PERL_EXPLOYT.PLK
Linux


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This is the detection for exploit codes that takes advantage of a vulnerability in the hosting control panel Plesk.
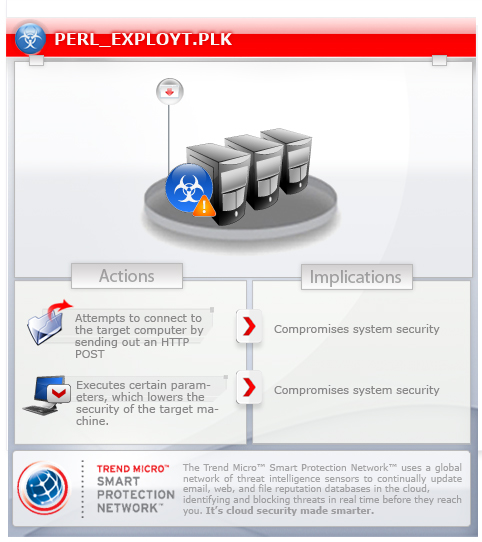
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This malware is a zero-day exploit that affects Plesk systems in Linux operating systems.
It attempts to connect to the target computer by sending out an HTTP POST. Allowing it to execute certain parameters lowers the security of the target machine.
TECHNICAL DETAILS
NOTES:
This malware uses the following parameters to execute:
%ScriptFile% [Target IP] [http|https] [Local IP] [Local Port]
The variables mentioned above are:
- [Target IP] - the IP address of the remote machine
- [http|https] - enables or disables SSL connection
- [Local IP] - IP address of the affected computer
- [Local Port] - port where the remote machine connects to
This malware attempts to connect to the target computer by sending out an HTTP POST. Allowing it to execute certain parameters lowers the security of the target machine.
It then sends a PHP script that enables remote shell using the data local IP and local port.
SOLUTION
Scan your computer with your Trend Micro product to delete files detected as PERL_EXPLOYT.PLK. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


