BKDR_SHARK.WMP
Symantec_Beta : Backdoor.Trojan
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This backdoor is capable of executing the several commands.
This backdoor may be dropped by other malware.
It connects to a website to send and receive information.
TECHNICAL DETAILS
Arrival Details
This backdoor may be dropped by the following malware:
Installation
This backdoor injects itself into the following processes running in the affected system's memory:
- svchost.exe
Autostart Technique
This backdoor drops the following files:
- %Program Files%\Common Files\bak.dll - copy of original mspmsnsv.dll
- %System%\fi.txt - contains a list of recently used documents
- %System%\msimage.dat - component file also detected as BKDR_SHARK.WMP
- %System%\task.dat - contains list of running processes and their respective process IDs
(Note: %Program Files% is the default Program Files folder, usually C:\Program Files.. %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
Other System Modifications
This backdoor modifies the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\WmdmPmSN
Start = 2
(Note: The default value data of the said registry entry is 3.)
Backdoor Routine
This backdoor opens the following ports:
- port 123
It connects to the following websites to send and receive information:
- {BLOCKED}.{BLOCKED}.123.123
NOTES:
It replaces the following legitimate files with its own AUTORUN component file:
- %System%\mspmsnsv.dll
- %System%\dllcache\mspmsnsv.dll
As a result, the malware is executed whenever the system executes the overwritten DLLs. Trend Micro also detects the autorun component file as BKDR_SHARK.WMP.
It is capable of executing the following commands:
- Retrieves operating system version
- Switches user profiles
- Retrieves process ID of processes/services
- Opens an FTP connection
- Downloads/Uploads files
- Modifies privileges
- Creates processes
- Uninstalls itself
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Restore this modified registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\WmdmPmSN
- From: Start = 2
To: Start = 3
- From: Start = 2
Step 4
Search and delete these files
Step 5
Scan your computer with your Trend Micro product to delete files detected as BKDR_SHARK.WMP. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 6
Restore a file/s that has/have been corrupted/modified by this malware/grayware
To restore system files:
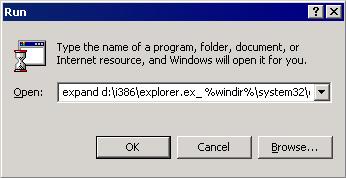
• For Windows 2000:
- Insert your Windows 2000 Installation CD in your CD-ROM drive.
- Click Start>Run.
- In the Open text box, type the following then click OK:
expand D:\i386\{file to restore}.ex_ %windir%\system32\{file to restore}.exe
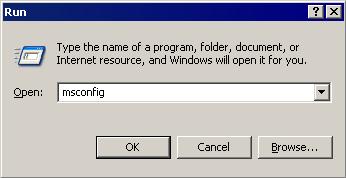
• For Windows XP and Windows Server 2003:
- Click Start>Run.
- In the Open text box, type the following then click OK:
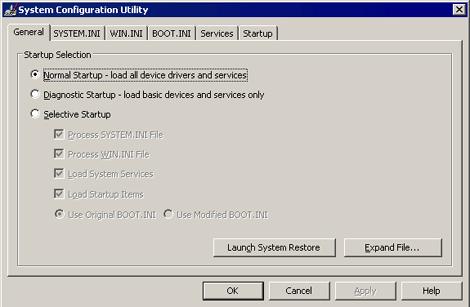
MSCONFIG - Make sure that the option Normal startup - load all device drivers and services option is selected.
- Click the Expand button.
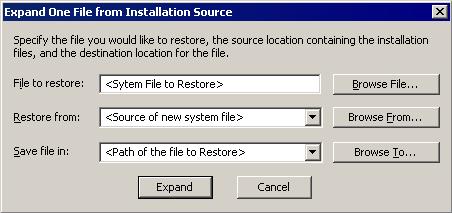
- In the dialog box that appears, type the following:
- File to restore contains the path and file name of the file you wish to restore.
- Restore from contains the path to the Windows CAB files. This path may vary from machine to machine. It may be in a local drive, in a network drive, or in a CD-ROM. In the local drive, it is usually in C:\WINDOWS\OPTIONS\INSTALL.
- Save file in contains the path of the file you wish to restore (Do not include the file name).
- Click the Expand button.
Did this description help? Tell us how we did.


