JAVA_DLOAD.ZZC
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
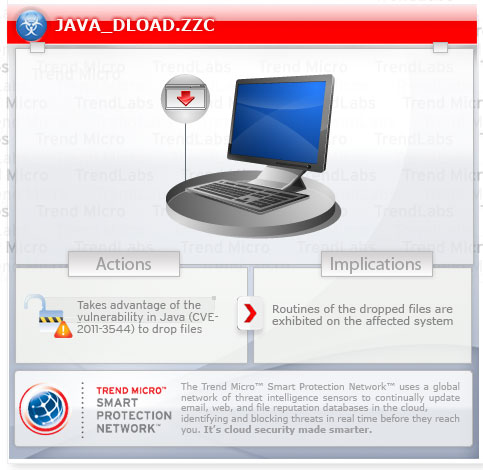
This malware exploits a known vulnerability in Java to drop malicious files. Routine of the dropped files are then exhibited on the affected system.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan may be hosted on a website and run when a user accesses the said website.
It executes the files it drops, prompting the affected system to exhibit the malicious routines they contain.
TECHNICAL DETAILS
Arrival Details
This Trojan may be hosted on a website and run when a user accesses the said website.
Installation
This Trojan drops the following files:
- %User Temp%\~spawn{random numbers}.tmp.dir\ATxBtCuy.exe - detected by Trend Micro as TROJ_PPOINTER.SM
- %User Temp%\~spawn{random numbers2}.tmp.dir\ATxBtCuy.exe - detected by Trend Micro as TROJ_PPOINTER.SM
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
It creates the following folders:
- %User Temp%\~spawn{random numbers}.tmp.dir
- %User Temp%\~spawn{random numbers2}.tmp.dir
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003.)
Dropping Routine
This Trojan executes the files it drops, prompting the affected system to exhibit the malicious routines they contain.
Other Details
More information on this vulnerability can be found below:
NOTES:
It exploits the following vulnerability in Java:
- Unspecified Vulnerability in the Java Runtime Environment
This Java applet contains metasploit.DAT, which identifies the name of the file and the number of times that it is dropped into the system.
Sample content of metasploit.DAT is as follows:
Spawn=2 Executable=ATxBtCuy.exe
The executable file ATxBtCuy.EXE is included in the .JAR file.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 3
Close all opened browser windows
Step 4
Search and delete these folders
- %User Temp%\~spawn{random numbers}.tmp.dir
- %User Temp%\~spawn{random numbers2}.tmp.dir
Step 5
Scan your computer with your Trend Micro product to delete files detected as JAVA_DLOAD.ZZC. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
For updates on available workarounds and patches for this vulnerability, please refer to the following page:
- http://www.oracle.com/technetwork/topics/security/javacpuoct2011-443431.html
Did this description help? Tell us how we did.


