RANSOM_SOREBRECT.A
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This malware is a variant of the SOREBRECT malware that Trend Micro discovered on June 2017. It sports fileless, code-injecting capabilities. Users affected by this malware may find their critical documents and files encrypted and rendered useless.
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to certain websites to send and receive information. It deletes itself after execution. It gathers information and reports it to its servers.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
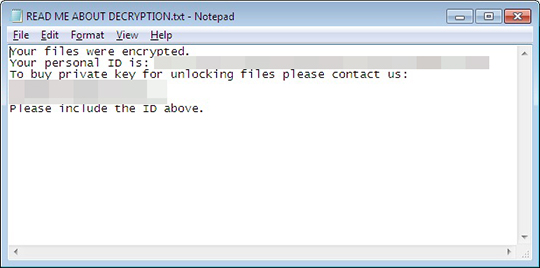
- {folder of encrypted files}\READ ME ABOUT DECRYPTION.txt ← ransom note
It adds the following processes:
- svchost.exe
It injects codes into the following process(es):
- svchost.exe
Other Details
This Ransomware connects to the following URL(s) to get the affected system's IP address:
- ipinfo.io
It connects to the following website to send and receive information:
- {BLOCKED}l7s7ynmazxwu.onion/gate.php
It renames encrypted files using the following names:
- {original filename}.pr0tect
It does the following:
- It avoids encrypting files in the following directories:
- Windows
- Desktop
- It terminates services with the following strings:
- AMS
- ARSM
- AcrSch2Svc
- Acronis
- AcronisAgent
- AcronisFS
- AcronisPXE
- AdobeARMservice
- Altaro.Agent.exe
- Altaro.HyperV.WAN.RemoteService.exe
- Altaro.SubAgent.exe
- Altaro.UI.Service.exe
- Apache2.2
- Apache2.4
- AutoDeploy
- Backup
- BackupExecAgentAccelerator
- BackupExecAgentBrowser
- BackupExecDeviceMediaService
- BackupExecJobEngine
- BackupExecManagementService
- BackupExecRPCService
- Browser
- Catalog
- CertPropSvc
- CertSvc
- CobianBackup11
- ComarchAutomatSynchronizacji
- ComarchML
- ComarchUpdateAgentService
- Connection
- CrashPlanService
- DLOAdminSvcu
- DLOMaintenanceSvc
- DataCollectorSvc
- DbxSvc
- DomainManagerProviderSvc
- EDBSRVR
- FBSServer
- FBSWorker
- FirebirdGuardianDefaultInstance
- FirebirdServerDefaultInstance
- GenetecSecurityCenterMobileServer
- GenetecServer
- GenetecWatchdog
- KAORCMP999467066507407
- LMIRfsDriver
- LogisticsServicesHost800
- MELCS
- MEMTAS
- MEPOCS
- MEPOPS
- MESMTPCS
- MICROMD72ONCOEMR
- MMS
- MSExchangeADTopology
- MSExchangeAntispamUpdate
- MSExchangeEdgeSync
- MSExchangeFBA
- MSExchangeFDS
- MSExchangeIS
- MSExchangeImap4
- MSExchangeMailSubmission
- MSExchangeMailboxAssistants
- MSExchangeMonitoring
- MSExchangePop3
- MSExchangeRep
- MSExchangeRepl
- MSExchangeSA
- MSExchangeSearch
- MSExchangeServiceHost
- MSExchangeTransport
- MSExchangeTransportLogSearch
- MSSQL$ACRONIS
- MSSQL$BKUPEXEC
- MSSQL$MICROSOFT##SSEE
- MSSQL$MICROSOFT##WID
- MSSQL$PROBA
- MSSQL$SBSMONITORING
- MSSQL$SHAREPOINT
- MSSQL$SQL2005
- MSSQL$SQLEXPRESS
- MSSQL$VEEAMSQL2008R2
- MSSQLFDLauncher
- MSSQLFDLauncher$PROBA
- MSSQLFDLauncher$SBSMONITORING
- MSSQLFDLauncher$SHAREPOINT
- MSSQLSERVER
- MSSQLSERVR
- MSSQLServerADHelper
- MSSQLServerADHelper100
- MSSQLServerOLAPService
- MicroMD
- MsDtsServer
- MsDtsServer100
- MySQL
- MySQL56
- NAVSERVER
- ONCOEMR2MICROMD7
- POP3
- PRIMAVERAWindowsService
- PleskControlPanel
- PleskSQLServer
- PopPassD
- PrimaveraWS800
- PrimaveraWS900
- Provider
- QBCFMonitorService
- QBFCService
- QBVSS
- QuickBooksDB23
- QuickBooksDB25
- RBMS_OptimaBI
- RBSS_OptimaBI
- RemoteSystemMonitorService
- Replication
- ReportServer
- SBOClientAgent
- SPAdminV4
- SPSearch4
- SPTimerV3
- SPTrace
- SPTraceV4
- SPWriter
- SPWriterV4
- SQLAgent$PROBA
- SQLAgent$SBSMONITORING
- SQLAgent$SHAREPOINT
- SQLAgent$SQLEXPRESS
- SQLAgent$VEEAMSQL2008R2
- SQLBrowser
- SQLSERVERAGENT
- SQLWriter
- Server
- ServerService
- Service
- ShadowProtectSvc
- StorageNode
- Sync
- TTESCheduleServer800
- TeamViewer
- VSNAPVSS
- VSS
- Veeam
- VeeamCatalogSvc
- VeeamCloudSvc
- VeeamDeploymentService
- VeeamMountSvc
- VeeamNFSSvc
- VeeamTransportSvc
- W32Time
- W3SVC
- WSS_ComputerBackupProviderSvc
- WSS_ComputerBackupSvc
- WSearch
- WinVNC4
- WseComputerBackupSvc
- WseEmailSvc
- WseHealthSvc
- WseMediaSvc
- WseMgmtSvc
- WseNtfSvc
- WseStorageSvc
- ZWCService
- bedbg
- cbVSCService11
- dashboardMD
- dbupdate
- dbupdatem
- eXchange
- memcached
- msftesql$SBSMONITORING
- msftesql-Exchange
- plesksrv
- postgresql-8.4
- sesvc
- spiceworks
- stc_raw_agent
- swprv
- vds
- vmicvss
- vmms
- wsbexchange
- zBackupAssistService
- It clears all Windows Event logs using the wevtutil.exe command.
- It uses TOR to secure its connection.
It deletes itself after execution.
It gathers the following information and reports it to its servers:
- Computer Name
- Username
- Malware path
- New infection
- Contents of auth.txt and info.txt.
NOTES:
This ransomware drops the following ransom note on all affected folders:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Restart in normal mode and scan your computer with your Trend Micro product for files detected as RANSOM_SOREBRECT.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 3
Search and delete this file
Step 4
Restore encrypted files from backup.
Did this description help? Tell us how we did.


