TROJ_UPATRE in Spammed Messages Using Various Subjects
On October 31, 2014 we observed spam mail that posed as an invoice notification and urge users to download a file from the link provided in the email. The downloaded file purported to be a .pdf file but it's true format is an executable file. The file that is downloaded from is detected as TROJ_UPATRE.GMRM.
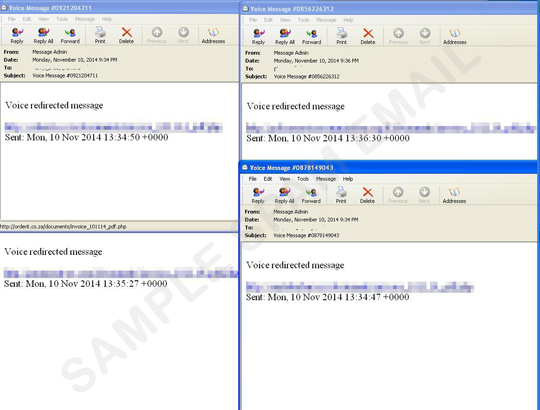
Just a few days after, we encountered a surge of spam mails from our sources and found almost 80 thousand samples that were related from the October 31 spam surge, but this time the URL format was changed. The new attack used subject lines such as fake employee document, outdated invoice, fax and voice message that you needed to download. In the message itself, the URL it has the /dropbox/invoice.php folder. The downloaded file is detected as TROJ_UPATRE.YYQM.
Users are advised to be cautious when opening emails from supposedly known sources as they may not actually be what they appear, such as in this case. It's highly advisable to immediately delete emails from unknown sources. Users are also advised to use a security solution that protects from spam and its components.
- ENGINE:7.5
- PATTERN:1066
