WORM_SALITY.RL
Windows 98, ME, NT, 2000, XP, Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Trend Micro has flagged this file infector as noteworthy due to the increased potential for damage, propagation, or both, that it possesses.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
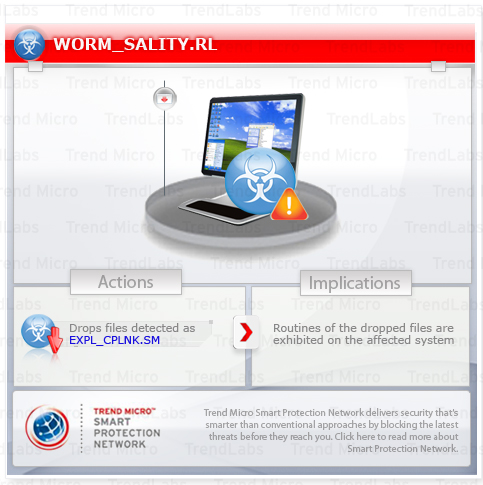
It drops a .LNK file that automatically executes the said file. The dropped .LNK file may use specific filenames. Trend Micro detects this file as EXPL_CPLNK.SM.
This worm may be downloaded by other malware/grayware/spyware from remote sites. It may be dropped by other malware. It may be unknowingly downloaded by a user while visiting malicious websites.
It executes the dropped file(s). As a result, malicious routines of the dropped files are exhibited on the affected system.
TECHNICAL DETAILS
Arrival Details
This worm may be downloaded by other malware/grayware/spyware from remote sites.
It may be dropped by other malware.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This worm adds the following mutexes to ensure that only one of its copies runs at any one time:
- op1mutx9
- woemnm593jfe
Other System Modifications
This worm adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
{malware path and file name} = "{malware path and file name}:*:Enabled:ipsec"
It adds the following registry keys as part of its installation routine:
HKEY_CURRENT_USER\Software\bntrp
(Default) =
HKEY_CURRENT_USER\Software\zrfke
(Default) =
Dropping Routine
This worm drops the following files:
- %User Temp%\{random filename}.exe - detected as PE_SALITY.RL-O
It executes the dropped file(s). As a result, malicious routines of the dropped files are exhibited on the affected system.
Other Details
This worm connects to the following possibly malicious URL:
- http://{BLOCKED}a.com/sm.php
NOTES:
Based on analysis of the codes, it has the following capabilities:
- Enumerates network shares and drops the .DLL file, {random file name}.tmp, which Trend Micro detected as WORM_SALITY.RL
- Drops an .LNK file that automatically executes WORM_SALITY.RL
- Takes advantage of the vulnerability in Windows Shell that could allow arbitrary commands to be executed
It then drops a .LNK file that automatically executes the said file. The .LNK may use any of the following filenames:
- Aline.lnk
- Anna Benson Sex video.lnk
- Anna.lnk
- Audra.lnk
- Bad girl.lnk
- Barbi.lnk
- Barrett Jackson nude photos.lnk
- beautiful.lnk
- Britney Spears XXX.lnk
- Caitie.lnk
- caroline.lnk
- Copy of New File.lnk
- Copy of New Folder.lnk
- Copy of Shortcut.lnk
- Drivers.lnk
- Fotograf.lnk
- Gallery photos.lnk
- groom.lnk
- Jammie.lnk
- Jenna Elfman sex anal deepthroat.lnk
- Juli.lnk
- Julie.lnk
- Kate Beckinsale nude pictures.lnk
- kate.lnk
- Katrina.lnk
- Kelley.lnk
- kleopatra.lnk
- Lisa.lnk
- Mandy.lnk
- Mary-Anne.lnk
- Mary.lnk
- Miss America Porno.lnk
- My beautiful person.lnk
- My photoalbum.lnk
- My Photos.lnk
- Myphotos.lnk
- New Folder.lnk
- New Shortcut.lnk
- Paris Hilton XXX Archive.lnk
- Photoalbum.lnk
- Picture.lnk
- Porno Screensaver.lnk
- rebecca.lnk
- Rena.lnk
- Sara.lnk
- Serials.lnk
- Shortcut.lnk
- stacy.lnk
- Tammy.lnk
- XXX archive.lnk
- XXX hardcore.lnk
- XXX.lnk
The said shortcut file is detected as EXPL_CPLNK.SM.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Restart in Safe Mode
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software
- bntrp
- bntrp
- In HKEY_CURRENT_USER\Software
- zrfke
- zrfke
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- {malware path and file name} = "{malware path and file name}:*:Enabled:ipsec"
- {malware path and file name} = "{malware path and file name}:*:Enabled:ipsec"
Step 6
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_SALITY.RL. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



