TROJ_SIREFEF.BZA
TrojanDropper:Win32/Sirefef (Microsoft), Trojan.Zeroaccess.C (Symantec), Troj/ZAccess-RQ (Sophos), W32/ZAccess.BQAC!tr.bdr (Fortinet), Win32/Sirefef.FY trojan (ESET)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It deletes itself after execution.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following copies of itself into the affected system and executes them:
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\GoogleUpdate.exe
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\GoogleUpdate.exe
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local on Windows Vista and 7.. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).)
It drops the following component file(s):
- %Windows%\assembly\GAC\Desktop.ini
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\@ - config file
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\@ - config file
(Note: %Windows% is the Windows folder, which is usually C:\Windows.. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local on Windows Vista and 7.. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).)
It creates the following folders:
- %AppDataLocal%\Google\Desktop\Install\{GUID}
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\U
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\L
- %Program Files%\Google\Desktop\Install\{GUID}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\U
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\L
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local on Windows Vista and 7.. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).)
It injects itself into the following processes as part of its memory residency routine:
- explorer.exe
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Google Update = ""%AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\GoogleUpdate.exe" >"
It registers its dropped component as a system service to ensure its automatic execution at every system startup. It does this by creating the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{RLO character}etadpug
Parameters = "136"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{RLO character}etadpug
Start = "2"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{RLO character}etadpug
Type = "16"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{RLO character}etadpug
ErrorControl = "0"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\{RLO character}etadpug
ImagePath = "%Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\GoogleUpdate.exe"
It registers its dropped component as a system service to ensure its automatic execution at every system startup. It does this by creating the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
Services\{RLO character}etadpug
Other System Modifications
This Trojan deletes the following registry keys:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Enum\Root\LEGACY_BITS
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Enum\Root\LEGACY_SHAREDACCESS
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Enum\Root\LEGACY_WSCSVC
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Enum\Root\LEGACY_WUAUSERV
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\wscsvc
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\wuauserv
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\BITS
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\wuauserv
Other Details
This Trojan deletes itself after execution.
NOTES:
For this Trojan to have a successful installation, it first attempts to elevate its privilege level by calling certain APIs. If the attempt fails, it drops the following files:
- %User Temp%\InstallFlashPlayer.exe - normal application
- %User Temp%\msimg32.dll - .DLL copy of the malware also detected as TROJ_SIREFEF.BZA
This Trojan disguises itself as msimg32.dll, since this is loaded by the legitimate InstallFlashPlayer.exe. It executes the legitimate Adobe Application %User Temp%\InstallFlashPlayer.exe to load the malicious file %User Temp%\msimg32.dll. This routine is intended to trigger the UAC prompt and trick the user in granting privilege to the Flash Player setup and consequently to load malicious file msimg32.dll.
This Trojan inserts the RLO Unicode character together with unprintable unicode characters on file names of the following folders to prevent user access in some operating systems:
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}
Accessing the folders in Windows Vista results to the following error message:
This RLO character trick is also used in the following added registry entry to disguise itself as a legitimate service entry:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\{RLO character}etadpug
ImagePath = "%Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\GoogleUpdate.exe"
Below is a comparison of the registry of two machines - one with RLO Unicode support, and the other without RLO Unicode support:


Same trick is used on the following added autorun entry:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Google Update = "%AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters}\{GUID}\GoogleUpdate.exe"
When a user tries to access this entry, this error message will be displayed:
Furthermore, this Trojan also modifies the permissions (ACL) of the following created folders to prevent user access in some operating systems:
- %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}
- %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}
Accessing the folder in Windows XP may result to the following error message:
To further lessen the infected host's security, this Trojan also terminates the following Microsoft security-related processes:
- wscntfy.exe
- MSASCui.exe
- MpCmdRun.exe
- MsMpEng.exe
- NisSrv.exe
- msseces.exe
It uses a configuration file @. The said file contains a list of 256 IP addresses in hex and the time since 1980. It uses this list of IP addresses to communicate with other infected hosts in a peer-to-peer (P2P) network. Information shared in the network includes updated list of files and infected hosts. It connects to the following URL to obtain information about the origin of the infected machine:
- http://j.maxmind.com/app/geoip.js
Sample reply from the mentioned site:
SOLUTION
NOTES:
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Restart in Safe Mode.
To restart in Safe Mode:
For Windows 2000 users
Restart your computer.
