RANSOM_LECTOOL.A
Trojan-Ransom.Win32.Leshiy.a (Kaspersky), Win32/Filecoder.DX (ESET), RDN/Ransom (McAfee)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It connects to certain websites to send and receive information. It deletes the initially executed copy of itself. It gathers information and reports it to its servers.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following files:
- {Folder containing encrypted files}\_secret_code.txt - contains unique code per victim
- {Folder containing encrypted files}\_How to decrypt LeChiffre files.html - contains the ransom note
It drops the following copies of itself into the affected system:
- %Recycle Bin%\sunset.jpg
(Note: %Recycle Bin% is usually C:\Recycler on Windows XP and below, or C:\$Recycle.Bin on Windows Vista and above)
Other System Modifications
This Trojan modifies the following file(s):
- appends the extension .LeChiffre to the encrypted files
- replaces the file %System%\sethc.exe with %System%\cmd.exe
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.)
Other Details
This Trojan connects to the following website to send and receive information:
- http://{BLOCKED}.{BLOCKED}.251.146/sipvoice.php?insert=servername={computer name}&username={user name}&started={execution date}&secretcode={value}&email={creator's email}&session={session ID}&patched=
- http://{BLOCKED}.{BLOCKED}.251.146/sipvoice.php?updqua=&quantity={count of encrypted files}&session={session ID}
- http://{BLOCKED}.{BLOCKED}.251.146/sipvoice.php?update={value}&finished={value}&session={session ID}
- http://{BLOCKED}.{BLOCKED}.251.146/sipvoice.php?changecomment={value}&comment={value}&session={session ID}
- http://{BLOCKED}.{BLOCKED}.251.146/sipvoice.php?shutdown=&reason={value}&session={session ID}
It encrypts files with the following extensions:
- *.*crypt
- *.?db
- *.001
- *.1
- *.1cd
- *.2
- *.7z
- *.900
- *.accdb
- *.ai
- *.bak
- *.back
- *.bk?
- *.bk
- *.bmp
- *.cbf
- *.cdr
- *.cdx
- *.cer
- *.crt
- *.cf
- *.cfg
- *.cr2
- *.csv
- *.dat
- *.db?
- *.dd
- *.dmp
- *.doc
- *.docx
- *.dt
- *.efd
- *.epf
- *.eps
- *.erf
- *.ert
- *.evt
- *.ffdata
- *.fxp
- *.gbk
- *.glf
- *.gzip
- *.i01
- *.iar
- *.img
- *.iso
- *.jpeg
- *.jpg
- *.key
- *.lck
- *.ldf
- *.lgf
- *.lic
- *.license
- *.mb
- *.md?
- *.mokesi
- *.mxfd
- *.mxl
- *.odt
- *.pbd
- *.pf
- *.pfx
- *.png
- *.ppt
- *.psd
- *.pst
- *.rar
- *.rpt
- *.rtf
- *.sql*
- *.sdm
- *.tar
- *.tib
- *.tif
- *.tiff
- *.xlk
- *.xls
- *.xml
- *.xlsx
- *.zip
- *.zur
- *backup*
It deletes the initially executed copy of itself
It gathers the following information and reports it to its servers:
- computer name
- user name
- number of encrypted files
- malware's execution date
NOTES:
It queries the geographical location of the affected system by accessing the following site:
- http://api.sypexgeo.net/xml/
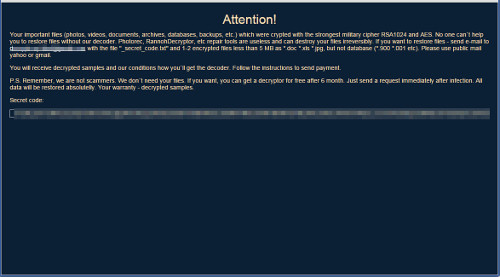
The dropped _How to decrypt LeChiffre files.html contains the following ransom note:
Once executed, this ransomware displays the following interface:
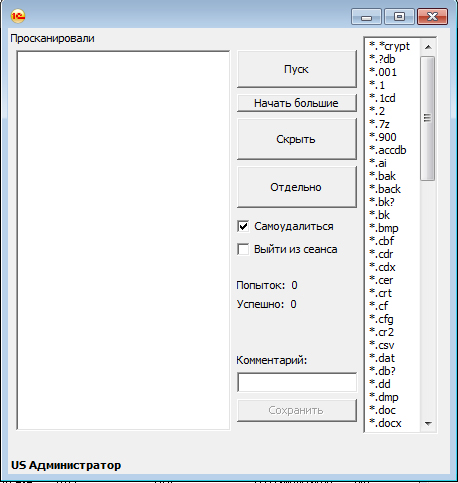
Encryption only starts when user clicks on the button пуск (English Translation: start).
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Identify and terminate files detected as RANSOM_LECTOOL.A
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 3
Search and delete this file
- {Folder containing encrypted files}\_secret_code.txt
- {Folder containing encrypted files}\_How to decrypt LeChiffre files.html
Step 4
Scan your computer with your Trend Micro product to delete files detected as RANSOM_LECTOOL.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 5
Restore this file from backup only Microsoft-related files will be restored. If this malware/grayware also deleted files related to programs that are not from Microsoft, please reinstall those programs on you computer again.
- %System%\sethc.exe
Step 6
Restore encrypted files from backup.
Did this description help? Tell us how we did.


