TROJ_YAKES.AO
Trojan Horse (Symantec); TrojanDownloader:Win32/Razle.A (Microsoft); Trojan.Win32.Yakes.bnu (Kaspersky); Mal/Zbot-ASK (Sophos)
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This malware is part of a malware spam campaign. It stops most of its malicious routines if certain processes are found running on the system.
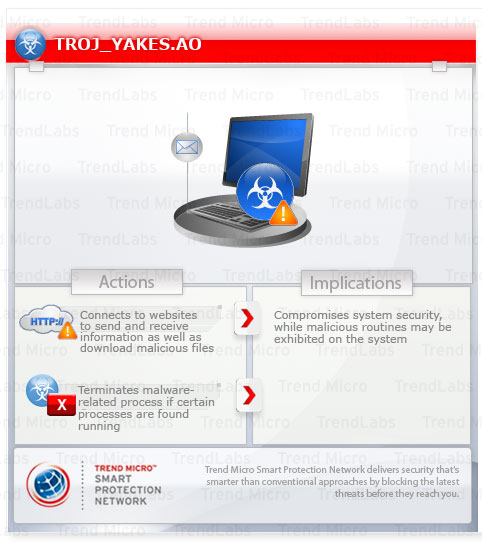
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan does not continue with its routine under certain conditions. It injects codes into its created process SVCHOST.EXE.
It may connect to a certain URL to report system infection and download possibly malicious files.
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It connects to certain websites to send and receive information. It deletes itself after execution.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
Installation
This Trojan adds the following processes:
- svchost.exe
Other Details
This Trojan connects to the following website to send and receive information:
- http://{BLOCKED}6.{BLOCKED}6.103.207/las/index.php
It deletes itself after execution.
NOTES:
It does not continue with its routine under the following conditions:
- The process WIRESHARK.EXE is running in the affected system
- GetModuleHandle to the files pstorec.dll and SbieDll.dll is successful
- The value of "VideoBiosVersion"; under the registry
HKEY_LOCAL_MACHINE\HARDWARE\
contains any of the following strings:
DESCRIPTION\System- VIRTUALBOX
- QEMU
- VMWARE
- VBOX
- VIRTUAL
- WARE
- ARRAY
- QM00001
- 00000000000000000001
- The file name of the sample executed is any of the following:
- SAMPLE
- VX
- VIRUS
It injects codes into its created process SVCHOST.EXE.
It may connect to the abovementioned URL to report system infection and download possibly malicious files.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product to delete files detected as TROJ_YAKES.AO. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