Press F8 when you see the Starting Windows bar at the bottom of the screen.
Choose the Safe Mode option from the Windows Advanced
Options menu then press Enter.
For Windows XP users
1. Restart your computer.
2. Press F8 after the Power-On Self Test (POST) routine
is done. If the Windows Advanced Options menu does not appear, try restarting then pressing F8 several times when the POST screen appears.
3. Choose the Safe Mode option from the Windows Advanced Options menu then press Enter.
For Windows Server 2003 users
1. Restart your computer.
2. Press F8 after Windows starts up. If the Windows Advanced Options menu does not appear, try restarting again and pressing F8 several times afterward.
3. On the Windows Advanced Option menu, use the arrow keys to select Safe Mode then press Enter.
For Windows Vista and Windows 7 users
1. Restart your computer.
2. Press F8 after the Power-On Self Test (POST) routine is done. If the Advanced Boot Options menu does not appear, try restarting and then pressing F8 several times after the POST screen is displayed.
3. On the Advanced Boot Options menu, use the arrow keys to select the Safe Mode option, and then press Enter.
Step 3
Disable Service Registry
- Open the Registry Editor by pressing Windows Key + R , type regedit into the Run input box, and then pressing ENTER.
- In the left panel, double-click the following:
HKEY_LOCAL_MACHINE>SYSTEM>CurrentControlSet>services>gupdate - In the right panel, locate the registry value:
ImagePath = "%Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}\{GUID}\GoogleUpdate.exe" - Right-click on the value name and choose Modify. Change the value data of this entry to:
ImagePath = "@" - In the right panel, locate the registry value:
Start = "2" - Right-click on the value name and choose Modify. Change the value data of this entry to:
Start = "4"
Step 4
For Windows Vista and later versions, you may skip 1 and 2 and just add permission by pressing 'yes' button on permission pop-up, For other Windows operating system versions, you need to assign an owner for the malware folder in order to access/delete it. To do this you need the following steps:
- Open the folder %AppDataLocal%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}
(Note: %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local on Windows Vista and 7. %Program Files% is the default Program Files folder, usually C:\Program Files in Windows 2000, Server 2003, and XP (32-bit), Vista (32-bit), and 7 (32-bit), or C:\Program Files (x86) in Windows XP (64-bit), Vista (64-bit), and 7 (64-bit).) - In the menu bar above, click Tools>Folder Options>View Tab. Uncheck use simple file sharing (Recommended) then press apply.

- Right Click the {GUID} folder and click Properties. Click Security Tab>Advanced button>Owner.
- Choose any owner then press 'Apply' button.
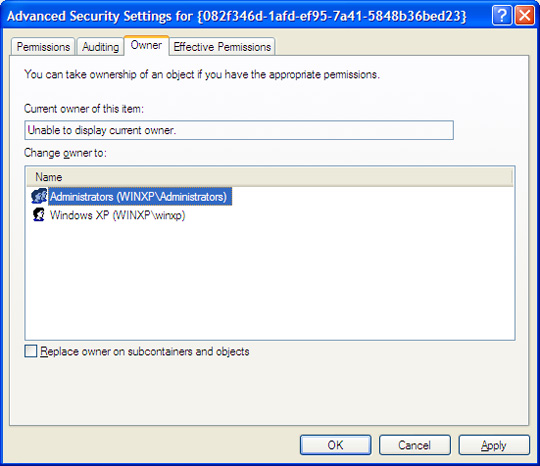
- Re-open folder Properties then on Security Tab. Checked the Full Control Box (Allow) then click 'Apply' button.
- Delete the folder to remove the malware.
- Open the folder %Program Files%\Google\Desktop\Install\{GUID}\{unprintable characters1}\{unprintable characters2}\{RLO + unprintable characters3}.
- In the menu bar above click Tools>Folder Options>View Tab. Uncheck 'use simple file sharing (Recommended)' then press apply.
- Right Click the {GUID} folder and click Properties. Click Security Tab>Advanced button>Owner.
- Choose any owner then press 'Apply' button.
- Re-open folder Properties then on Security Tab. Checked the Full Control Box (Allow) then click 'Apply' button.
- Delete the contents of the folder excluding '@' file. (This is non-malicious but can be deleted upon restart).
- Restore the registry entries backup in Step 2 by executing the .reg file in saved folder and file name you specified.
Step 5
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_SIREFEF.BZA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files.
Did this description help? Tell us how we did.


