TSPY_CHISBURG.A
HackTool:Win32/Mailpassview (Microsoft), a variant of Win32/Injector.Autoit.ZQ trojan (Eset), Troj/AutoIt-AAT (Sophos)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware uses an AutoIT packer, a scripting language leveraged by cybercriminals. It has the capability to propagate via drives and steals user names and passwords from Yahoo, Hotmail, and Pidgin among others.
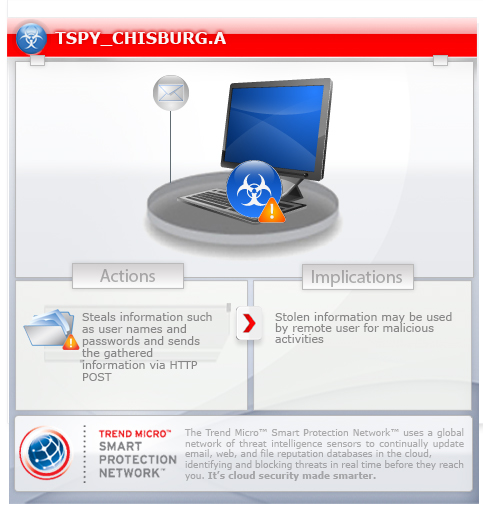
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
This spyware arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
TECHNICAL DETAILS
Arrival Details
This spyware arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
Installation
This spyware drops the following files:
- %User Temp%\{10 random alphanumeric characters}.ini
- %User Profile%\Xp21237W81223\{random filename and extension}
- %User Profile%\Mf88749K80827.WV7
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.. %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It drops the following copies of itself into the affected system:
- %User Profile%\Xp21237W81223\explorer.exe
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It creates the following folders:
- %User Profile%\Xp21237W81223
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
Autostart Technique
This spyware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\RunOnce
Ic98367G37760 = "%User Profile%\Xp21237W81223\explorer.exe"
Propagation
This spyware drops copies of itself in the following drives:
- {drive letter}:\explorer.exe - All drives
Stolen Information
This spyware sends the gathered information via HTTP POST to the following URL:
- http://{BLOCKED}ber123.hostingsiteforfree.com/index.php?action=add&username={username}&password={password}&app={application}&pcname={computername}&sitename={url of credentials}
NOTES:
It steals user names and passwords from the following:
- Internet Download Manager
- jDownloader
- VPN/ISP Credentials
- Trillian Messenger
- Yahoo
- Hotmail
- Pidgin
- FileZilla
- Registry/website/application defined in %User Temp%\{10 random alphanumeric characters}.ini
It sleeps for approximately 15 seconds when there's a running AvastUI.exe application.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- Ic98367G37760 = "%User Profile%\Xp21237W81223\explorer.exe"
- Ic98367G37760 = "%User Profile%\Xp21237W81223\explorer.exe"
Step 3
Search and delete these folders
- %User Profile%\Xp21237W81223
Step 4
Search and delete these files
- %User Temp%\{10 random alphanumeric characters}.ini
- %User Profile%\Mf88749K80827.WV7
Step 5
Scan your computer with your Trend Micro product to delete files detected as TSPY_CHISBURG.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



