TROJ_REGIN.SM
Windows, Windows 64bit


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This is the Trend Micro detection for malicious files that belong to the malware family known as REGIN. REGIN is a multi-component malware that uses different files for its malicious functionalities and payload. It also sports multiple advanced techniques to avoid user and security vendor detection. This detection addresses the initial driver/loader file responsible for initializing the malware's malicious routines.
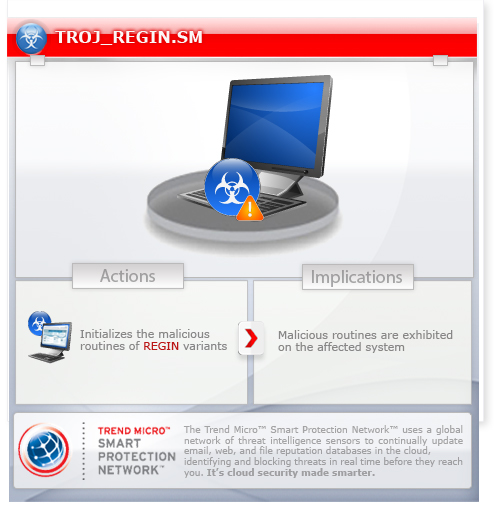
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
TECHNICAL DETAILS
NOTES:
This file is usually found in the System32 folder and may use any of the following filenames:
- abiosdsk.sys
- adpu160.sys
- atdisk.sys
- cdaudio.sys
- floppy.sys
- ndisips.sys
- parclass.sys
- pciclass.sys
- pcidump.sys
- pciport.sys
- rasprt.sys
- rdpmdd.sys
- Ser8UART.sys
- serial.sys
- usbclass.sys
Some of the driver files may contain Microsoft properties in order to disguise themselves and avoid detection by the user.
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as TROJ_REGIN.SM. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


