By Ashish Verma, Deep Patel, Simon Dulude (Senior Threat Researchers, TrendAI™ Research)
Key takeaways
- TrendAI™ analysis of botnet activity from the RondoDox, RedTail, and Mozi-AndroxGh0st groups shows how modern botnets have evolved into industrialized operational infrastructure, enabling attacks to scale far beyond traditional campaigns.
- Botnets now exploit vulnerabilities within hours of disclosure, with operators actively monitoring public vulnerability sources while continuing to exploit old but unpatched vulnerabilities.
- Internet-exposed devices — including routers (deployed in homes, offices, and industrial or critical infrastructure environments), DVR systems, enterprise gateways, and cloud-hosted workloads — might serve either as direct targets or as unintended enablers of botnet operations.
- Defense platforms that combine machine-speed automation with human expertise can help organizations prioritize and remediate the most exploitable vulnerabilities before botnets can weaponize them.
Overview
The botnet landscape has undergone a significant transformation. It has moved well beyond the era of uncoordinated, opportunistic strikes led by entry-level actors to a marked professionalization that closely mirrors the structured development cycles found in legitimate corporate software houses.
Threat groups are increasingly demonstrating agility and organizational structure that enable them to approach exploit development as a rapid production process. By closely monitoring resources, such as the National Vulnerability Database (NVD), and events like Pwn2Own, these groups have minimized the interval between public vulnerability disclosures and the deployment of weaponized attacks.
| Metric | Value | Trend |
|---|---|---|
| Total CVEs in the dataset | 97 unique vulnerabilities | RondoDox: 90 exploits |
| Average time to weaponization | 72 hours from NVD disclosure | 80% faster |
| Primary targets | IoT (80%), enterprise (15%), cloud (5%) | Shifting to enterprise |
Table 1. An overview of findings illustrating shifts in the scale, speed, and target focus of industrialized botnet exploitation
This report, which draws on our findings from 2025, shows how established threat actors have industrialized their workflows into automated engines for disruption. While these botnets are familiar names, their modern capabilities represent a dangerous departure from their past designs. Our core finding shows that the window between vulnerability disclosure and botnet weaponization has narrowed to just hours.
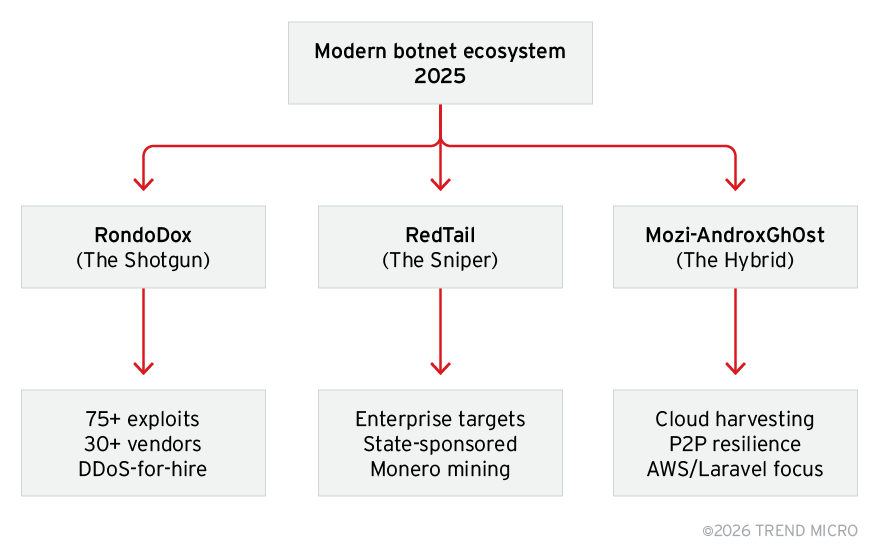
We characterize the botnet landscape as comprising three primary archetypes: RondoDox, RedTail, and the Mozi-AndroxGh0st hybrid.
Figure 1. Botnet operational archetypes showing the divergence between mass-scale exploitation (RondoDox), enterprise targeting (RedTail), and hybrid cloud–focused campaigns (Mozi-AndroxGh0st)
RondoDox (The Shotgun)
RondoDox operates as a high-volume delivery system. By integrating more than 80 exploits into its codebase, it targets a broad array of hardware from over 30 vendors. Its primary objective is to overwhelm networks with exploits to identify a single unpatched entry point. This approach accounts for the statistical likelihood that vulnerabilities will exist within sufficiently large networks.
RedTail (The Sniper)
RedTail exemplifies a contrasting approach. Attributed to the Lazarus Group, this botnet avoids consumer internet-of-things (IoT) devices and instead targets high-value enterprise infrastructure. It employs custom implants and precise targeting logic to infiltrate the networks of financial institutions and technology firms. RedTail also functions as a specialized tool for state-sponsored espionage and significant financial gain.
Mozi-AndroxGh0st (The Hybrid)
Mozi-AndroxGh0st demonstrates the trend of code reuse in 2025. It combines the peer-to-peer (P2P) architecture of the Mozi botnet with the AndroxGh0st framework. This integration provides the botnet with stealth, via a decentralized network, and credential theft capabilities characteristic of cloud-focused exploit kits.
From Shotguns to Snipers: Defining the current threat
The modern botnet ecosystem has evolved beyond indiscriminate mass infection into a stratified threat landscape defined by specialization. Today’s operators are no longer uniformly “spray-and-pray” actors. Instead, they range from bandwidth aggregators monetizing disruption, to precision infrastructure breachers seeking strategic footholds, to hybrid operators targeting cloud credentials through multilayered attack chains. The following archetypes illustrate how contemporary botnets differ not only in technical execution, but in economic model, targeting philosophy, and long-term intent.
RondoDox (The Edge Aggressor)
RondoDox represents the industrialization of high-volume exploitation. It is not subtle, surgical, or intelligence-driven. Instead, it is optimized for scale, designed to rapidly compromise vast numbers of internet-facing devices and convert them into monetizable bandwidth. This archetype reflects the continued profitability of disruption-as-a-service within the underground economy.
- The goal: Powering the DDoS economy
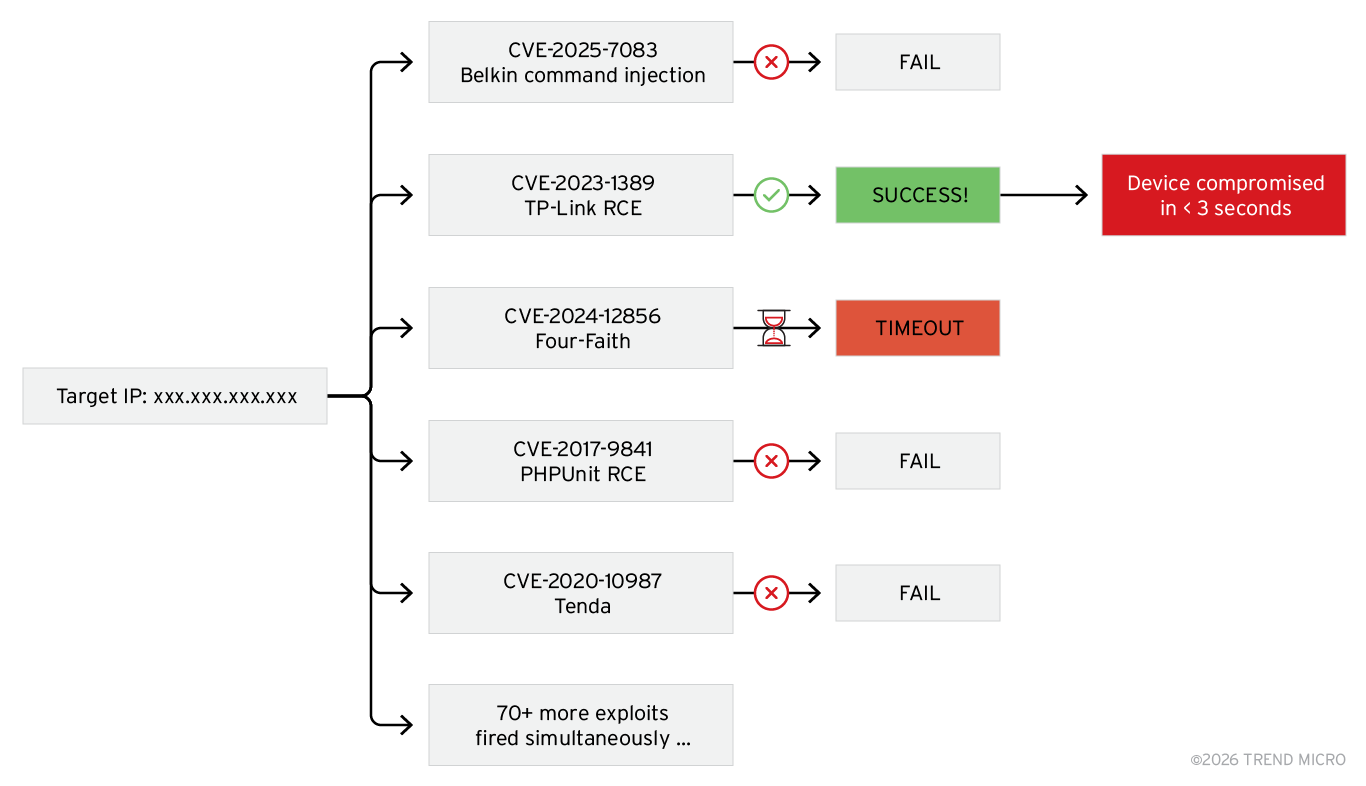
RondoDox is designed to support the global DDoS-for-hire market. Its operators do not seek sensitive data or corporate secrets, but focus on acquiring bandwidth. By infecting hundreds of thousands of devices, they create a large, rentable platform capable of taking websites offline for paying clients. - The tactic: The exploit shotgun
Stealth is not a priority for this group. Its operators use a method known as the “exploit shotgun,” which involves launching multiple exploits at a single IP address at once. Rather than identifying the target hardware, they attempt various attacks to identify any vulnerabilities. If a device has an unpatched vulnerability from the past five years, RondoDox is likely to exploit it through brute force. - The targets: Small office and home office (SOHO) networks and the industrial edge
The botnet thrives in the neglected corners of the internet. Its primary targets are SOHO routers, which are often installed and forgotten by users, rarely receiving the firmware updates needed to stay secure. - Evolution: Targeting industrial routers and DVR systems
Beyond consumer gear, we have seen a sharp increase in RondoDox targeting multiple industrial routers and generic DVR systems. These are high-value targets for a DDoS botnet because they sit directly on the network edge and often have high-speed connections. Once RondoDox takes over, it clears out any competing malware and locks the door behind it, turning a simple industrial tool into a permanent “zombie” in its botnet.
Figure 2. A visualization of RondoDox’s shotgun approach
RedTail (The Perimeter Breacher)
If RondoDox is a sledgehammer, RedTail is a high-velocity drill. This botnet does not focus on consumer routers, but targets the very walls built to keep hackers out — specifically, enterprise-grade security appliances.
- The goal: Monero and long-term access
RedTail is a dual threat. Its primary financial engine is Monero mining using a heavily modified version of the XMRig miner. However, it is not just a hit-and-run operation. The malware frequently implants SSH backdoors to ensure that the operators can return at any time. This suggests that the initial mining activity might just be a way to monetize a target while they wait for more lucrative espionage opportunities. - The tactic: Attacking high-end infrastructure
While others fire broad scans, RedTail operators hunt for critical vulnerabilities in high-end infrastructure. We have seen them aggressively exploit n-day vulnerabilities and critical flaws in Palo Alto Networks (PAN-OS) and Ivanti Connect Secure VPNs. By compromising these devices, they gain root access to the most sensitive part of a corporate network. This allows them to bypass traditional internal security because they are essentially operating from the trusted gateway. - Attribution: The Lazarus connection
The level of investment behind RedTail points toward a state-sponsored origin. Research from Akamai has highlighted significant tactical overlaps with the Lazarus Group, including the use of private mining pools, a resource-intensive approach that suggests nation-state backing. However, Akamai has not formally attributed RedTail to any specific group, and attribution remains speculative. Specifically, RedTail does not use public mining pools or visible wallet addresses. Instead, its operators run their own private mining infrastructure and pool proxies. This is an expensive and complex logistical hurdle that most cybercriminals cannot afford.
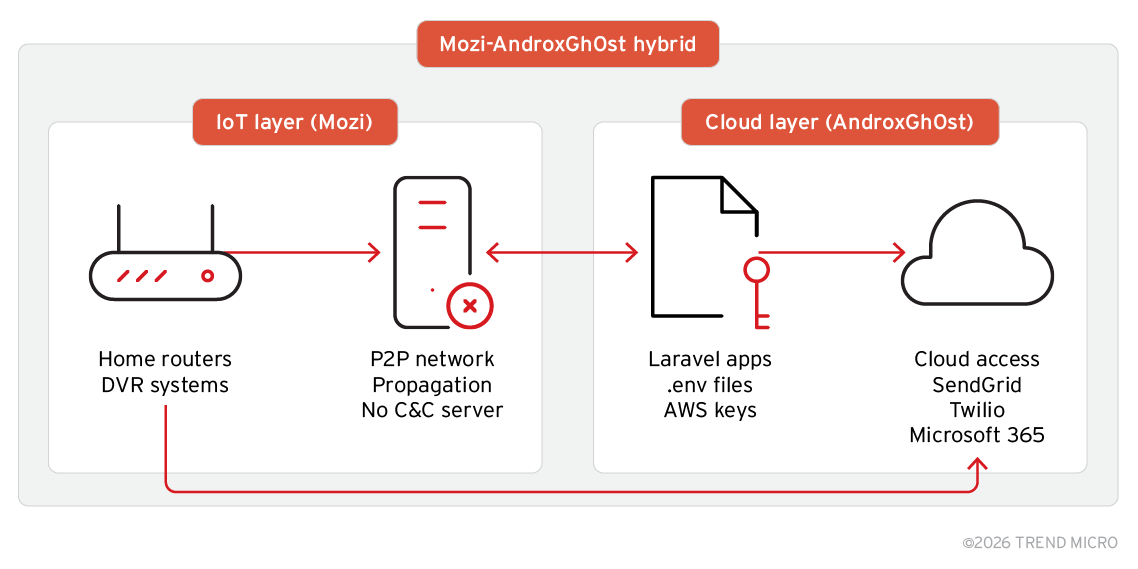
Mozi-AndroxGh0st (The Credential Harvester)
This pairing reflects a notable development in 2025 where previously discontinued botnet code, including Mozi, has been reused and incorporated into modern cloud-targeting botnets such as AndroxGh0st.
