COOKIE_ASK
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Others
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
What is a cookie?
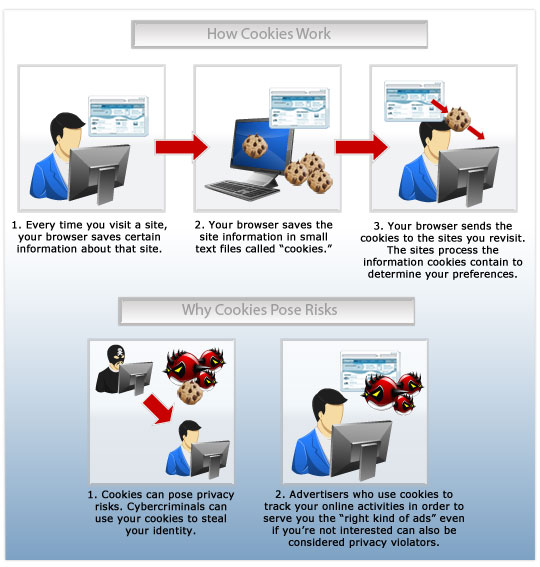
Cookies are small text files that are created on a user’s system whenever they visit a web site. It’s a way for that website to remember its visitors and all that they do on it, so the next time they visit, the website automatically recognizes them and lets them see and continue where they left off. It’s such a subtle process that, by default, users don’t even notice it.
Cookies are also used to track users’ browsing activity through multiple sites for marketing purposes. This lets internet advertisers figure out what sort of ads that the user would be more interested in, and display them accordingly.
Do cookies pose as threats?
By themselves, cookies are harmless, and are there simply for the ease and convenience of the user’s browsing experience. However, they can be considered as a threat to your privacy, as the cookies from certain ad networks can keep track of your online activities. This in itself can be considered a violation of a user’s privacy.
Cybercriminals can also utilize malware and browser attacks in the past to steal cookies. They do this to impersonate users on the websites they frequent, ‘fooling’ the website into automatically providing the compromised user’s personal information. WORM_KOOBFACE, for example, did exactly this to hijack users’ Facebook accounts and post on people’s walls without their authorization.
TECHNICAL DETAILS
NOTES:
This tracking cookie is installed on a system when an affected user visits the following website:
- http://www.ask.com
Tracking cookies (data miners) are cookies that are used by two or more Web sites to track an affected user's Web browsing habits and display advertisement or other material the users might be interested in.
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Scan your computer with your Trend Micro product to delete files detected as COOKIE_ASK. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
What should we do with cookies?
- Delete cookies regularly. The browser you use should have this feature. Consult your browser’s product manual or help guide to see how to do this.
- Consider private browsing. Browsers have modes where they disable cookies automatically. Once again, consult your browser’s product manual or help guide to see how to do this.
For more information about cookies and your privacy online, you can check out our e-book on the subject here.
Did this description help? Tell us how we did.

