BKDR_PLUGX.NSC
Backdoor:Win32/Plugx.H (Microsoft), Win32/Korplug.BX trojan (NOD32)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Backdoor
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware is related to the zero-day exploit on Adobe Flash Player (CVE-2014-0502) detected as SWF_EXPLOYT.LPE.
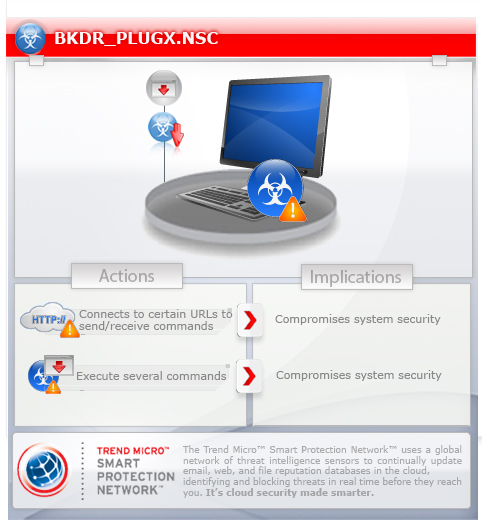
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes commands from a remote malicious user, effectively compromising the affected system.
It deletes itself after execution.
TECHNICAL DETAILS
Arrival Details
This backdoor arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This backdoor drops the following copies of itself into the affected system:
- %All Users Profile%\DRM\RasTls.exe
(Note: %All Users Profile% is the All Users or Common profile folder, which is C:\Documents and Settings\All Users in Windows 2000, XP, and Server 2003, and C:\ProgramData in Windows Vista and 7.)
It drops the following file(s)/component(s):
- %All Users Profile%\DRM\RasTls\{random file name} - Non-malicious
(Note: %All Users Profile% is the All Users or Common profile folder, which is C:\Documents and Settings\All Users in Windows 2000, XP, and Server 2003, and C:\ProgramData in Windows Vista and 7.)
It creates the following folders:
- %All Users Profile%\DRM
- %All Users Profile%\DRM\RasTls
(Note: %All Users Profile% is the All Users or Common profile folder, which is C:\Documents and Settings\All Users in Windows 2000, XP, and Server 2003, and C:\ProgramData in Windows Vista and 7.)
It injects threads into the following normal process(es):
- svchost.exe
Other System Modifications
This backdoor adds the following registry keys as part of its installation routine:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\
Windows\CurrentVersion\Internet Settings\
5.0\User Agent\Post Platform
HKEY_CURRENT_USER\SOFTWARE\Microsoft\
Windows\CurrentVersion\Internet Settings\
User Agent\Post Platform
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Internet Setttings\
5.0\User Agent
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Internet Setttings\
User Agent
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Copy, move, rename, delete files
- Create directories
- Create files
- Enumerate files
- Execute files
- Get drive information
- Get file information
- Open and modify files
- Log keystrokes and active window
- Enumerate TCP and UDP connections
- Enumerate network resources
- Set TCP connection state
- Lock workstation
- Log off user
- Restart/Reboot/Shutdown system
- Display a message box
- Perfrom port mapping
- Enumerate processes
- Get process information
- Terminate processes
- Enumerate registry keys
- Create registry keys
- Delete registry keys
- Copy registry keys
- Enumerate registry entries
- Modify registry entries
- Delete registry values
- Screen capture
- Delete services
- Enumerate services
- Get service information
- Modify services
- Start services
- Perform remote shell
- Connect to a database server and execute SQL statement
- Host Telnet server
It connects to the following URL(s) to send and receive commands from a remote malicious user:
- http://{BLOCKED}ice.no-ip.org/{generated value}
- http://{BLOCKED}a.ns1.name/{generated value}
- http://{BLOCKED}a.ns1.name:443/{generated value}
- http://{BLOCKED}i.ns01.us/{generated value}
Other Details
This backdoor deletes itself after execution.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Restart in Safe Mode
Step 3
Search and delete these folders
- %All Users Profile%\DRM
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry. Before you could do this, you must restart in Safe Mode. For instructions on how to do this, you may refer to this page If the preceding step requires you to restart in safe mode, you may proceed to edit the system registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Setttings\5.0
- User Agent
- User Agent
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Setttings
- User Agent
- User Agent
Step 5
Restart in normal mode and scan your computer with your Trend Micro product for files detected as BKDR_PLUGX.NSC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


