PE_SALITY.BV-O
RDN/Generic BackDoor (McAfee), Backdoor:MSIL/Noancooe.C (Microsoft), Win32/Injector.DONI (ESET-NOD32)
Windows


Threat Type: File infector
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This File infector arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It infects by appending its code to target host files.
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
TECHNICAL DETAILS
Arrival Details
This File infector arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This File infector drops the following copies of itself into the affected system:
- {random filename}. {exe/cmd/pif}
It drops the following files:
- %User Temp%\IXP000.TMP\@.cmd
- %User Temp%\IXP000.TMP\@.cm_
- %User Temp%\IXP000.TMP\@.cmdx
- %AppDataLocal%\CSIDL_
- %AppDataLocal%\CSIDL_X
- %User Temp%\{Random Numbers}.bat
- %User Temp%\{Random letters}.exe
- {Drive}\autorun.inf
- {Drive}\{Random Letters}.exe
- %User Temp%\IXP000.TMP\@.cmd.config
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista, 7, and 8.. %AppDataLocal% is the Local Application Data folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Application Data on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local on Windows Vista, 7, and 8.)
It adds the following processes:
- %System%\net1 stop MpsSvc
- cmd.exe /c echo on error resume next:CreateObject("WScript.Shell").Run "%User Temp%\IXP000.TMP\@.cmd",1: >"%User Startup%\{random letter}.vbs"
- cmd.exe /c ""%User Temp%\{random numbers}.bat" "%User Temp%\IXP000.TMP\@.cmd" "
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %User Startup% is the current user's Startup folder, which is usually C:\Windows\Profiles\{user name}\Start Menu\Programs\Startup on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu\Programs\Startup on Windows NT, C:\Documents and Settings\{User name}\Start Menu\Programs\Startup on Windows XP, or C:\Users\{user name}\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup on Windows Vista, 7, and 8.)
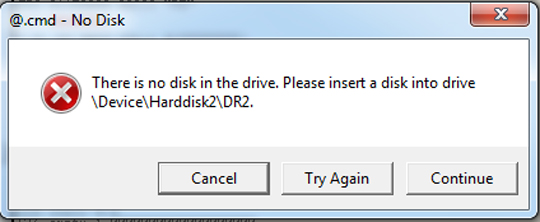
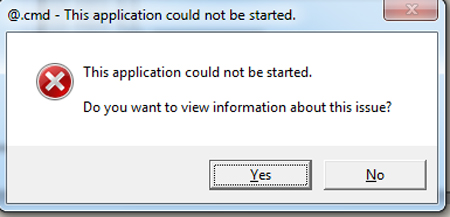
It displays the following fake error messages:
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- qazwsxedc
- uxJLpe1m
Autostart Technique
This File infector adds the following registry entries to enable its automatic execution at every system startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\RunOnce
wextract_cleanup0 = "rundll32.exe %System%\advpack.dll,DelNodeRunDLL32 "%User Temp%\IXP000.TMP\"
Other System Modifications
This File infector adds the following registry entries:
HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications
HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\
GeoExpert
HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\
GeoExpert\Recent File List
HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\
GeoExpert\Settings
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLUA = "0"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Explorer\
Advanced
Hidden = "2"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center
AntiVirusOverride = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center
AntiVirusDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center
FirewallDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center
FirewallOverride = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center
UpdatesDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center
UacDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center\Svc
AntiVirusOverride = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center\Svc
AntiVirusDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center\Svc
FirewallDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center\Svc
FirewallOverride = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center\Svc
UpdatesDisableNotify = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Security Center\Svc
UacDisableNotify = "1"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Internet Settings
GlobalUserOffline = "0"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Policies\
System
EnableLUA = "0"
HKEY_CURRENT_USER\Software\{Random}
d{Random}_{Random} = "{Random}"
File Infection
This File infector infects the following file types:
- .exe
- .scr
It infects by appending its code to target host files.
Propagation
This File infector drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
Note: The order of autorun.inf strings may vary and may contain a combination of uppercase and lowercase letters.
