Ransom.Win32.BLACKCAT.C
Win32/Filecoder.BlackCat.B (NOD32)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- %Temp%\{random numbers}.exe
- {Encrypted Directory}\checkpoints-{Encrypted File Name}.qgk5spt → deleted after file encryption
- %Desktop%\RECOVER-qgk5spt-FILES.txt.png
(Note: %Temp% is the Windows temporary folder, where it usually is C:\Windows\Temp on all Windows operating system versions.. %Desktop% is the current user's desktop, which is usually C:\Documents and Settings\{User Name}\Desktop on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\Desktop on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
It adds the following processes:
- "%System%\cmd.exe" /c "reg add HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\109887672622700698813643583812537429462 /d Service"
- "%System%\cmd.exe" /c "bcdedit /set {current} safeboot minimal"
- {Malware File Name} --safeboot-instance --access-token {ACCESS_TOKEN} --prop-arg-safeboot --no-net --no-prop --no-impers --prop-file \"{Malware File Path}\{Malware File Name}\"
- "%System%\cmd.exe" /c "%User Temp%\{random numbers}.exe --safeboot-instance --access-token {ACCESS_TOKEN} --prop-arg-safeboot --no-net --no-prop --no-impers --prop-file \"{Malware File Path}\{Malware File Name}\" --prop-file \"{Malware File Path}\{Malware File Name}\""
- %User Temp%\{random numbers}.exe --safeboot-instance --access-token {ACCESS_TOKEN} --prop-arg-safeboot --no-net --no-prop --no-impers --prop-file \"{Malware File Path}\{Malware File Name}\" --prop-file \"{Malware File Path}\{Malware File Name}\"
- "%System%\cmd.exe" /c "iisreset.exe /stop"
- "%System%\cmd.exe" /c "reg add HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters /v MaxMpxCt /d 65535 /t REG_DWORD /f"
- "%System%\cmd.exe" /c "vssadmin.exe Delete Shadows /all /quiet"
- "%System%\cmd.exe" /c "arp -a"
- "%System%\cmd.exe" /c "wmic.exe Shadowcopy Delete"
- "%System%\cmd.exe" /c "wevtutil.exe el"
- "%System%\cmd.exe" /c "wevutil.exe cl \"{Windows Event Logs}"
- "%System%\cmd.exe" /c "bcdedit /set {default} recoveryenabled No"
- "%System%\cmd.exe" /c "bcdedit /set {current} safeboot network"
- "%System%\cmd.exe" /c "bcdedit /deletevalue {current} safeboot"
- "%System%\cmd.exe" /c "fsutil behavior set SymlinkEvaluation R2L:1"
- "%System%\cmd.exe" /c "fsutil behavior set SymlinkEvaluation R2R:1"
- wmic csproduct get UUID
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000(32-bit), XP, and Server 2003(32-bit), or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit).)
Autostart Technique
This Ransomware registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Control\SafeBoot\Minimal\
109887672622700698813643583812537429462
(Default) = Service
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\LanmanServer\Parameters
MaxMpxCt = 65535
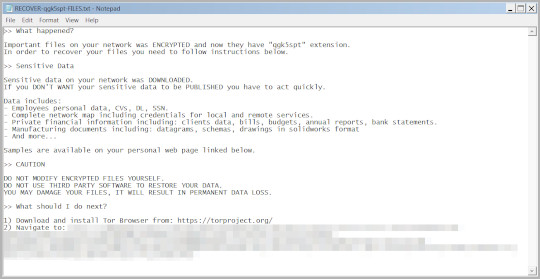
It sets the system's desktop wallpaper to the following image:
- %Desktop%\RECOVER-qgk5spt-FILES.txt.png

Process Termination
This Ransomware terminates the following services if found on the affected system:
- mepocs
- memtas
- veeam
- svc$
- backup
- sql
- vss
- msexchange
- sql$
- mysql
- mysql$
- sophos
- MSExchange
- MSExchange$
- WSBExchange
- PDVFSService
- BackupExecVSSProvider
- BackupExecAgentAccelerator
- BackupExecAgentBrowser
- BackupExecDiveciMediaService
- BackupExecJobEngine
- BackupExecManagementService
- BackupExecRPCService
- GxBlr
- GxVss
- GxClMgrS
- GxCVD
- GxCIMgr
- GXMMM
- GxVssHWProv
- GxFWD
- SAPService
- SAP
- SAP$
- SAPD$
- SAPHostControl
- SAPHostExec
- QBCFMonitorService
- QBDBMgrN
- QBIDPService
- AcronisAgent
- VeeamNFSSvc
- VeeamDeploymentService
- VeeamTransportSvc
- MVArmor
- MVarmor64
- VSNAPVSS
- AcrSch2Svc
It terminates the following processes if found running in the affected system's memory:
- agntsvc
- dbeng50
- dbsnmp
- encsvc
- excel
- firefox
- infopath
- isqlplussvc
- msaccess
- mspub
- mydesktopqos
- mydesktopservice
- notepad
- ocautoupds
- ocomm
- ocssd
- onenote
- oracle
- outlook
- powerpnt
- sqbcoreservice
- sql
- steam
- synctime
- tbirdconfig
- thebat
- thunderbird
- visio
- winword
- wordpad
- xfssvccon
- *sql*
- bedbh
- vxmon
- benetns
- bengien
- pvlsvr
- beserver
- raw_agent_svc
- vsnapvss
- CagService
- QBIDPService
- QBDBMgrN
- QBCFMonitorService
- SAP
- TeamViewer_Service
- TeamViewer
- tv_w32
- tv_x64
- CVMountd
- cvd
- cvfwd
- CVODS
- saphostexec
- saposcol
- sapstartsrv
- avagent
- avscc
- DellSystemDetect
- EnterpriseClient
- VeeamNFSSvc
- VeeamTransportSvc
- VeeamDeploymentSvc
Other Details
This Ransomware does the following:
- It requires being executed with the following arguments to proceed with its encryption routine:
- --access-token {ACCESS_TOKEN} --safeboot
- It clears Windows event logs.