- The goal: Steal data from the cloud
The primary goal is not simple disruption, but credential harvesting. The botnet targets sensitive environment files (.env) that developers often leave exposed. By cracking these files, it gains direct access to AWS, SendGrid, and Twilio accounts. This allows its operators to hijack massive cloud computing power or launch large-scale spam and phishing campaigns using a victim company’s own legitimate infrastructure. - The tactic: Bridging IoT and web frameworks
What makes this threat notable is its dual-threat architecture. It uses Mozi’s old tricks to infect IoT devices like home routers and DVRs, and then uses that massive proxy network to hide its real objective of attacking web frameworks. It specifically targets exposed and unpatched Laravel- and PHPUnit-based vulnerabilities to gain a foothold on web servers. By using a compromised household router to attack a corporate server, the botnet makes its activity look like standard, harmless internet noise. - The persistence: Why Mozi remains active despite shutdown
Mozi was thought to have been neutralized after a global kill switch was activated in late 2023. However, the AndroxGh0st operators containerized Mozi’s P2P engine. This gives the hybrid a decentralized backbone that has no central server to shut down. Every infected device talks to its neighbors, sharing commands and update files in a way that is resilient against traditional law enforcement takedowns. - The tactic: Exploiting the development pipeline
The botnet targets a very specific set of flaws, most notably CVE-2017-9841 in PHPUnit. It scans for exposed vendor folders on web servers and uses them to execute remote code. Once it’s in, it doesn’t just steal data, but often drops web shells to ensure that it has a permanent backdoor. We have observed that this hybrid has become the go-to tool for threat actors looking to pivot from simple IoT infection to a full-scale cloud breach.
Figure 3. The hybrid botnet model integrating Mozi’s P2P IoT propagation with AndroxGh0st’s cloud-focused exploitation targeting Laravel applications and exposed credentials
The vulnerability intersection
The technical overlaps among these three botnets highlight significant concerns regarding current internet security. These are not isolated incidents; they reflect a coordinated exploitation ecosystem where a single hardware vulnerability becomes a persistent tool for major threat actors.
Vulnerability longevity: One of our key findings is that patches are not reaching the network edge. Vulnerabilities from 2016 continue to be actively exploited. In SOHO and IoT environments, devices that were unsecure eight years ago remain persistent assets for botnet operators. These long-standing vulnerabilities offer a reliable, low-cost resource for groups like RondoDox and Mozi, enabling them to maintain large botnets without seeking new zero-day exploits.
Exploit democratization: There is a significant overlap in the CVEs used by RondoDox, RedTail, and the Mozi-AndroxGh0st hybrid, specifically from 2018 to 2021. This suggests that high-quality exploit kits are being traded, leaked, or sold as commodities on the dark web. When a developer for a group like Lazarus (RedTail) perfects an exploit for an enterprise gateway, it eventually trickles down to a broader range of cybercriminals. The competitive advantage is no longer about who finds the flaw, but who automates its delivery the fastest.
Active development and near-real-time weaponization: Attackers no longer wait months to integrate new CVEs. RondoDox, for example, integrated CVE-2025-7083 and CVE-2025-9528 within days of their release in the NVD. These vulnerabilities, which enable command injection in multiple router devices, were weaponized so rapidly that many security teams had not completed their initial risk assessments before attacks began. Botnet authors now monitor the NVD closely, seeking immediate opportunities.
The following are two of the “battleground” vulnerabilities that the botnets continue to exploit as n-days:
- CVE-2023-1389 (TP-Link Archer AX21): A primary target, acts as a central resource in ongoing attacks
- CVE-2017-9841 (PHPUnit): Remains actively exploited by RondoDox and AndroxGh0st to compromise web servers despite its age
A botnet exploit matrix — which maps specific CVEs to the botnets that exploit them, showing which high-velocity exploits are used by multiple cybercriminal organizations — and the indicators of compromise (IoCs) for this report can be found here and here, respectively.
Weaponization velocity
The primary threat from attackers is not technical skill, but their speed, with defenders having a shorter window to respond. Previously, organizations had weeks to test and deploy patches, but now, botnet-related attacks often occur within hours of a vulnerability being disclosed.
Modern botnet operators, for example, now use the NVD as a real-time source. Automated systems monitor new entries, focusing on critical scores that signal remote code execution (RCE) or authentication bypass.
RondoDox: The operators behind this botnet use the Pwn2Own hacking contest as a source. Instead of waiting for official CVE assignments or vendor advisories, they analyze live demonstrations and contest notes to develop exploits. Their early use of vulnerabilities first disclosed during the Pwn2Own event illustrates this approach. By the time patches are released, RondoDox has already targeted thousands of systems.
