TSPY_FAREIT.YOI
PWS:Win32/Fareit.gen!E(Microsoft); Trojan-PSW.Win32.Tepfer.uytm(Kaspersky); MSIL/Injector.IOX(ESET)
Windows


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware is related to CryptoWall 3.0 attacks seen in March 2015.
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
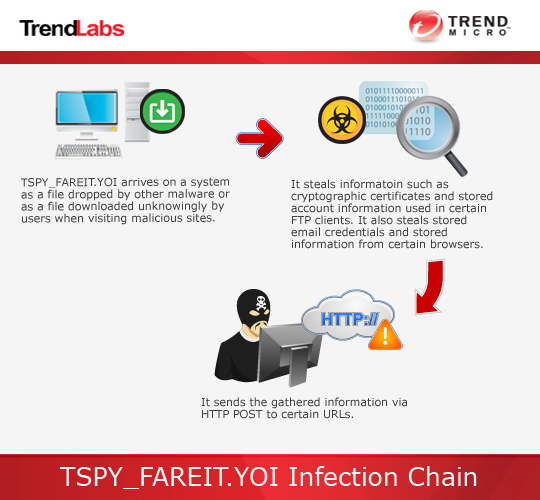
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes then deletes itself afterward.
TECHNICAL DETAILS
Arrival Details
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This spyware drops the following files:
- %User Temp%\{7 random numbers}.bat
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It adds the following processes:
- cmd.exe (uses the dropped .bat file)
It executes then deletes itself afterward.
Other System Modifications
This spyware adds the following registry entries as part of its installation routine:
HKEY_CURRENT_USER\Software\WinRAR
HWID = "{GUID}"
HKEY_CURRENT_USER\Software\WinRAR
Client Hash = "{Random Value}"
Information Theft
This spyware gathers the following data:
- Cryptographic certificates
It attempts to steal stored account information used in the following installed File Transfer Protocol (FTP) clients or file manager software:
- Far Manager
- Total Commander
- WS_FTP
- GlobalSCAPE CuteFTP 6 Home
- GlobalSCAPE CuteFTP 6 Professional
- GlobalSCAPE CuteFTP 7 Home
- GlobalSCAPE CuteFTP 7 Professional
- GlobalSCAPE CuteFTP 8 Home
- GlobalSCAPE CuteFTP 8 Professional
- GlobalSCAPE CuteFTP
- GlobalSCAPE CuteFTP Pro
- GlobalSCAPE CuteFTP Lite
- FlashFXP
- FileZilla
- FTP Navigator
- FTP Commander
- BulletProof FTP
- SmartFTP
- TurboFTP
- CoreFTP
- FTP Explorer
- UltraFXP
- FTPRush
- BitKinex
- Frigate3
- WebSitePublisher
- SecureFX
- ExpanDrive
- FFFTP
- ClassicFTP
- Fling FTP
- SoftX FTPClient
- Directory Opus
- LeapFTP
- 32BitFtp
- WebDrive
- Wise-FTP
- FTPVoyager
- FireFTP
- LeechFTP
- WinFTP
- FTPGetter
- ALFTP
- DeluxeFTP
- Epic
- Staff-FTP
- FreshFTP
- BlazeFT
- GoFTP
- 3D-FTP
- EasyFTP
- NetSarang
- FTPNow
- Robo-FTP
- LinasFTP
- CyberDuck
- PuTTY
- NppFTP
- CoffeeCup Software
- FTPShell
- MAS-Soft FTPInfo
- NexusFile
- WinZip
- NovaFTP
- Odin Secure FTP Expert
It gathers the following account information from any of the mentioned File Transfer Protocol (FTP) clients or file manager software:
- Username
- Password
- User ID
- Host Address
- Directory List
- Port Number
- Terminal Type
- Server Name
- Server Type
It attempts to steal stored email credentials from the following:
- Windows Live Mail
- Windows Mail
- Pocomail
- Incredimail
- BatMail
- The Bat!
- Internet Account Manager
- Microsoft Outlook
- Thunderbird
- FastTrack
- Windows Live Mail
- Windows Mail
- Pocomail
- Incredimail
- BatMail
- The Bat!