;{garbage characters}
[AutoRun]
;{garbage characters}
;{garbage characters}
open = {Random Filename}.{pif/cmd/exe}
;ShElL\eXPLOre\coMMAnD={Random Filename}.{pif/cmd/exe}
;
shElL\opEn\Default=1
;{garbage characters}
sHell\Open\cOMMAnD= {Random Filename}.{pif/cmd/exe}
sHElL\AuToplAy\cOMmAnD ={Random Filename}.{pif/cmd/exe}
Process Termination
This File infector terminates the following services if found on the affected system:
- Agnitum Client Security Service
- ALG
- Amon monitor
- aswUpdSv
- avast! Antivirus
- avast! Mail Scanner
- avast! Web Scanner
- BackWeb Plug-in - 4476822
- BGLiveSvc
- BlackICE
- CAISafe
- ccEvtMgr
- ccProxy
- ccSetMgr
- F-Prot Antivirus Update Monitor
- fsbwsys
- FSDFWD
- F-Secure Gatekeeper Handler Starter
- fshttps
- InoRPC
- InoRT
- InoTask
- ISSVC
- LavasoftFirewall
- LIVESRV
- McAfeeFramework
- McShield
- McTaskManager
- navapsvc
- NOD32krn
- NPFMntor
- NSCService
- Outpost Firewall main module
- OutpostFirewall
- PAVFIRES
- PAVFNSVR
- PavProt
- PavPrSrv
- PAVSRV
- PcCtlCom
- PersonalFirewal
- PREVSRV
- ProtoPort Firewall service
- PSIMSVC
- RapApp
- SmcService
- SNDSrvc
- SPBBCSvc
- Symantec Core LC
- Tmntsrv
- TmPfw
- tmproxy
- UmxAgent
- UmxCfg
- UmxLU
- UmxPol
- vsmon
- VSSERV
- WebrootDesktopFirewallDataService
- WebrootFirewall
- XCOMM
It terminates processes or services that contain any of the following strings if found running in the affected system's memory:
- ALERTSVC
- ALMON.
- ALOGSERV
- ALSVC.
- AMON.
- ANTI-TROJAN.
- ANTIVIR
- ANTS.
- APVXDWIN.
- ARMOR2NET.
- ASHAVAST.
- ASHDISP.
- ASHENHCD.
- ASHMAISV.
- ASHPOPWZ.
- ASHSERV.
- ASHSIMPL.
- ASHSKPCK.
- ASHWEBSV.
- ASWUPDSV.
- ATCON.
- ATUPDATER.
- ATWATCH.
- AUPDATE.
- AUTODOWN.
- AUTOTRACE.
- AUTOUPDATE.
- AVCIMAN.
- AVCONSOL.
- AVENGINE.
- AVGAMSVR.
- AVGCC.
- AVGCC32.
- AVGCTRL.
- AVGEMC.
- AVGFWSRV.
- AVGNT.
- AVGNTDD
- AVGNTMGR
- AVGSERV.
- AVGUARD.
- AVGUPSVC.
- AVINITNT.
- AVKSERV.
- AVKSERVICE.
- AVKWCTL.
- AVP32.
- AVPCC.
- AVPM.
- AVAST
- AVSCHED32.
- AVSYNMGR.
- AVWUPD32.
- AVWUPSRV.
- AVXMONITOR9X.
- AVXMONITORNT.
- AVXQUAR.
- BACKWEB-4476822.
- BDMCON.
- _AVPM.
- A2GUARD.
- AAVSHIELD.
- AVAST
- ADVCHK.
- AHNSD.
- AIRDEFENSE
- CMGRDIAN.
- CUREIT
- DEFWATCH.
- DOORS.
- DRVIRUS.
- DRWADINS.
- DRWEB32W.
- DRWEBSCD.
- DRWEBUPW.
- ESCANH95.
- ESCANHNT.
- EWIDOCTRL.
- EZANTIVIRUSREGISTRATIONCHECK.
- F-AGNT95.
- FAMEH32.
- FAST.
- FCH32.
- FILEMON
- FIRESVC.
- FIRETRAY.
- FIREWALL.
- FPAVUPDM.
- F-PROT95.
- FRESHCLAM.
- FSAV32.
- FSAVGUI.
- FSBWSYS.
- F-SCHED.
- FSDFWD.
- FSGK32.
- FSGK32ST.
- FSGUIEXE.
- FSM32.
- FSMA32.
- FSMB32.
- FSPEX.
- FSSM32.
- F-STOPW.
- GCASDTSERV.
- GCASSERV.
