OSX_DOK.C
HEUR:Trojan-Spy.OSX.Aptordoc.b (Kaspersky) MacOS:Dok-D [Trj] (Avast)
Mac OS X


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware abuses certificates and has security software evasion that affects machines using Apple's OS X operating system. The fake certificates installed by the malware allows for man in the middle attacks. The malware is also known to target financial institutions.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It modifies the affected system's HOSTS files. This prevents users from accessing certain websites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following copies of itself into the affected system and executes them:
- /Users/Shared/AppStore.app
HOSTS File Modification
This Trojan modifies the affected system's HOSTS files to prevent a user from accessing the following websites:
- 127.0.0.1 localhost
- 255.255.255.255 broadcasthost
- ::1 localhost
- 127.0.0.1 metrics.apple.com
- 127.0.0.1 ocsp.apple.com
- 127.0.0.1 su.itunes.apple.com
- 127.0.0.1 ax.su.itunes.apple.com
- 127.0.0.1 swscan.apple.com
- 127.0.0.1 swcdn.apple.com
- 127.0.0.1 swdist.apple.com
- 127.0.0.1 a1.phobos.apple.com
- 127.0.0.1 a101.phobos.apple.com
- 127.0.0.1 a102.phobos.apple.com
- 127.0.0.1 a103.phobos.apple.com
- 127.0.0.1 a104.phobos.apple.com
- 127.0.0.1 a105.phobos.apple.com
- 127.0.0.1 a11.phobos.apple.com
- 127.0.0.1 a12.phobos.apple.com
- 127.0.0.1 a13.phobos.apple.com
- 127.0.0.1 a14.phobos.apple.com
- 127.0.0.1 a15.phobos.apple.com
- 127.0.0.1 access.apple.com
- 127.0.0.1 advertising.apple.com
- 127.0.0.1 albert.apple.com
- 127.0.0.1 ali.apple.com
- 127.0.0.1 ams.apple.com
- 127.0.0.1 apple.apple.com
- 127.0.0.1 apple.com
- 127.0.0.1 appleconnect.apple.com
- 127.0.0.1 appleid-it.apple.com
- 127.0.0.1 appleid.apple.com
- 127.0.0.1 appleseed.apple.com
- 127.0.0.1 appleseed3.apple.com
- 127.0.0.1 appleseedtest.apple.com
- 127.0.0.1 aps.info.apple.com
- 127.0.0.1 ara.apple.com
- 127.0.0.1 arait.apple.com
- 127.0.0.1 asia.apple.com
- 127.0.0.1 asw.apple.com
- 127.0.0.1 atlaslms.apple.com
- 127.0.0.1 av.apple.com
- 127.0.0.1 benefits.apple.com
- 127.0.0.1 beta.apple.com
- 127.0.0.1 bugreport.apple.com
- 127.0.0.1 bugreporter.apple.com
- 127.0.0.1 c.apple.com
- 127.0.0.1 calendar.apple.com
- 127.0.0.1 certifications-test.apple.com
- 127.0.0.1 certifications.apple.com
- 127.0.0.1 certifications2.apple.com
- 127.0.0.1 checkcoverage.apple.com
- 127.0.0.1 checkrepair.apple.com
- 127.0.0.1 concierge-mobile.apple.com
- 127.0.0.1 concierge.apple.com
- 127.0.0.1 consultants.apple.com
- 127.0.0.1 cooljobs.apple.com
- 127.0.0.1 deimos.apple.com
- 127.0.0.1 deimos2.apple.com
- 127.0.0.1 deimos3.apple.com
- 127.0.0.1 deploy.apple.com
- 127.0.0.1 developer.apple.com
- 127.0.0.1 developer2.apple.com
- 127.0.0.1 developertest.apple.com
- 127.0.0.1 devforums.apple.com
- 127.0.0.1 devimages.apple.com
- 127.0.0.1 diagnostics.apple.com
- 127.0.0.1 discussions.apple.com
- 127.0.0.1 documentation.apple.com
- 127.0.0.1 downloads.apple.com
- 127.0.0.1 ecommerce.apple.com
- 127.0.0.1 employment.apple.com
- 127.0.0.1 enterprise.apple.com
- 127.0.0.1 ep.sap.apple.com
- 127.0.0.1 erp.apple.com
- 127.0.0.1 esp-test.apple.com
- 127.0.0.1 esp.apple.com
- 127.0.0.1 euro.apple.com
- 127.0.0.1 events.apple.com
- 127.0.0.1 ext.apple.com
- 127.0.0.1 ext1.apple.com
- 127.0.0.1 extensions.apple.com
- 127.0.0.1 files.apple.com
- 127.0.0.1 gspa21.ls.apple.com
- 127.0.0.1 gsx-it.apple.com
- 127.0.0.1 gsx.apple.com
- 127.0.0.1 gsxit.apple.com
- 127.0.0.1 guide.apple.com
- 127.0.0.1 help.apple.com
- 127.0.0.1 hrweb.apple.com
- 127.0.0.1 iad.apple.com
- 127.0.0.1 iadworkbench.apple.com
- 127.0.0.1 id.apple.com
- 127.0.0.1 identity.apple.com
- 127.0.0.1 iforgot.apple.com
- 127.0.0.1 images.apple.com
- 127.0.0.1 index.apple.com
- 127.0.0.1 init.apple.com
- 127.0.0.1 investor.apple.com
- 127.0.0.1 iphone.apple.com
- 127.0.0.1 itunes.apple.com
- 127.0.0.1 itunespartner.apple.com
- 127.0.0.1 jobs.apple.com
- 127.0.0.1 k.apple.com
- 127.0.0.1 lists.apple.com
- 127.0.0.1 locate.apple.com
- 127.0.0.1 macos.apple.com
- 127.0.0.1 manuals.info.apple.com
- 127.0.0.1 manuals01.info.apple.com
- 127.0.0.1 manuals02.info.apple.com
- 127.0.0.1 manuals03.info.apple.com
- 127.0.0.1 manuals04.info.apple.com
- 127.0.0.1 maps.apple.com
- 127.0.0.1 mapsconnect.apple.com
- 127.0.0.1 meetingroom.apple.com
- 127.0.0.1 mfi.apple.com
- 127.0.0.1 mobile.apple.com
- 127.0.0.1 mobileaccess.apple.com
- 127.0.0.1 movies.apple.com
- 127.0.0.1 movietrailers.apple.com
- 127.0.0.1 myaccess-it.apple.com
- 127.0.0.1 myaccess.apple.com
- 127.0.0.1 mynews.apple.com
- 127.0.0.1 mystore.apple.com
- 127.0.0.1 news.apple.com
- 127.0.0.1 nr.apple.com
- 127.0.0.1 opensource.apple.com
- 127.0.0.1 podcastsconnect.apple.com
- 127.0.0.1 portal.apple.com
- 127.0.0.1 quicktime.apple.com
- 127.0.0.1 radar.apple.com
- 127.0.0.1 register.apple.com
- 127.0.0.1 relay.apple.com
- 127.0.0.1 relay1.apple.com
- 127.0.0.1 relay11.apple.com
- 127.0.0.1 relay12.apple.com
- 127.0.0.1 relay13.apple.com
- 127.0.0.1 relay14.apple.com
- 127.0.0.1 relay15.apple.com
- 127.0.0.1 relay2.apple.com
- 127.0.0.1 relay3.apple.com
- 127.0.0.1 relay4.apple.com
- 127.0.0.1 relay5.apple.com
- 127.0.0.1 remoteadvisor.apple.com
- 127.0.0.1 remoteadvisor1.apple.com
- 127.0.0.1 remoteadvisor2.apple.com
- 127.0.0.1 reportaproblem.apple.com
- 127.0.0.1 s.apple.com
- 127.0.0.1 safari-extensions.apple.com
- 127.0.0.1 sales.apple.com
- 127.0.0.1 salesresources.apple.com
- 127.0.0.1 school.apple.com
- 127.0.0.1 selfsolve.apple.com
- 127.0.0.1 servers.apple.com
- 127.0.0.1 service.apple.com
- 127.0.0.1 sift.apple.com
- 127.0.0.1 signin.apple.com
- 127.0.0.1 signin.info.apple.com
- 127.0.0.1 source.apple.com
- 127.0.0.1 ssl.apple.com
- 127.0.0.1 sso.apple.com
- 127.0.0.1 store.apple.com
- 127.0.0.1 support.apple.com
- 127.0.0.1 support01.apple.com
- 127.0.0.1 support02.apple.com
- 127.0.0.1 support03.apple.com
- 127.0.0.1 support04.apple.com
- 127.0.0.1 support05.apple.com
- 127.0.0.1 supportprofile.apple.com
- 127.0.0.1 supporttest.apple.com
- 127.0.0.1 survey.apple.com
- 127.0.0.1 survey2.apple.com
- 127.0.0.1 swdlp.apple.com
- 127.0.0.1 time.apple.com
- 127.0.0.1 time1.apple.com
- 127.0.0.1 time2.apple.com
- 127.0.0.1 time3.apple.com
- 127.0.0.1 time4.apple.com
- 127.0.0.1 time5.apple.com
- 127.0.0.1 tips.apple.com
- 127.0.0.1 trailers.apple.com
- 127.0.0.1 training.apple.com
- 127.0.0.1 trainingevents.apple.com
- 127.0.0.1 uptodate.apple.com
- 127.0.0.1 volume.apple.com
- 127.0.0.1 war.apple.com
- 127.0.0.1 www1.apple.com
- 127.0.0.1 wwwtest.apple.com
- 127.0.0.1 xml.apple.com
- 127.0.0.1 xp.apple.com
- 127.0.0.1 xp2.apple.com
- 127.0.0.1 virustotal.com
- 127.0.0.1 www.virustotal.com
Other Details
This Trojan connects to the following URL(s) to get the affected system's IP address:
- api.ipify.org
It does the following:
- It installs fake certificates without notifying the user.
- It terminates the following browsers:
- Safari
- Firefox
- Google Chrome
- It disables system updates.
