WORM_DOWNAD.AD
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm exploits a vulnerability in Server service that, when exploited, allows a remote user to execute arbitrary code on the infected system in order to propagate across networks.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
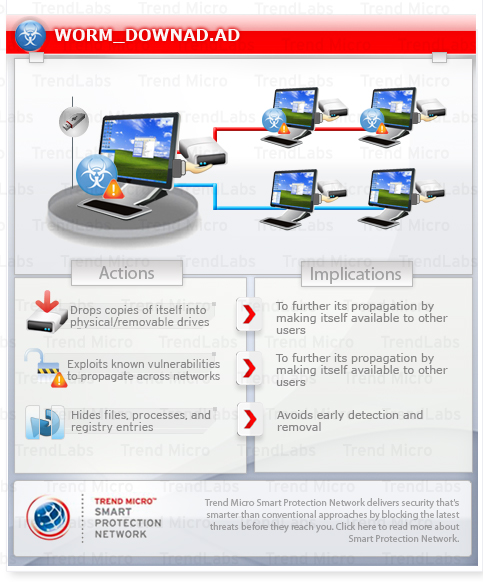
It propagates by dropping copies of itself in physical and removable drives. It also propagates over the Internet by attempting to send the exploit code to random Internet addresses.
It generates a set of URLs containing 250 random sites per day based on the UTC time standard.
It blocks access to websites that contain certain strings, which are mostly related to antivirus programs.
This worm arrives via removable drives. It may be dropped by other malware.
It modifies registry entries to disable various system services. This action prevents most of the system functions to be used.
It drops copies of itself into all the removable drives connected to an affected system. It drops copies of itself into network drives. It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system. It exploits software vulnerabilities to propagate to other computers across a network.
It modifies certain registry entries to hide Hidden files. It prevents users from visiting antivirus-related websites that contain specific strings.
TECHNICAL DETAILS
Arrival Details
This worm arrives via removable drives.
It may arrive via network shares.
It may be dropped by other malware.
Installation
This worm drops the following copies of itself into the affected system:
- %Application Data%\{random file name}.dll
- %System%\{random file name}.dll
- %System%\{random number}.tmp
- %Program Files%\Internet Explorer\{random file name}.dll
- %Program Files%\Movie Maker\{random file name}.dll
- %User Temp%\{random file name}.dll
(Note: %Application Data% is the current user's Application Data folder, which is usually C:\Documents and Settings\{user name}\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Roaming on Windows Vista and 7.. %System% is the Windows system folder, which is usually C:\Windows\System32.. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).. %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- {random characters}
- Global\{random characters based on the computer name}-7
Autostart Technique
This worm registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\SvcHost\
{random characters}
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random characters}
ImagePath = "%System Root%\system32\svchost.exe -k"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{random characters}\Parameters
ServiceDll = "%System%\{malware file name}"
It adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{random characters} = "rundll32.exe {malware path and file name}, Parameter"
Other System Modifications
This worm adds the following registry entries as part of its installation routine:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Applets
dl = "0"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Applets
ds = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Applets
dl = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Applets
ds = "0"
It modifies the following registry key(s)/entry(ies) as part of its installation routine:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\Tcpip\Parameters
TcpNumConnections = "00FFFFFE"
(Note: The default value data of the said registry entry is user-defined.)
It modifies registry entries to disable the following system services:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\BITS
Start = "4"
(Note: The default value data of the said registry entry is 2.)
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\wuauserv
Start = "4"
(Note: The default value data of the said registry entry is 2.)
Propagation
This worm creates the following folders in all removable drives:
- {drive letter}:\Recycler\{SID}
It drops copies of itself into all the removable drives connected to an affected system.
It drops the following copy(ies) of itself in all removable drives:
- {drive letter}:\Recycler\{SID}\{random characters}
It drops copies of itself into network drives.
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
It uses the following user name and password to gain access to password-protected shares:
- 99999999
- 9999999
- 999999
- 99999
- 88888888
- 8888888
- 888888
- 88888
- 77777777
- 7777777
- 777777
- 77777
- 66666666
- 6666666
- 666666
- 66666
- 55555555
- 5555555
- 555555
- 55555
- 44444444
- 4444444
- 444444
- 44444
- 33333333
- 3333333
- 333333
- 33333
- 22222222
- 2222222
- 222222
- 22222
- 11111111
- 1111111
- 111111
- 11111
- 00000000
- 0000000
- 00000
- 0987654321
- 987654321
- 87654321
- 7654321
- 654321
- 54321
- zzzzz
- xxxxx
- qqqqq
- aaaaa
- intranet
- controller
- killer
- games
- private
- market
- coffee
- cookie
- forever
- freedom
- student
- account
- academia
- files
- windows
- monitor
- unknown
- anything
- letitbe
- letmein
- domain
- access
- money
- campus
- explorer
- exchange
- customer
- cluster
- nobody
- codeword
- codename
- changeme
- desktop
- security
- secure
- public
- system
- shadow
- office
- supervisor
- superuser
- share
- super
- secret
- server
- computer
- owner
- backup
- database
- lotus
- oracle
- business
- manager
- temporary
- ihavenopass
- nothing
- nopassword
- nopass
- Internet
- internet
- example
- sample
- love123
- boss123
- work123
- home123
- mypc123
- temp123
- test123
- qwe123
- abc123
- pw123
- root123
- pass123
- pass12
- pass1
- admin123
- admin12
- admin1
- password123
- password12
- password1
- default
- foobar
- foofoo
- temptemp
- testtest
- rootroot
- adminadmin
- mypassword
- mypass
- Login
- login
- Password
- password
- passwd
- zxcvbn
- zxcvb
- zxccxz
- zxcxz
- qazwsxedc
- qazwsx
- q1w2e3
- qweasdzxc
- asdfgh
- asdzxc
- asddsa
- asdsa
- qweasd
- qwerty
- qweewq
- qwewq
- nimda
- administrator
- Admin
- admin
- a1b2c3
- 1q2w3e
- 1234qwer
- 1234abcd
- 123asd
- 123qwe
- 123abc
- 123321
- 12321
- 123123
- 1234567890
- 123456789
- 12345678
- 1234567
- 123456
- 12345
It exploits the following software vulnerabilities to propagate to other computers across a network:
- Vulnerability in Microsoft's Server service
Other Details
This worm connects to the following URL(s) to get the affected system's IP address:
- http://www.getmyip.org
- http://www.whatsmyipaddress.com
- http://www.whatismyip.org
- http://checkip.dyndns.org
It connects to the following time servers to determine the current date:
- myspace.com
- msn.com
- ebay.com
- cnn.com
- aol.com
- w3.org
- ask.com
- yahoo.com
- google.com
- baidu.com
It modifies the following registry entries to hide Hidden files:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced\Folder\Hidden\
SHOWALL
CheckedValue = "0"
(Note: The default value data of the said registry entry is 1.)
It does the following:
- Patches TCPIP.SYS in memory in order to modify the limit of maximum TCP half-connection attempts in systems running Windows XP Service Pack 2. It does this by loading TCPIP.SYS in a certain memory location. It then drops %System%\0{random number}.tmp, which is responsible for creating a device object named TcpIp_Perf and linking it to the loaded TCPIP.SYS in memory. It then sends the control code (patch code) to the linked device object.
- Checks if the command line includes the string RUNDLL32.EXE. If it does, this worm assumes it is running as a scheduled task. It then injects itself to the legitimate processes SVCHOST.EXE and EXPLORER.EXE.
- Exports functions used by other malware. It sets the creation time of the file similar to that of the creation time indicated in the legitimate Windows file KERNEL32.DLL, which is also located in the Windows system folder. It does this to prevent early detection as a newly added file on the affected system.
- Checks the operating system version of the affected system. If the worm is running on a Windows 2000 machine, it injects itself to SERVICES.EXE.
- Injects itself to SVCHOST.EXE if the infected system has any of the following operating systems:
- Windows Server 2003
- Windows Server 2003 R2
- Windows XP
- Executes the following commands to disable auto-tuning if the system is running under Windows Vista:
- netsh interface tcp set global autotuning=disabled
- Injects itself to the process SVCHOST.EXE to hook NetpwPathCanonicalize and avoid reinfection of an affected system.
- Propagates by taking advantage of a vulnerability discovered in certain Microsoft operating systems that could allow remote code execution if an affected system received a specially crafted RPC request, which also contains a shellcode. More information on the said vulnerability can be found in this Microsoft Web page:
- Microsoft Security Bulletin MS08-067
- http://{IP address of the affected machine}:{random port generated by this worm}/{malware file name composed of random characters}
- Propagating over the Internet by attempting to send the exploit code to random Internet addresses. It first broadcasts the opened random port that serves as an HTTP server so that it is accessible over the Internet. Then, it gets the external IP address of the system to check if it has a direct connection to the Internet. Once a direct connection is made, it launches the exploit code over the Internet by checking the external IP address and the configured IP address in the ethernet or modem driver.
- Drops a copy of itself in the Admin$\System32 folder using a randomly named file using the credentials of the compromised user once it gains access. Upon successful network propagation, a scheduled task is created in the %Windows%\Tasks folder using the NetScheduleJobAdd API to be able to execute its dropped copy. The scheduled time of execution on the created job file is retrieved from GetLocalTime API.
- Generates strings and appends the following extensions to create URLs based on the current date:
- .biz
- .info
- .org
- .net
- .com.
- .ws
- .cn
- .cc
- Generates a set of URLs containing 250 random sites per day based on the UTC time standard.
- Checks if any of the generated URLs is active and creates a thread to download and execute files. This routine also converts the host name to an IP address to complete the following URL:
- http://{IP address}/search?q=0
- Creates a named pipe with the following format:
- \.\pipe\System_{random number}
- Hooks the following APIs to filter a list of antivirus-related sites when being accessed on the Internet:
- DnsQuery_A
- DnsQuery_UTF8
- Query_Main
It prevents users from visiting antivirus-related websites that contain the following strings:
- Ccert.
- sans.
- bit9.
- windowsupdate
- wilderssecurity
- threatexpert
- castlecops
- spamhaus
- cpsecure
- arcabit
- emsisoft
- sunbelt
- securecomputing
- rising
- prevx
- pctools
- norman
- k7computing
- ikarus
- hauri
- hacksoft
- gdata
- fortinet
- ewido
- clamav
- comodo
- quickheal
- avira
- avast
- esafe
- ahnlab
- centralcommand
- drweb
- grisoft
- nod32
- f-prot
- jotti
- kaspersky
- f-secure
- computerassociates
- networkassociates
- etrust
- panda
- sophos
- trendmicro
- mcafee
- norton
- symantec
- microsoft
- defender
- rootkit
- malware
- spyware
- virus
- avg
- avp
- eset
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
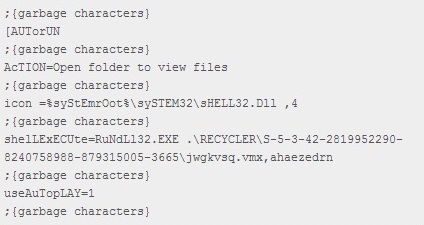
Step 3
Search and delete AUTORUN.INF files created by WORM_DOWNAD.AD that contain these strings
[AUTorUN
;{garbage characters}
AcTION=Open folder to view files
;{garbage characters}
icon =%syStEmrOot%\sySTEM32\sHELL32.Dll ,4
;{garbage characters}
shelLExECUte=RuNdLl32.EXE .\RECYCLER\S-5-3-42-2819952290-8240758988-879315005-3665\jwgkvsq.vmx,ahaezedrn
;{garbage characters}
useAuTopLAY=1
;{garbage characters}
Step 4
Scan your computer with your Trend Micro product to delete files detected as WORM_DOWNAD.AD. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 5
Download and apply this security patch Refrain from using these products until the appropriate patches have been installed. Trend Micro advises users to download critical patches upon release by vendors.
NOTES:
Trend Micro OfficeScan users are also urged to use the following features to protect from WORM_DOWNAD malware:
Enabling Device Access Control
- Open the OfficeScan web console.
- In the left panel, click Networked Computers to expand its list of contents.

- Click Client Management to open the user interface found in the right panel.
- In the right panel, click Setting and choose Device Control Settings from the dropdown list.

- Click Enable Device Control then Block Autorun function on USB devices after setting your desired permissions.
- At the bottom of the window, click Apply to All Clients.
Enabling USB Autoscan
For Trend Micro OfficeScan 10.6 SP1 and later, enable this Trend Micro OfficeScan feature, please refer to the following eSupport page:
Enabling Scan Network Drive
- Still in the OfficeScan web console, in the left panel, click Networked Computers to expand its list of contents.
- Click Client Management to open user interface on the right panel.
- In the right panel, click Settings and select Scan Settings>Real-time Scan Settings.

- In Scan Settings, check Scan network drive.

- At the bottom of the window, click Apply to All Clients.
Enabling Web Reputation Service
- Still in the OfficeScan web console, in the left panel, click Networked Computers.
- Click Client Management to open user interface on the right panel.
- In the right panel, click Settings, then choose Web Reputation Settings from the dropdown list. This opens a new window where you can configure the Web Reputation service settings.
- Check Enable Web reputation policy on the following operation systems.

- At the bottom of the window, click Apply to All.
Enabling Firewall Feature
- Still in the OfficeScan web console, in the left panel, click Networked Computers.
- Click Client Management to open user interface on the right panel.
- In the right panel, click Settings, then choose Additional Service Settings from the dropdown list. This opens a new window where you can enable firewall service.

- Check Enable service ion the following operating systems.

- At the bottom of the window, click Apply to All Clients.
Trend Micro OfficeScan users may also install and configure the Intrusion Defense Firewall (IDF) plugin to further prevent WORM_DOWNAD infections.
Configuring IDF to Protect from DOWNAD infections
- Right-click Selected Computer Group>Actions>Deploy Client Plug-in(s).

- Create a Security Profile. Select Security Profiles in the IDF console. Right-click Windows Workstation Profile then select Duplicate. Then you may rename the Security Profile.
Note: Skip this step if there is an existing IDF profile.

- Disable the IDF firewall to preserve the Officescan Firewall. In the Security Profile Window, select Firewall and uncheck Inherit. Then select Off.

- Enable corresponding IDF rules by doing the following:
• Select Deep Packet Inspection and uncheck Inherit, then Select On and Prevent.

• Under DPI rules, select IDS/IPS. In the upper right corner, type in CVE-2008-4250 and press Enter.

• Wait for the relevant IDF rules to be found and check all IDF rules, then click Save. - Assign the security profile to the select computer group by doing the following:
• Right-click on Computer Group>Actions>Assign Security Profile.

• Select the newly created Security Profile, then click OK. - To check if the IDF plugin was properly configured, Select a machine inside the selected Computer Group. The expected status are the following: Managed (Online), Firewall: Off, DPI: Prevent, 4 rules.

Did this description help? Tell us how we did.