- Internet Account Manager
- Microsoft Outlook
- Thunderbird
- FastTrack
It attempts to get stored information such as user names, passwords, and hostnames from the following browsers:
- Opera
- Mozilla
- SeaMonkey
- Internet Explorer
- Google Chrome
- Chromium
- ChromePlus
- Bromium
- Nichrome
- Comodo
- RockMelt
- K-Meleon
- FastStone
- Yandex
- Flock
It uses the following list of user names and passwords to access password-protected locations where the mentioned information is stored:
- samantha
- michelle
- david
- eminem
- scooter
- asdfasdf
- sammy
- baby
- diamond
- maxwell
- 55555
- justin
- james
- chicken
- danielle
- iloveyou2
- fuckoff
- prince
- junior
- rainbow
- 112233
- fuckyou1
- 1
- nintendo
- peanut
- none
- church
- bubbles
- robert
- 222222
- destiny
- loving
- gfhjkm
- mylove
- jasper
- hallo
- 123321
- cocacola
- helpme
- nicole
- guitar
- billgates
- looking
- scooby
- joseph
- genesis
- forum
- emmanuel
- cassie
- victory
- passw0rd
- foobar
- ilovegod
- nathan
- blabla
- digital
- peaches
- football1
- 11111111
- power
- thunder
- gateway
- iloveyou!
- football
- tigger
- corvette
- angel
- killer
- creative
- 123456789
- zxcvbnm
- startrek
- ashley
- cheese
- a
- sunshine
- christ
- 000000
- soccer
- qwerty1
- friend
- summer
- 1234567
- merlin
- phpbb
- 12345678
- jordan
- saved
- dexter
- viper
- winner
- sparky
- windows
- 123abc
- lucky
- anthony
- jesus
- ghbdtn
- admin
- hotdog
- baseball
- password1
- dragon
- trustno1
- jason
- internet
- mustdie
- john
- letmein
- 123
- mike
- knight
- jordan23
- abc123
- red123
- praise
- freedom
- jesus1
- 12345
- london
- computer
- microsoft
- muffin
- qwert
- mother
- master
- 111111
- qazwsx
- samuel
- canada
- slayer
- rachel
- onelove
- qwerty
- prayer
- iloveyou1
- whatever
- god
- password
- blessing
- snoopy
- 1q2w3e4r
- cookie
- 11111
- chelsea
- pokemon
- hahaha
- aaaaaa
- hardcore
- shadow
- welcome
- mustang
- 654321
- bailey
- blahblah
- matrix
- jessica
- stella
- benjamin
- testing
- secret
- trinity
- richard
- peace
- shalom
- monkey
- iloveyou
- thomas
- blink182
- jasmine
- purple
- test
- angels
- grace
- hello
- poop
- blessed
- 1234567890
- heaven
- hunter
- pepper
- john316
- cool
- buster
- andrew
- faith
- ginger
- 7777777
- hockey
- hello1
- angel1
- superman
- enter
- daniel
- 123123
- forever
- nothing
- dakota
- kitten
- asdf
- 1111
- banana
- gates
- flower
- taylor
- lovely
- hannah
- princess
- compaq
- jennifer
- myspace1
- smokey
- matthew
- harley
- rotimi
- fuckyou
- soccer1
- 123456
- single
- joshua
- green
- 123qwe
- starwars
- love
- silver
- austin
- michael
- amanda
- 1234
- charlie
- bandit
- chris
- happy
- hope
- maggie
- maverick
- online
- spirit
- george
- friends
- dallas
- adidas
- 1q2w3e
- 7777
- orange
- testtest
- asshole
- apple
- biteme
- 666666
- william
- mickey
- asdfgh
- wisdom
- batman
- pass
Stolen Information
This spyware sends the gathered information via HTTP POST to the following URL:
- http://{BLOCKED}amap.com/administrator/lib/cheapoakley.php
- http://{BLOCKED}leds.com/upload/images/images.php
- http://{BLOCKED}old.com/img/t/t.php
- http://www.{BLOCKED}e.mx/wp-includes/images/images.php
- http://www.{BLOCKED}w.nl/wp-includes/pomo/pomo.php
- http://www.{BLOCKED}ved.nl/wp-content/themes/themes.php
- http://www.{BLOCKED}osting.nl/wp-includes/theme-compat/ips_kernel.php
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\WinRAR
- HWID = "{GUID}"
- HWID = "{GUID}"
- In HKEY_CURRENT_USER\Software\WinRAR
- Client Hash = "{Random Value}"
- Client Hash = "{Random Value}"
Step 4
Search and delete these files
- %User Temp%\{7 random numbers}.bat
Step 5
Scan your computer with your Trend Micro product to delete files detected as TSPY_FAREIT.YOI. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


