrypted data, which contains information on its spamming routine.
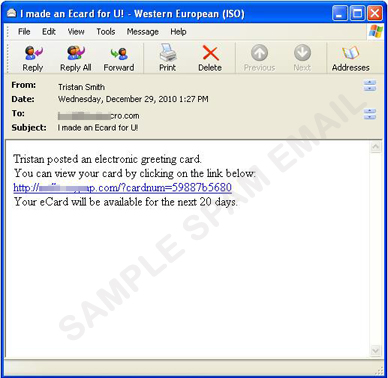
The email it sends has the following format:
From: {name of sender}
Subject: {subject}
Message Body:
{name of sender} {message 1} {message 2}
{message 3}
{malicious link}Some samples bear the following details:
{name of sender}:
- Abraham
- Adalbert
- Baldwin
- Barbara
- Candida
- Carol
- Daniel
- Dannie
- Eddie
- Edgar
- Fanny
- Felicia
- Gabriel
- Geffrey
- Hadrian
- Hannah
- Irene
- Isaac
- Jacob
- James
- Katharine
- Kathleen
- Lambert
- Laura
- Mabel
- Madeleine
- Nance
- Nancy
- Odette
- Olive
- Paddy
- Patricia
- Rachel
- Ralph
- Sadie
- Sally
- Teddy
- Terry
- Valentine
- Veronica
- Wallace
- Walter
{subject}:
- Happy 2011!
- You've got a Happy New Year Greeting Card!
- I made an Ecard for U!
- Enjoy the New Year!
- Wishing you the Best New Year!
{message 1} can be any of the following:
- just mailed to you
- wants to show you
- has created for you
{message 2} can be any of the following:
- a postcard.
- an ecard.
- an electronic New Year greeting card.
- a digital postcard.
- a New Year ECard.
- an Online greeting card.
{message 3} can be any of the following:
- Click on the link below to see your greeting card:
- Collect your E-card here:
- It is waiting for you at our card site, go ahead and see it!
- To pick up your greeting card, click on the following link at anytime within the next 30 days:
- To view the ecard simply click the link below:
{malicious link} can be any link where TROJ_KELIHOS.DLR can be downloaded.
It displays information on its activities when it is executed with the parameter /loggs99. Below is a screenshot of the said log:
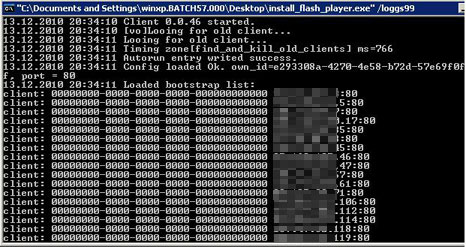
- Executes with the parameter /loggs99 to log its activities. It then drops its log file at {malware path and file name}.LOG.
- Communicates peer-to-peer (P2P) mechanism by connecting to other computers infected with this malware through TCP port 80. This type of communication is usually referred to as HTTP2P. It then gets the list of IP addresses the remote computer has logged and adds them to the list of IP addresses it connects to.
- Sends list of IP addresses of infected systems once it receives remote connection via TCP port 80
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 3
Identify and terminate files detected as WORM_KELIHOS.SM
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- SmartIndex={malware path and file name}
- SmartIndex={malware path and file name}
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software
- Google
- Google
Step 6
Search and delete this folder
- %System Root%\All Users\Application Data\boost_interprocess
Step 7
Scan your computer with your Trend Micro product to delete files detected as WORM_KELIHOS.SM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