- GIANTANTISPYWAREMAIN.
- GIANTANTISPYWAREUPDATER.
- GUARDGUI.
- GUARDNT.
- HREGMON.
- HRRES.
- HSOCKPE.
- HUPDATE.
- IAMAPP.
- IAMSERV.
- ICLOAD95.
- ICLOADNT.
- ICMON.
- ICSSUPPNT.
- ICSUPP95.
- ICSUPPNT.
- IFACE.
- INETUPD.
- INOCIT.
- INORPC.
- INORT.
- INOTASK.
- INOUPTNG.
- IOMON98.
- ISAFE.
- ISATRAY.
- ISRV95.
- ISSVC.
- KAVMM.
- KAVPF.
- KAVPFW.
- KAVSTART.
- KAVSVC.
- KAVSVCUI.
- KMAILMON.
- KPFWSVC.
- KWATCH.
- LOCKDOWN2000.
- LOGWATNT.
- LUALL.
- LUCOMSERVER.
- LUUPDATE.
- MCAGENT.
- MCMNHDLR.
- MCREGWIZ.
- MCUPDATE.
- MCVSSHLD.
- MINILOG.
- MYAGTSVC.
- MYAGTTRY.
- NAVAPSVC.
- NAVAPW32.
- NAVLU32.
- NAVW32.
- NOD32.
- NEOWATCHLOG.
- NEOWATCHTRAY.
- NISSERV
- NISUM.
- NMAIN.
- NOD32
- NORMIST.
- NOTSTART.
- NPAVTRAY.
- NPFMNTOR.
- NPFMSG.
- NPROTECT.
- NSCHED32.
- NSMDTR.
- NSSSERV.
- NSSTRAY.
- NTRTSCAN.
- NTXCONFIG.
- NUPGRADE.
- NVC95.
- NVCOD.
- NVCTE.
- NVCUT.
- NWSERVICE.
- OFCPFWSVC.
- OUTPOST.
- PAVFIRES.
- PAVFNSVR.
- PAVKRE.
- PAVPROT.
- PAVPROXY.
- PAVPRSRV.
- PAVSRV51.
- PAVSS.
- PCCGUIDE.
- PCCIOMON.
- PCCNTMON.
- PCCPFW.
- PCCTLCOM.
- PCTAV.
- PERSFW.
- PERTSK.
- PERVAC.
- PNMSRV.
- POP3TRAP.
- POPROXY.
- PREVSRV.
- PSIMSVC.
- QHM32.
- QHONLINE.
- QHONSVC.
- QHPF.
- QHWSCSVC.
- RAVMON.
- RAVTIMER.
- REALMON.
- REALMON95.
- RFWMAIN.
- RTVSCAN.
- RTVSCN95.
- RULAUNCH.
- SAVADMINSERVICE.
- SAVMAIN.
- SAVPROGRESS.
- SAVSCAN.
- SCAN32.
- SCANNINGPROCESS.
- CUREIT.
- SDHELP.
- SHSTAT.
- SITECLI.
- SPBBCSVC.
- SPHINX.
- SPIDERML.
- SPIDERNT.
- SPIDERUI.
- SPYBOTSD.
- SPYXX.
- SS3EDIT.
- STOPSIGNAV.
- SWAGENT.
- SWDOCTOR.
- SWNETSUP.
- SYMLCSVC.
- SYMPROXYSVC.
- SYMSPORT.
- SYMWSC.
- SYNMGR.
- TAUMON.
- TBMON.
- AVAST
- TDS-3.
- TEATIMER.
- TFAK.
- THAV.
- THSM.
- TMAS.
- TMLISTEN.
- TMNTSRV.
- TMPFW.
- TMPROXY.
- TNBUTIL.
- TRJSCAN.
- UP2DATE.
- VBA32ECM.
- VBA32IFS.
- VBA32LDR.
- VBA32PP3.
- VBSNTW.
- VCHK.
- VCRMON.
- VETTRAY.
- VIRUSKEEPER.
- VPTRAY.
- VRFWSVC.
- VRMONNT.
- VRMONSVC.
- VRRW32.
- VSECOMR.
- VSHWIN32.
- VSMON.
- VSSERV.
- VSSTAT.
- WATCHDOG.
- WEBPROXY.
- WEBSCANX.
- WEBTRAP.