RedTail: Its operators has established a new standard for the speed of weaponizing vulnerabilities. When CVE-2024-3400 was first disclosed, the group integrated it into their scanner within hours of the first proof of concept (PoC) appearing on GitHub. They target high-value perimeter devices while administrative teams are still assessing the initial alert. This immediate exploitation enables them to gain access before patches can be deployed.
The grace period for patching no longer exists, as vulnerabilities are increasingly exploited by botnets within hours of disclosure. By the time most security teams receive an official advisory, groups such as RedTail and RondoDox have already weaponized the flaw and initiated global scanning.
This accelerated threat environment is fueled by the immediate availability of PoC code. In several critical cases, exploit attempts occurred within three to six hours of a PoC being published on GitHub. This pace leaves little margin for delayed patching.
In some cases, real-world exploitation outpaces official vulnerability catalogs, such as the CISA Known Exploited Vulnerabilities (KEV) Catalog. In late 2025, for instance, RondoDox exploited CVE-2025-7083 and CVE-2025-9528 well before these vulnerabilities were included in federal tracking and remediation frameworks.
| CVE ID | Target software | Botnet | Weaponization speed | Source |
|---|---|---|---|---|
| CVE-2024-3400 | Palo Alto PAN-OS | RedTail | Zero-day/Day one | Volexity |
| CVE-2025-55182 (React2Shell) | React/Next.js | RondoDox | Under 12 Hours | TrendAI™ Research |
| CVE-2025-7083 | Belkin edge routers | RondoDox | Instant (pre-NVD) | TrendAI™ Research |
| CVE-2017-9841 | PHPUnit framework | Mozi Hybrid | Persistent reuse | CISA KEV Catalog |
Table 2. The observed time to weaponization for several vulnerabilities, illustrating the rapid transition from disclosure to active exploitation across multiple botnets
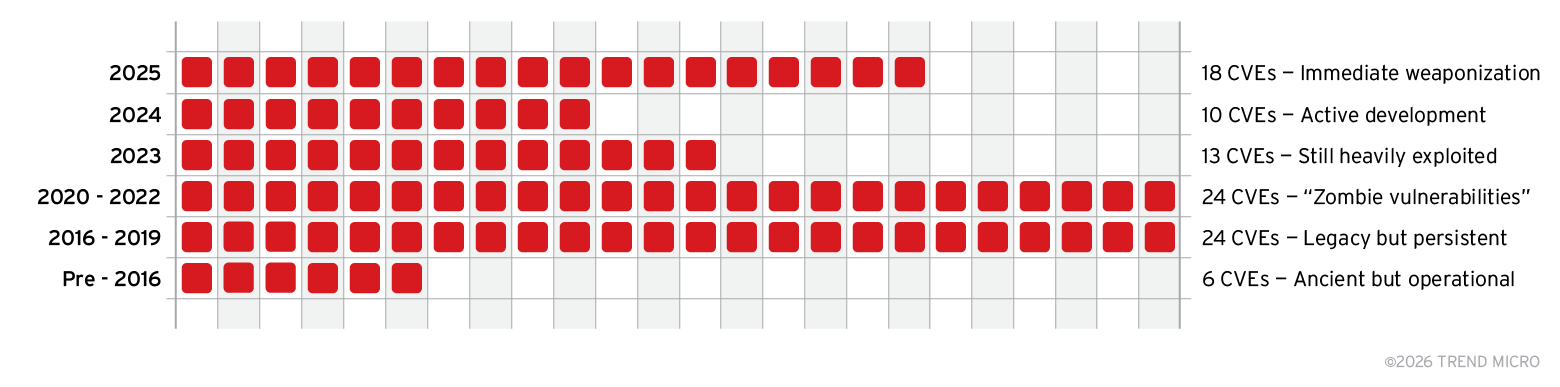
Exploiting vulnerabilities old and new
The distribution of actively exploited CVEs shows that botnet operators draw from vulnerabilities across multiple generations, rather than focusing solely on newly disclosed flaws. While 2024 and 2025 vulnerabilities are rapidly weaponized, a substantial portion of exploitation activity remains concentrated in CVEs disclosed between 2016 and 2022, as well as even earlier weaknesses that persist in long-lived and poorly maintained devices. These so-called “zombie” and legacy vulnerabilities continue to provide reliable access due to patching gaps, embedded system life cycles, and operational inertia. The pattern highlights a dual reality of the current threat landscape: Attackers aggressively adopt new exploits while simultaneously relying on older, proven vulnerabilities that remain widely exposed.
