RANSOM_ELFREXDDOS.A
HEUR:Trojan.Linux.Rex.a (Kaspersky), Gen:Variant.Trojan.Linux.DDos.1 (F-Secure)
Linux


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Trojan arrives by accessing affected shared networks.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives by accessing affected shared networks.
Other Details
This Trojan connects to the following URL(s) to get the affected system's IP address:
- http://www.trackip.net/ip?json
- https://ipinfo.io/ip
- https://ipv4.icanhazip.com
It does the following:
- It is capable of distributed denial of service (DDoS) attacks.
- It monitors port 5099 to receive information from other nodes.
- It launches RPC plug-ins to scan network resources. These plug-ins are used to scan for vulnerabilities on the affected site and networks. Some identified scanner names are the following:
- AirOS Scanner
- Contact Scanner
- Drupal Scanner
- Jetspeed
- Ransom Scanner
- Wordpress
- exagrid
- kerner
- It request bitcoins as payment (amount may change depending on attacker). If ransom is not paid, the server is threatened with DDoS attacks and the payment price is increased.
NOTES:
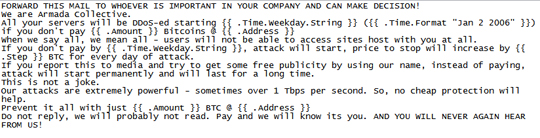
This malware is capable of sending ransom notes via email. The email contains the following message:
SOLUTION
Scan your computer with your Trend Micro product to delete files detected as RANSOM_ELFREXDDOS.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


