HKTL_COINMINE.GC
Tool.BtcMine.812 (DrWeb); Win64/BitCoinMiner.AP (ESET-NOD32); not-a-virus:RiskTool.Win64.BitCoinMiner.bcr (Kaspersky)
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Hacking Tool may arrive bundled with malware packages as a malware component. It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be manually installed by a user.
It does not have any propagation routine.
It does not have any backdoor routine.
It does not have any downloading capability.
TECHNICAL DETAILS
Arrival Details
This Hacking Tool may arrive bundled with malware packages as a malware component.
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be manually installed by a user.
Propagation
This Hacking Tool does not have any propagation routine.
Backdoor Routine
This Hacking Tool does not have any backdoor routine.
Download Routine
This Hacking Tool does not have any downloading capability.
Other Details
This Hacking Tool does the following:
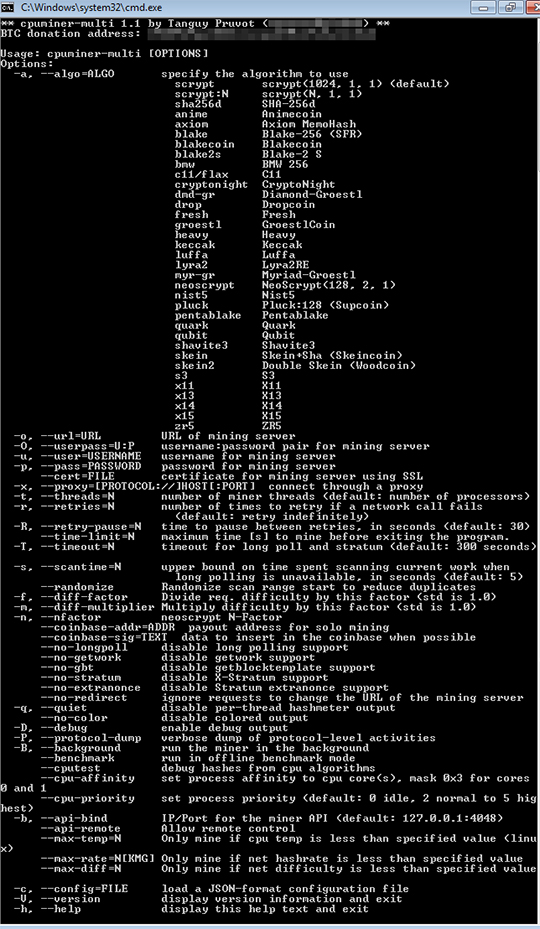
- This hacking tool accepts the following parameters:
- -a, --algo=ALGO -> specify the algorithm to use, where the user could choose from these algorithms:
- scrypt -> scrypt(1024, 1, 1) (default)
- scrypt:N -> scrypt(N, 1, 1)
- sha256d -> SHA-256d
- anime -> Animecoin
- axiom -> Axiom MemoHash
- blake -> Blake-256 (SFR)
- blakecoin -> Blakecoin
- blake2s -> Blake-2 S
- bmw -> BMW 256
- c11/flax -> C11
- cryptonight -> CryptoNight
- dmd-gr -> Diamond-Groestl
- drop -> Dropcoin
- fresh -> Fresh
- groestl -> GroestlCoin
- heavy -> Heavy
- keccak -> Keccak
- luffa -> Luffa
- lyra2 -> Lyra2RE
- myr-gr -> Myriad-Groestl
- neoscrypt -> NeoScrypt(128, 2, 1)
- nist5 -> Nist5
- pluck -> Pluck:128 (Supcoin)
- pentablake -> Pentablake
- quark -> Quark
- qubit -> Qubit
- shavite3 -> Shavite3
- skein -> Skein+Sha (Skeincoin)
- skein2 -> Double Skein (Woodcoin)
- s3 -> S3
- x11 -> X11
- x13 -> X13
- x14 -> X14
- x15 -> X15
- zr5 -> ZR5
- -o, --url=URL -> URL of mining server
- -O, --userpass=U:P -> username:password pair for mining server
- -u, --user=USERNAME -> username for mining server
- -p, --pass=PASSWORD -> password for mining server
- --cert=FILE -> certificate for mining server using SSL
- -x, --proxy=[PROTOCOL://]HOST[:PORT] -> connect through a proxy
- -t, --threads=N -> number of miner threads (default: number of processors)
- -r, --retries=N -> number of times to retry if a network call fails (default: retry indefinitely)
- -R, --retry-pause=N -> time to pause between retries, in seconds (default: 30)
- --time-limit=N -> maximum time [s] to mine before exiting the program.
- -T, --timeout=N -> timeout for long poll and stratum (default: 300 seconds)
- -s, --scantime=N -> upper bound on time spent scanning current work when long polling is unavailable, in seconds (default: 5)
- --randomize -> Randomize scan range start to reduce duplicates
- -f, --diff-factor -> Divide req. difficulty by this factor (std is 1.0)
- -m, --diff-multiplier -> Multiply difficulty by this factor (std is 1.0)
- -n, --nfactor -> neoscrypt N-Factor
- --coinbase-addr=ADDR -> payout address for solo mining
- --coinbase-sig=TEXT -> data to insert in the coinbase when possible
- --no-longpoll -> disable long polling support
- --no-getwork -> disable getwork support
- --no-gbt -> disable getblocktemplate support
- --no-stratum -> disable X-Stratum support
- --no-extranonce -> disable Stratum extranonce support
- --no-redirect -> ignore requests to change the URL of the mining server
- -q, --quiet -> disable per-thread hashmeter output
- --no-color -> disable colored output
- -D, --debug -> enable debug output
- -P, --protocol-dump -> verbose dump of protocol-level activities
- -B, --background -> run the miner in the background
- --benchmark -> run in offline benchmark mode
- --cputest -> debug hashes from cpu algorithms
- --cpu-affinity -> set process affinity to cpu core(s), mask 0x3 for cores 0 and 1
- --cpu-priority -> set process priority (default: 0 idle, 2 normal to 5 highest)
- -b, --api-bind -> IP/Port for the miner API (default: 127.0.0.1:4048)
- --api-remote -> Allow remote control
- --max-temp=N -> Only mine if cpu temp is less than specified value (linux)
- --max-rate=N[KMG] -> Only mine if net hashrate is less than specified value
- --max-diff=N -> Only mine if net difficulty is less than specified value
- -c, --config=FILE -> load a JSON-format configuration file
- -V, --version -> display version information and exit
- -h, --help -> display this help text and exit
- -a, --algo=ALGO -> specify the algorithm to use, where the user could choose from these algorithms:
NOTES:
This hacking tool is a Bitcoin miner used to generate bitcoins.
It may be bundled with a malware to send to other machines and use the affected machine to mine for Bitcoins.
The affected machine uses high CPU power, which also requires more electricity. This may result in higher electricity bills.
It displays the following when executed in command prompt:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as HKTL_COINMINE.GC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