Figure 4. The distribution of actively exploited CVEs by disclosure period, highlighting the continued weaponization of both recent and legacy vulnerabilities
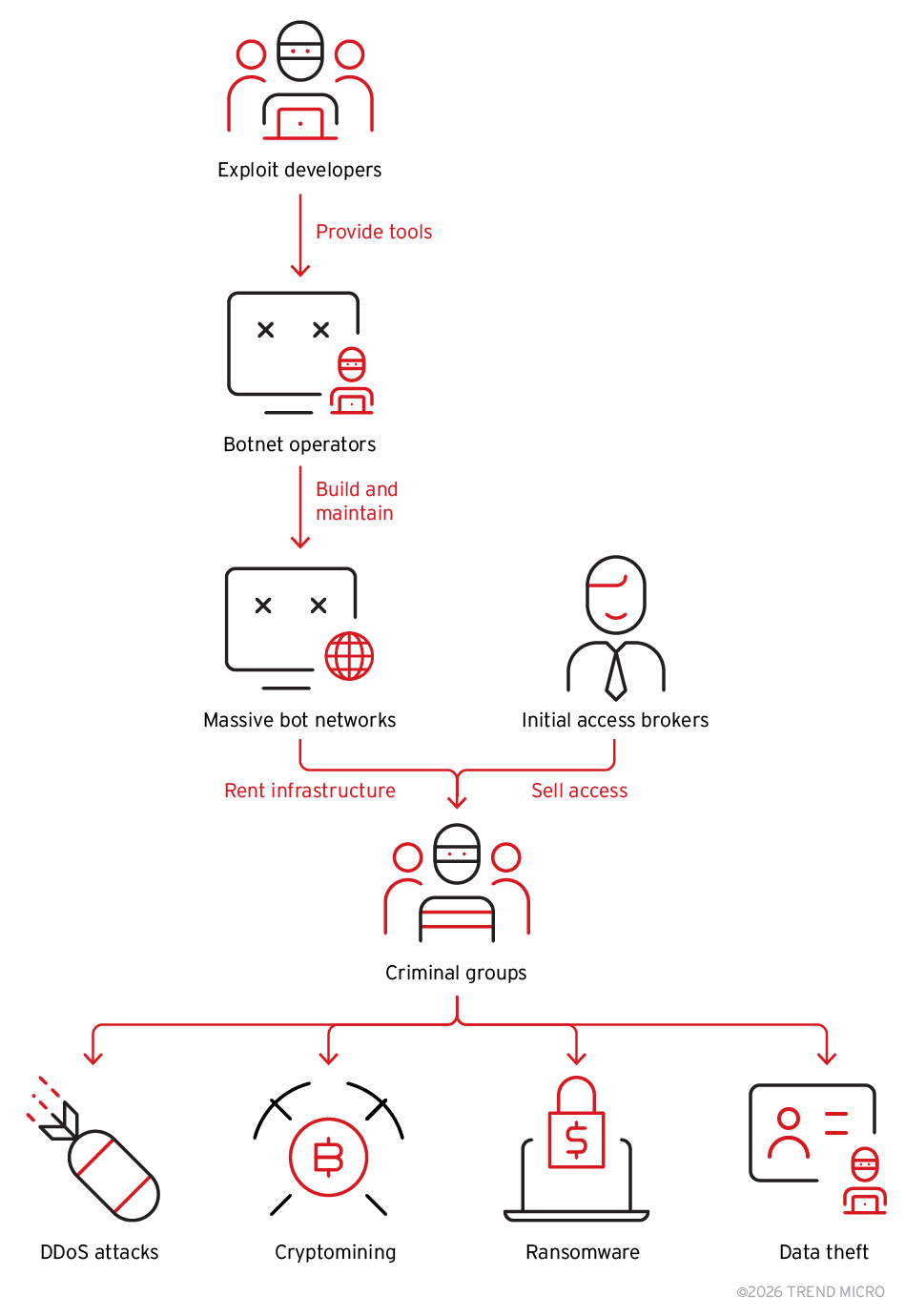
The perks of shared infrastructure
A significant development is the shift toward an infrastructure-as-a-service (IaaS) model. Leading botnet operators now construct and maintain extensive digital botnets that they lease to other criminal organizations, rather than using them solely for their own operations. This division of labor means the group gaining initial access is often different from the one carrying out ransomware attacks or data theft. Botnets are now acting as the underlying infrastructure enabling multiple forms of cybercriminal activity.
Figure 5. An IaaS model showing how a shared botnet infrastructure underpins a broad range of cybercriminal activities, including distributed denial-of-service (DDoS) attacks, cryptocurrency mining, ransomware, and data theft
Shared infrastructure has become a defining feature of modern botnet operations, enabling both attribution obfuscation and sustained activity:
- Attribution obfuscation: By funneling traffic through the same pool of command-and-control (C&C) nodes, rival botnets successfully scramble the breadcrumbs that researchers use for attribution.
- Sustained activity: The resilience afforded by this shared backbone ensures that even if one malware strain is successfully neutralized, the underlying C&C servers remain active to support other campaigns.
