RANSOM_LEBANA.THBBBAH
Troj/Lebana-A (SOPHOS_LITE); Trojan.Deshacop (QUICKHEAL); TR/AD.RansomHeur.qhuas (ANTIVIR)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
It encrypts files found in specific folders.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Autostart Technique
This Ransomware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Run
UpdateBackUp = {Malware Path}
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
UpdateBackUp = {Malware Path}
Other System Modifications
This Ransomware modifies the following registry entries:
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows Defender
DisableAntiSpyware = 1
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows Defender
DisableRoutinelyTakingAction = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
WindowsDefenderMAJ = 1
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows NT\SystemRestore
DisableSR = 1
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows NT\SystemRestore
DisableConfig = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 1
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows
DisableCMD = 2
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\Windows\System
DisableCMD = 2
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\
DisableCMD = 2
HKEY_LOCAL_MACHINE\Software\Policies\
Microsoft\MMC\{GUID}
Restrict_Run = 1
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection\
DisableRealtimeMonitoring = 1
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services
SecurityHealthService = 4
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services
WdNisSvc = 3
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services
WinDefend = 3
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoControlPanel = 1
HKEY_LOCAL_MACHINE\System\CurrentControlSet\
Control\SafeBoot\Minimal
MinimalX = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoRun = 1
HKEY_LOCAL_MACHINE\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableRegistryTools = 1
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoRun = 1
HKEY_CURRENT_USER\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
WindowsDefenderMAJ = 1
HKEY_CURRENT_USER\Software\Microsoft\
Windows Script Host\Settings
Enabled = 0
HKEY_CURRENT_USER\Software\Policies\
Microsoft\Windows NT\SystemRestore
DisableConfig = 1
HKEY_CURRENT_USER\SYSTEM\CurrentControlSet\
Services
USBSTOR = 4
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
System
DisableTaskMgr = 1
HKEY_CURRENT_USER\Software\Policies\
Microsoft\Windows\System
DisableCMD=2 = 2
HKEY_CURRENT_USER\Software\Policies\
Microsoft
DisableCMD = 2
HKEY_CURRENT_USER\Software\Policies\
Microsoft\MMC\{GUID}
Restrict_Run = 1
HKEY_CURRENT_USER\SOFTWARE\Policies\
Microsoft\Windows Defender\Real-Time Protection
DisableRealtimeMonitoring = 1
HKEY_CURRENT_USER\SYSTEM\CurrentControlSet\
Services
SecurityHealthService = 4
HKEY_CURRENT_USER\SYSTEM\CurrentControlSet\
Services
WdNisSvc = 3
HKEY_CURRENT_USER\SYSTEM\CurrentControlSet\
Services
WinDefend = 3
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Policies\
Explorer
NoRun = 1
Propagation
This Ransomware drops the following copy(ies) of itself in all removable drives:
- {removable drive letter}:\Copter.flv.exe
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
[autorun]
open=Copter.flv.exe
shellexecute=Copter.flv.exe
Process Termination
This Ransomware terminates the following processes if found running in the affected system's memory:
- ProcessHacker
- procexp64
- msconfig
- taskmgr
- chrome
- firefox
- regedit
- opera
- UserAccountControlSettings
- yandex
- microsoftedge
- microsoftedgecp
- iexplore
Other Details
This Ransomware does the following:
- It disables executing the following applications by adding the following registry entries:
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\{application}
- Debugger = RIP
- Debugger = RIP
where {application} are as follows:- msconfig.exe
- taskmgr.exe
- cmd.exe
- chrome.exe
- firefox.exe
- opera.exe
- microsoftedge.exe
- microsoftedgecp.exe
- notepad++.exe
- notepad.exe
- iexplore.exe
- MSASCuiL.exe
- mmc.exe
- gpedit.msc
- UserAccountControlSettings.exe
- Autoruns64.exe
- Autoruns.exe
- systemexplorer.exe
- taskkill.exe
- powershell.exe
- yandex.exe
- attrib.exe
- bcdedit.exe
- sethc.exe
- mspaint.exe
- dllhost.exe
- rundll.exe
- rundll32.exe
- cabinet.dll
- chkdsk.exe
- DBGHELP.exe
- DCIMAN32.exe
- wmplayer.exe
- ksuser.dll
- mpg4dmod.dll
- mydocs.dll
- rasman.dll
- shellstyle.dll
- secpol.msc
- url.dll
- usbui.dll
- webcheck.dll
- recoverydrive.exe
- logoff.exe
- control.exe
- explorer.exe
- regedit.exe
- csrss.exe
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\{application}
- It disables the following:
- Windows Defender
- System Restore
- Task Manager
- CMD
- Run Command
- Control Panel
- Safe Boot
- Registry Tools
- Windows Script Host
- USB driver
Ransomware Routine
This Ransomware encrypts files found in the following folders:
- %User Profile%\Documents
- %User Profile%\Pictures
- %User Profile%\Downloads
- %User Profile%\Desktop
- %User Profile%\Videos
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It appends the following extension to the file name of the encrypted files:
- .ANNABELLE
NOTES:
This ransomware displays the following message box: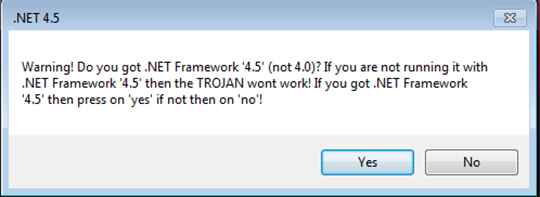
It then reboots the system and displays this lock screen: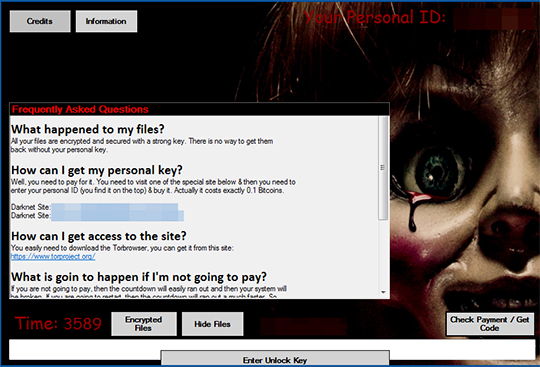
The unlock key is wHYecVx64uX2zjVedeTeyRLN.
It also displays the following window that shows the decryption process of the malware: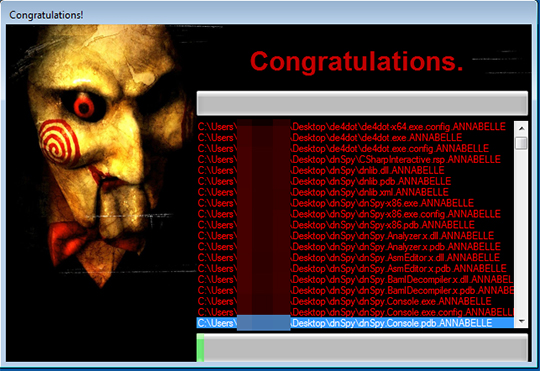
It reboots the system and displays the malware's MBR, making the system unbootable: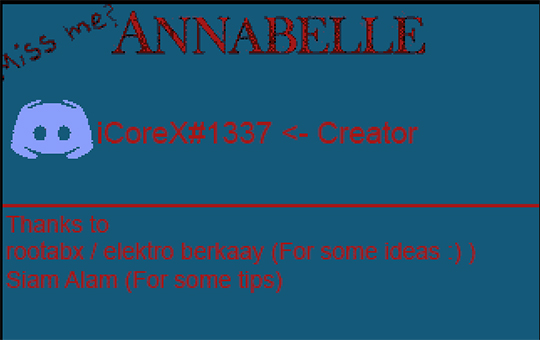
SOLUTION
NOTES:
Restore the system from backup or reinstall the operating system (OS). The system may be made bootable by doing a system repair using a Windows installer disk.
Did this description help? Tell us how we did.