- It terminates ESXi VMs.
- It uses PsExec to propagate.
- It creates a pipe named:
- \.\pipe\__rust_anonymous_pipe1__.{Process ID}.{random characters}
It accepts the following parameters:
- --access-token → Access Token
- --bypass → Dummy
- --child → Run as child process
- --drag-and-drop → Invoked with drag and drop
- --drop-drag-and-drop-target → Drop drag and drop target batch file
- --log-file → Enable logging to specified file
- --no-impers → Do not spawn impersonated processes on Windows
- --no-net → Do not discover network shares on Windows
- --no-prop → Do not self propagate (worm) on Windows
- --no-prop-servers → Do not propagate to defined servers
- --no-vm-kill → Do not stop VMs on ESXi
- --no-vm-killnames → Do not stop defined VMs on ESXi
- --no-vm-snapshot-kill → Do not wipe VMs snapshots on ESXi
- --no-wall → Do not update desktop wallpaper on Windows
- -p, --path → Only process files inside defined paths
- --prop-file → Propagate specified file
- --propagate → Run as propagated process
- --safeboot → Reboot in Safe Mode before running on Windows
- --safeboot-instance → Run as safeboot instance on Windows
- --safeboot-network → Reboot in Safe Mode with Networking before running on Windows
- --sleep-restart → Sleep for duration in seconds after successful run and then restart. (This is soft persistence, keeps process alive no longer then defined in --sleep-restart-duration, 24 hours by default)
- --sleep-restart-duration → Keep soft persistence alive for duration in seconds. (24 hours by default)
- --sleep-restart-until → Keep soft persistence alive until defined UTC time in millis. (Defaults to 24 hours since launch)
- --ui → Show user interface
- --elevated → Run as elevated process
- --verbose → Log to console
- --extra-verbose → Log more to console (Also forces process to run in attached mode)
- --safeboot-entry → Safemode Reboot Callback
- -h, --help → Print help information
- --prop-arg-safeboot
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- desktop.ini
- autorun.inf
- ntldr
- bootsect.bak
- thumbs.db
- boot.ini
- ntuser.dat
- iconcache.db
- bootfont.bin
- ntuser.ini
- ntuser.dat.log
It avoids encrypting files found in the following folders:
- system volume information
- $windows.~ws
- $recycle.bin
- $windows.~bt
- msocache
- windows
- default
- all users
- tor browser
- boot
- config.msi
- perflogs
- windows.old
It appends the following extension to the file name of the encrypted files:
- .qgk5spt
It drops the following file(s) as ransom note:
- %Desktop%\RECOVER-qgk5spt-FILES.txt
- {Encrypted Directory}\RECOVER-qgk5spt-FILES.txt
It avoids encrypting files with the following file extensions:
- themepack
- nls
- diagpkg
- msi
- lnk
- exe
- cab
- scr
- bat
- drv
- rtp
- msp
- prf
- msc
- ico
- key
- ocx
- diagcab
- diagcfg
- pdb
- wpx
- hlp
- icns
- rom
- dll
- msstyles
- mod
- ps1
- ics
- hta
- bin
- cmd
- ani
- 386
- lock
- cur
- idx
- sys
- com
- deskthemepack
- shs
- ldf
- theme
- mpa
- nomedia
- spl
- cpl
- adv
- icl
- msu
SOLUTION
Step 1
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restart in Safe Mode
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\109887672622700698813643583812537429462
- (Default) = Service
- (Default) = Service
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters
- MaxMpxCt = 65535
- MaxMpxCt = 65535
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\109887672622700698813643583812537429462
Step 6
Search and delete this file
- %Temp%\{random numbers}.exe
- {Encrypted Directory}\checkpoints-{Encrypted File Name}.qgk5spt
- %Desktop%\RECOVER-qgk5spt-FILES.txt.png
- %Desktop%\RECOVER-qgk5spt-FILES.txt
- {Encrypted Directory}\RECOVER-qgk5spt-FILES.txt
Step 7
Reset your Desktop properties
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.BLACKCAT.C. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 9
Restore encrypted files from backup.
Step 10
Scan your computer with your Trend Micro product to delete files detected as Ransom.Win32.BLACKCAT.C. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