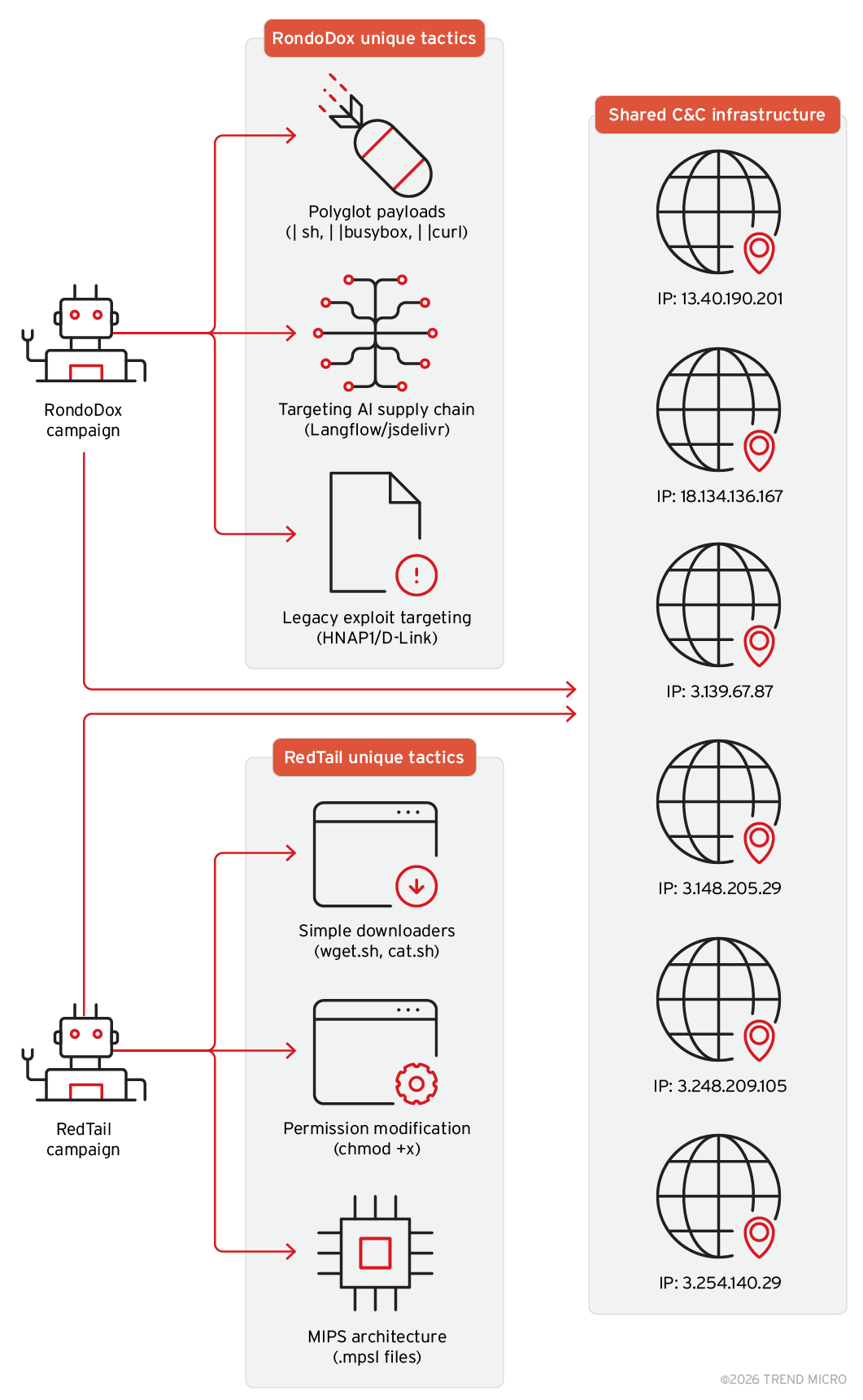
Figure 6. The unique tactics and the shared C&C infrastructure employed by RondoDox and RedTail
The killer mechanism
Even as botnets operate on shared infrastructure, the main conflict now is not between hackers and defenders, but among rival botnets competing for control of the same compromised hardware. This competition determines which botnet secures all available processing power.
Rivalry among cybercriminals: Botnet operators view compromised servers as limited resources. Since activities such as cryptocurrency mining or DDoS attacks require substantial CPU power, they do not share devices with competitors. When a botnet detects another on the same system, it immediately attempts to remove the rival and gain exclusive control.
The adversarial logic of clean.sh: RedTail exemplifies this approach. It deploys a payload, often called clean.sh, designed to remove competing malware. After establishing access, the script scans for rival threats such as Kinsing or Mirai, terminates their processes, deletes their files, and blocks their communication ports.
Monopolizing the machines: The objective is complete control. By eliminating competitors, RedTail ensures that all the victims’ CPU resources are used for its Monero-mining operations. This aggressive removal process is now standard practice among botnets.
