The Security of Mobile Payment Options
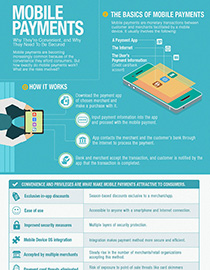 view infographic: The Security of Mobile Payments
view infographic: The Security of Mobile Payments
Even before the Christmas city lights go up, everybody is rushing to tick their shopping lists and hit the shops to score early bird discounts and other great bargains. With the convenience mobile devices offer, people increasingly prefer to pay using their devices as it simulates an all-in-one experience for busy people on the go. While you’re using your handheld device, you can instantly make a transaction with it as well, without having to fish for your wallet and risk misplacing other belongings especially in crowded places.
Essentially, mobile payments are faster and more secure than conventional payments. All you need is a payment app to launch a transaction, and because you don’t need to use your card, the risk of point-of-sale (PoS) attacks such as card skimmers are eliminated. Mobile payments are also protected by security measures. However, since it has become a popular payment alternative, attackers could use Man-in-the-Middle (MitM) attacks via fake or malicious apps and data breaches to take advantage of the new payment methods. The app itself could also have coding or process flaws, which can lead to leaked banking information. Additionally, if the device is lost or stolen, the stored financial data could be whisked for malicious purposes. If you’re not careful, your data and credentials could end up in the wrong hands.
While mobile payments do come with such threats, this payment method is still favorable to many users, especially for the coming shopping season where people will be more inclined to pay using their devices to save on time and effort. However, it still pays to be smart. Equip your mobile device with proper security software to block malicious apps. Make sure that you only connect to a secure network and avoid public or open Wi-Fi. Before making a transaction, always double-check if you’re using the right payment app. Finally, update your passwords and use unique, hard-to-guess passwords for both emails and apps.
Learn more about mobile payments and how you can stay secure by clicking on the embedded infographic.

Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Artículos Recientes
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation