HKTL_WEBPASSWORD.GA
PWS:MSIL/Mintluks.A (Microsoft),
Windows


Threat Type: Hacking Tool
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. It may be manually installed by a user.
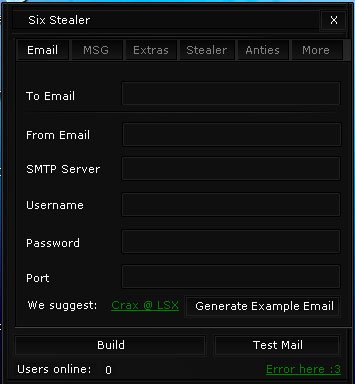
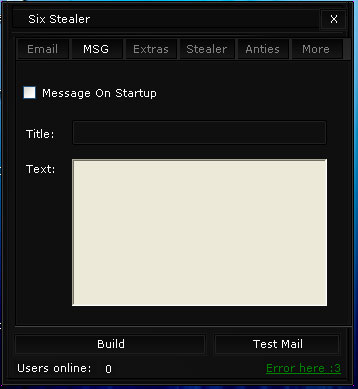
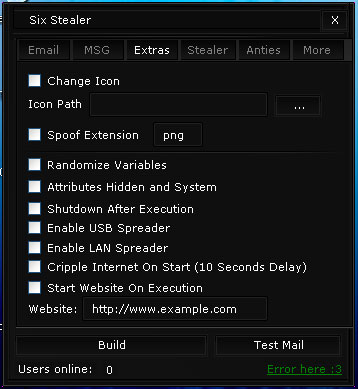
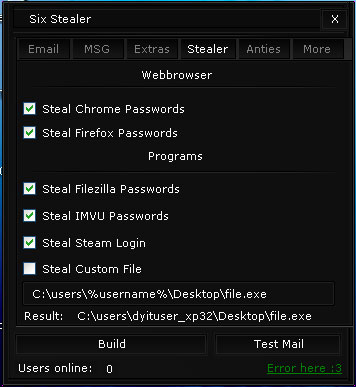
It uses a user interface (UI).
TECHNICAL DETAILS
Arrival Details
This hacking tool arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It may be manually installed by a user.
Other Details
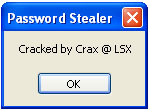
This hacking tool displays the following message boxes:
It drops the following file(s)/component(s):
- {User-defined path}\{User-defined filename}.exe
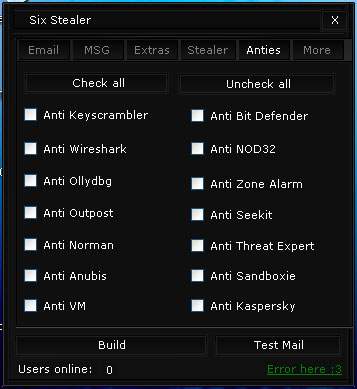
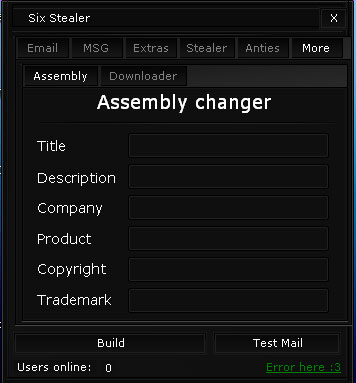
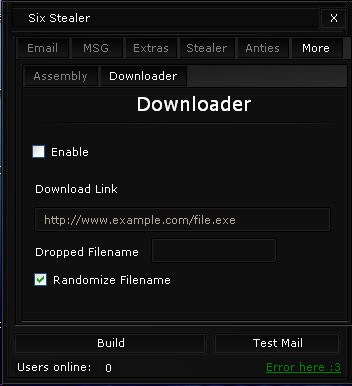
It uses the following user interfaces (UIs):
It does the following:
- Email stolen information to an address specified by the user
- Steal passwords from the following web browsers and programs:
- Chrome
- Firefox
- Filezilla
- IMVU
- Steam
- Steal any file
- Change its own file information
- Download files from urls specified by a user
- Can create the dropped file with the following evasion techniques:
- Anti Keyscrambler
- Anti Wireshark
- Anti Ollydbg
- Anti Outpost
- Anti Norman
- Anti Anubis
- Anti VM
- Anti AV Products
- Bit Defender
- NOD32
- Zone Alarm
- Seekit
- Threat Experts
- Kaspersky
- Anti Sandboxie
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as HKTL_WEBPASSWORD.GA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.