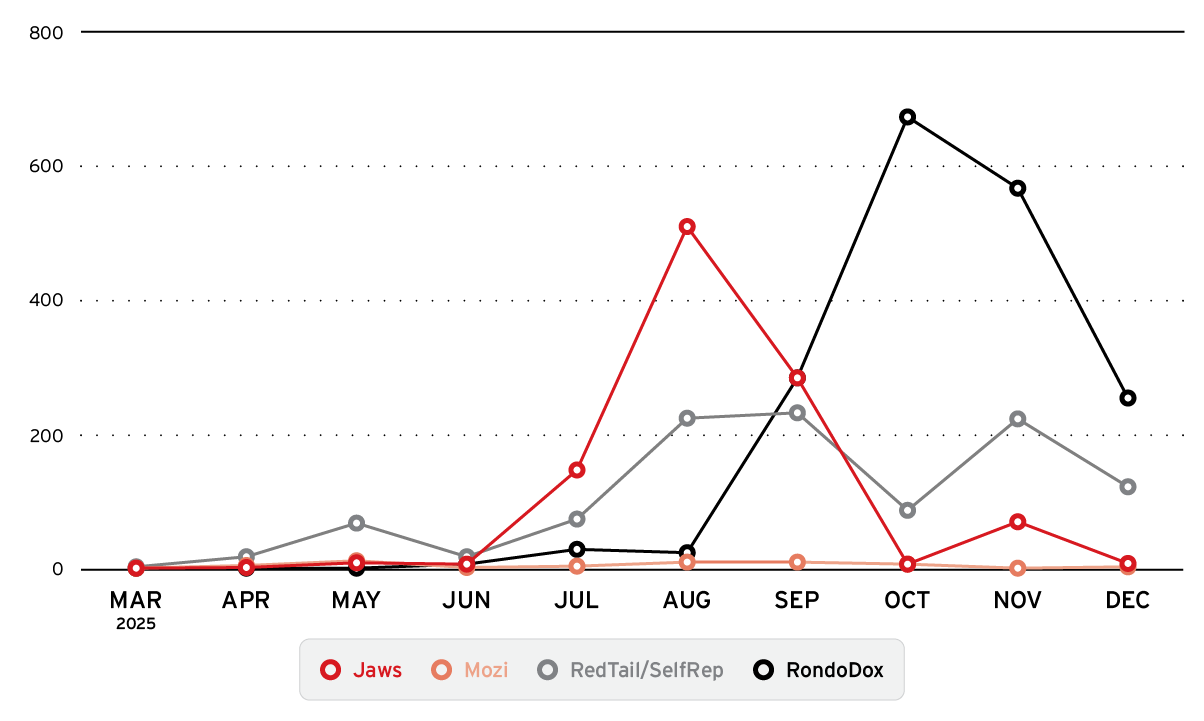
The summer surge
Our telemetry from 2025 shows that the volume of attacks was low in the first and second quarter, but escalated significantly in the third quarter, which we refer to as the “summer surge.”
Figure 7. Attack volume over time, showing activity across major botnets and highlighting changes in campaign intensity throughout 2025
Our analysis of the data further reveals the following trends:
- Jaws, which is linked to legacy IoT attacks, and RedTail both reached their highest activity in August, with 508 and 223 recorded events, respectively.
- While RedTail’s activity remained steady, RondoDox’s surged in the fourth quarter, increasing from near zero in the first half of the year to 671 events in October. It became the leading volume aggressor by the end of the year.
Impact and mitigation
As botnet operations become increasingly automated, exploitation now occurs at a speed that often exceeds the timelines of human response. This acceleration expands the impact of attacks beyond digital systems, introducing potential consequences for connected physical environments.
Operational technology (OT): When a botnet such as RondoDox compromises industrial routers, the impact extends beyond network disruptions. These devices manage factory floors, logistics hubs, and assembly lines, so an infection can halt operations. By targeting the industrial edge, botnet operators can cause physical shutdowns, escalating a software flaw into a production crisis.
Operational challenges in high-volume vulnerability management: Over 40,000 vulnerabilities were disclosed in 2024 alone, with an even higher total in 2025. The traditional approach of patching every vulnerability is no longer viable. This scale enables attackers to succeed with broad, automated attacks. While defenders review advisories, automated botnets are already scanning millions of targets. Automation consistently outpaces manual response. AI-driven security research platforms like TrendAI ÆSIR can address this challenge by combining machine-speed automation with human expertise, to identify zero-day vulnerabilities before botnet operators do.
The botnet activity we observed in 2025 reflects a structural shift toward automation-driven operations. Specialized roles and industrialized workflows have compressed the timeline from vulnerability disclosure to active exploitation, leaving little room for traditional response models. Moving into 2026 and beyond, organizations must treat botnets not as isolated malware campaigns, but as integrated elements of a shared automated infrastructure that enables large-scale cybercriminal activity. Defending against this model requires security capabilities that operate at comparable speed and scale.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Artículos Recientes
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation