RANSOM_NECNE.TIBAFJ
Ransom:Win32/Necne (MICROSOFT); W32/GenKryptik.BUKT!tr (FORTINET)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It deletes itself after execution.
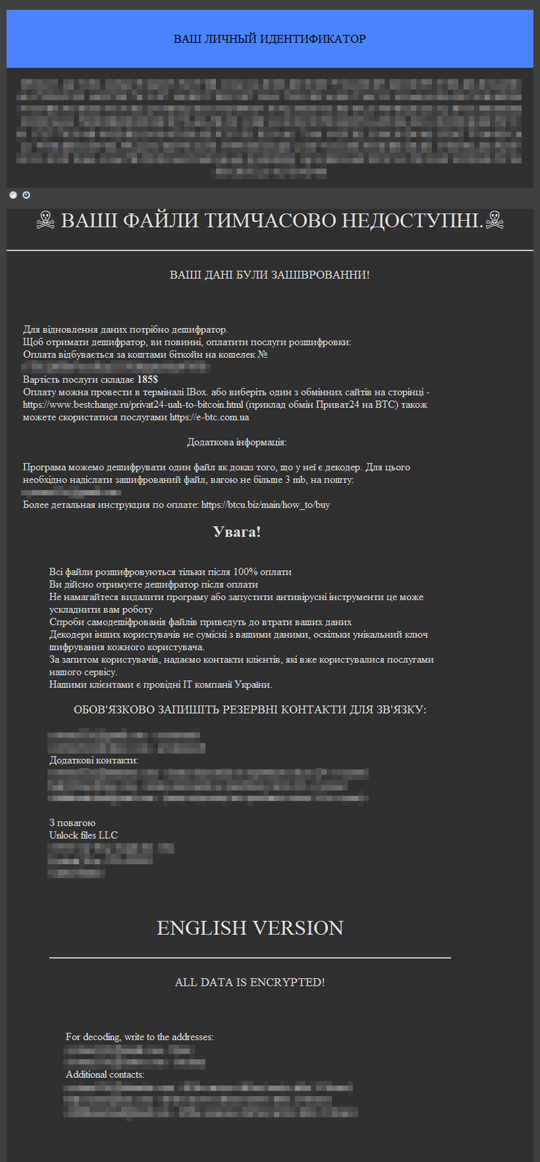
It drops files as ransom note.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following component file(s):
- %AppDataLocal%\tmp{random string}.tmp.bat <- deletes shadow copies
- C:\Users\Public\DCDEC2B5F7BCE854A7B279F522DF7535E368B319B6B8D31386F25A99C246C28F <- infection marker
(Note: %AppDataLocal% is the Application Data folder found in Local Settings, where it is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It drops the following copies of itself into the affected system:
- %AppDataLocal%\{malware name}.exe
(Note: %AppDataLocal% is the Application Data folder found in Local Settings, where it is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Other System Modifications
This Ransomware adds the following registry entries as part of its installation routine:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\RunOnce
BrowserUpdateCheck = %AppDataLocal%\{malware name}.exe
Other Details
This Ransomware does the following:
- Executes %AppDataLocal%\tmp{random string}.tmp.bat to delete shadow copies.
(Note: %AppDataLocal% is the Application Data folder found in Local Settings, where it is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It deletes itself after execution.
Ransomware Routine
This Ransomware avoids encrypting files found in the following folders:
- Windows
- Microsoft
- Microsoft Help
- Windows App Certification Kit
- Windows Defender
- COMODO
- Windows NT
- Windows Kits
- Windows Mail
- Windows Media Player
- Windows Multimedia Platform
- Windows Phone Kits
- Windows Phone Silverlight Kits
- Windows Photo Viewer
- Windows Portable Devices
- Windows Sidebar
- WindowsPowerShell
- NVIDIA Corporation
- Microsoft.NET
- Internet Explorer
- Kaspersky Lab
- McAfee
- Avira
- spytech software
- sysconfig
- Avast
- Dr.Web
- Symantec
- Symantec_Client_Security
- system volume information
- Microsoft Shared
- Common Files
- Outlook Express
- Movie Maker
- Chrome
- Mozilla Firefox
- Opera
- YandexBrowser
- ntldr
- ProgramData
It appends the following extension to the file name of the encrypted files:
- .lock
It drops the following file(s) as ransom note:
- {encrypted directory}\doc.html
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- BrowserUpdateCheck = %AppDataLocal%\{malware name}.exe
- BrowserUpdateCheck = %AppDataLocal%\{malware name}.exe
Step 5
Search and delete these files
- %AppDataLocal%\{malware name}.exe
- %AppDataLocal%\tmp{random string}.tmp.bat
- C:\Users\Public\DCDEC2B5F7BCE854A7B279F522DF7535E368B319B6B8D31386F25A99C246C28F
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as RANSOM_NECNE.TIBAFJ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 7
Restore encrypted files from backup.
Did this description help? Tell us how we did.