- It installs the following in the affected system:
- brew
- tor
- socat
- It contains a list of its targeted financial institutions :
- *.cic.ch
- *.clientis.ch
- *.postfinance.ch
- *.ukb.ch
- *.urkb.ch
- *abs ch
- *acrevis.ch
- *aekbank.ch
- *akb.ch
- *alpharheintalbank.ch
- *apbank.ch
- *appkb.ch
- *arabbank.ch
- *baloise.ch
- *bancasempione.ch
- *bancazarattini.ch
- *bankbiz.ch
- *bankgantrisch.ch
- *bankhaus-jungholz.ch
- *bankleerau.ch
- *bankslm.ch
- *bankzimmerberg.ch
- *banquecramer.ch
- *banqueduleman.ch
- *banquethaler.com
- *bbobank.ch
- *bbva.ch
- *bcf.ch
- *bcge.ch
- *bcj.ch
- *bcn.ch
- *bcpconnect.com
- *bcv.ch
- *bcvs.ch
- *bekb.ch
- *bil.com
- *bkb.chs
- *blkb.ch
- *bnpparibas.com
- *bordier.com
- *bsibank.com
- *btv3banken.ch
- *ca-financements.ch
- *cash.ch
- *cbhbank.com
- *ce-riviera.ch
- *ceanet.ch
- *cedc.ch
- *cembra.ch
- *cen.ch
- *cimbanque.net
- *cmvsa.ch
- *commerzbank.com
- *corneronline.ch
- *coutts.com
- *credinvest.ch
- *credit-suisse.com
- *dcbank.ch
- *dominickco.ch
- *eek.ch
- *efginternational.com
- *ekaffoltern.ch
- *eki.ch
- *ekr.ch
- *ersparniskasse.ch
- *exane.com
- *falconpb.com
- *frankfurter-bankgesellschaft.com
- *gemeinschaftsbank.ch
- *gkb.ch
- *glarner-regionalbank.ch
- *glkb.ch
- *globalance-bank.com
- *gobanking.ch
- *hbl.ch
- *hsbcprivatebank.com
- *hypobank.ch
- *incorebank.ch
- *inlinea.ch
- *juliusbaer.com
- *leihkasse-stammheim.ch
- *lienhardt.ch
- *lukb.ch
- *maerki-baumann.ch
- *mirabaud.com
- *mmwarburg.ch
- *mybancaria.ch
- *neuehelvetischebank.ch
- *nkb.ch
- *nordea.ch
- *notenstein-laroche.ch
- *onba.ch
- *owkb.ch
- *pbgate.net
- *pbihag.ch
- *piguetgalland.ch
- *rahnbodmer.ch
- *raiffeisen.chs
- *rbm.ch
- *regiobank.ch
- *reyl.com
- *saanenbank.ch
- *sebgroup.com
- *shkb.ch
- *slbucheggberg.ch
- *slfrutigen.ch
- *slguerbetal.ch
- *slr.ch
- *slwynigen.ch
- *sparhafen.ch
- *sparkasse-dielsdorf.ch
- *sparkasse.ch
- *szkb.ch
- *trafina.ch
- *triba.ch
- *ubp.com
- *ubs.com
- *umtb.ch
- *valiant.ch
- *vermoegenszentrum.ch
- *vontobel.com
- *wir.ch
- *zkb.ch
- *zuercherlandbank.ch
- *zugerkb.ch
- bankthalwil.ch
- bernerlandb. nk.ch
- cic.ch
- clientis.ch
- cs.directnet.com
- ebanking.raiffeisen.ch
- tb.raiffeiendirect.ch
- ukb.ch
- urkb.ch
- It adds itself to the macOS Login Items named "AppStore"
- It installs the following files in the user's Launch Agents folder to redirect HTTP and HTTPS traffic:
- com.apple.Safari.pac.plist
- com.apple.Safari.proxy.plist
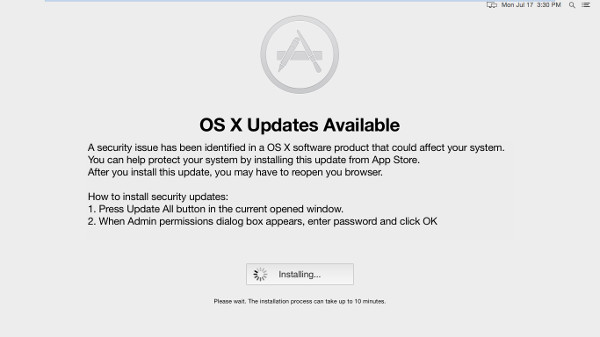
- It removes the system AppStore and opens a fake OSX update screen.
NOTES:
It displays the following fake system update application:
SOLUTION
Step 1
Search and delete these files
- /Users/YOUR USERNAME/Library/LaunchAgents/com.apple.Safari.proxy.plist
- /Users/YOUR USERNAME/Library/LaunchAgents/com.apple.Safari.pac.plist
Step 2
Scan your computer with your Trend Micro product to delete files detected as OSX_DOK.C. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
NOTES:
Solution:
Remove these strings added by the malware/grayware/spyware in the HOSTS file
Did this description help? Tell us how we did.


