TROJ_RANSOM.QOWA
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan ransomware uses social engineering methods to lure users into performing certain actions that may, directly or indirectly, cause malicious routines to be performed. Specifically, it disables functionality of the compromised computer so that victims are forced to dial a premium-rate SMS number.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.

This ransomware consistently displays an image which users from accessing their desktops and applications. Users are then forced to provide the required ransom by dialing the premium-rate SMS number displayed on the screen.
This Trojan may be unknowingly downloaded by a user while visiting malicious websites.
It uses icons similar to those of legitimate applications to entice a user to click them.
TECHNICAL DETAILS
Arrival Details
This Trojan may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This Trojan drops the following copies of itself into the affected system:
- %System%\usrinit.exe
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
Autostart Technique
This Trojan modifies the following registry entries to ensure it automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
Userinit = %System%\userinit.exe,%System%\usrinit.exe
(Note: The default value data of the said registry entry is %System%\userinit.exe,.)
Propagation
This Trojan uses icons similar to those of legitimate applications to entice a user to click them.
Other Details
This Trojan does the following:
- Displays the following image in a consistent manner after this Trojan executes, preventing users from accessing their desktops and applications:
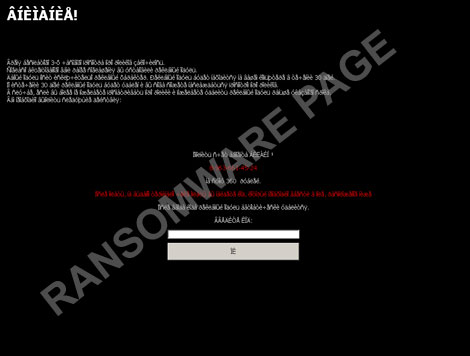
Users are then forced to provide the required "ransom" by dialing the premium-rate SMS number displayed on the screen.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Since this malware uses rootkit technology, detection and removal using normal and safe mode methods may not eliminate it completely. This procedure restarts the system using the Windows Recovery Console.
- Insert the Windows Installation CD into the CD drive, then Press the restart button.
- Upon prompt, press any key to boot from the CD.
- On the main menu, type r to go to the Recovery Console.
- Type the drive that contains Windows (usually C:) and press Enter.
- In the input box, type the following then press Enter:
del %System%\usrinit.exe - Type exit and press Enter to restart the system normally.
Step 3
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- From: Userinit = %System%\userinit.exe,%System%\usrinit.exe
To: Userinit = %System%\userinit.exe,
- From: Userinit = %System%\userinit.exe,%System%\usrinit.exe
Step 4
Scan your computer with your Trend Micro product to delete files detected as TROJ_RANSOM.QOWA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


