OSX_FAVDONW.A
Trojan-Downloader.OSX.FavDonw.c (Kaspersky); OSX/FakeAV-DWN (Sophos); Trojan-Downloader.OSX.Fav.A (Clamav); Trojan-Downloader.OSX.FavDonw (Ikarus)
Mac OS


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
Upon execution, this malware prompts the installation of fake antivirus application.
Once installed, it may download and install the fake antivirus/antispyware software, MacShield from a certain URL.
The said malware is already detected as OSX_FAKEAV.HXZ.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following files:
- //Application/dShield.app/
- //Application/dShield.app/Contents
- //Application/dShield.app/Contents/Info.plist
- //Application/dShield.app/Contents/MacOS/
- //Application/dShield.app/Contents/MacOS/dShield
- //Application/dShield.app/Contents/PkgInfo
- //Application/dShield.app/Contents/Resources/{resource files}
NOTES:
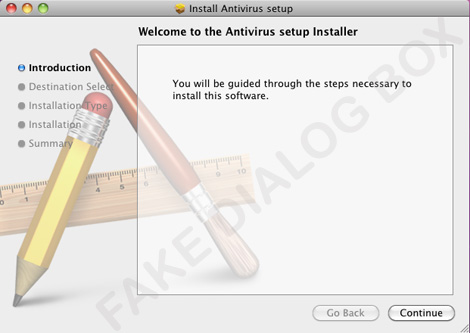
Upon execution, it prompts the installation of fake antivirus application:
Once installed, it may download and install the fake antivirus/antispyware software, MacShield from the following URL:
- http://{BLOCKED}.{BLOCKED}.162.117/mac/soft.php?affid={number}
The said malware is already detected as OSX_FAKEAV.HXZ.
SOLUTION
NOTES:
- Terminating Malware Process
Go to Applications>Utilities>Activity Monitor and terminate the process related to dShield using the "Quit Process" button. - Deleting Malware File
Go to your Applications folder and drag dShield to the Trash. You may also right-click on the application then select Move to Trash. - Restart your machine
- Scan your computer with your Trend Micro product to delete files detected as OSX_FAVDONW.A and OSX_FAKEAV.HXZ. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