- WGFE95.
- WINAW32.
- WINROUTE.
- WINSS.
- WINSSNOTIFY.
- WRADMIN.
- WRCTRL.
- XCOMMSVR.
- ZATUTOR.
- ZAUINST.
- ZLCLIENT.
- ZONEALARM.
- BDNEWS.
- BDOESRV.
- BDSS.
- BDSUBMIT.
- BDSWITCH.
- BLACKD.
- BLACKICE.
- CAFIX.
- CCAPP.
- CCEVTMGR.
- CCPROXY.
- CCSETMGR.
- CFIAUDIT.
- CLAMTRAY.
- CLAMWIN.
- CLAW95.
- CLAW95CF.
- CLEANER.
- CLEANER3.
- CLISVC.
Download Routine
This File infector connects to the following URL(s) to download its component file(s):
- http://{BLOCKED}nwengen.com/wordpress/wp-content/themes/flozo/images/styles.gif?1af8c0=7070464
- http://{BLOCKED}amps.com/wp-content/themes/StampVamps/images/styles.gif?1b0a7b=12405085
- http://static.{BLOCKED}mains.com/images/logo_huge_domains.gif
- http://{BLOCKED}ockassociates.com/wp-content/themes/Foundation/images/styles.gif?1b1506=5324562
- http://{BLOCKED}smali.fr/wp-content/themes/mali/styles.gif?1b22cc=3556760
- http://{BLOCKED}reshining.co.uk/wp-content/themes/make/styles.gif?1b36a9=8917325
- http://iqhouse.{BLOCKED}v.ua/wp-content/themes/iqhouse/img/style.gif?1b5457=14328504
- http://{BLOCKED}nwengen.com/wordpress/wp-content/themes/flozo/images/styles.gif?1af8c0=7070464
Other Details
This File infector checks for the presence of the following process(es):
- VBoxService.exe
- vmtoolsd.exe
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
- wextract_cleanup0 = "rundll32.exe %System%\advpack.dll,DelNodeRunDLL32 "%User Temp%\IXP000.TMP\"
- wextract_cleanup0 = "rundll32.exe %System%\advpack.dll,DelNodeRunDLL32 "%User Temp%\IXP000.TMP\"
- In HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications
- HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\GeoExper
- HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\GeoExper
- In HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\GeoExpert\Recent File List
- HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\GeoExpert\Settings
- HKEY_CURRENT_USER\Software\Local AppWizard-Generated Applications\GeoExpert\Settings
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLUA = "0"
- EnableLUA = "0"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
- Hidden = "2"
- Hidden = "2"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center
- AntiVirusOverride = "1"
- AntiVirusOverride = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center
- AntiVirusDisableNotify = "1"
- AntiVirusDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center
- FirewallDisableNotify = "1"
- FirewallDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center
- FirewallOverride = "1"
- FirewallOverride = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center
- UpdatesDisableNotify = "1"
- UpdatesDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center
- UacDisableNotify = "1"
- UacDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Svc
- AntiVirusOverride = "1"
- AntiVirusOverride = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Svc
- AntiVirusDisableNotify = "1"
- AntiVirusDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Svc
- FirewallDisableNotify = "1"
- FirewallDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Svc
- FirewallOverride = "1"
- FirewallOverride = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Svc
- UpdatesDisableNotify = "1"
- UpdatesDisableNotify = "1"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Svc
- UacDisableNotify = "1"
- UacDisableNotify = "1"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings
- GlobalUserOffline = "0"
- GlobalUserOffline = "0"
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- EnableLUA = "0"
- EnableLUA = "0"
- In HKEY_CURRENT_USER\Software\{Random}
- d{Random}_{Random} = "{Random}"
- d{Random}_{Random} = "{Random}"
Step 4
Search and delete this file
- %User Temp%\IXP000.TMP\@.cmd
- %User Temp%\IXP000.TMP\@.cm_
- %User Temp%\IXP000.TMP\@.cmdx
- %AppDataLocal%\CSIDL_
- %AppDataLocal%\CSIDL_X
- %User Temp%\{Random Numbers}.bat
- %User Temp%\{Random Letters}.exe
- {Drive}\autorun.inf
- {Drive}\{Random Letters}.exe
- %User Temp%\IXP000.TMP\@.cmd.config
Step 5
Search and delete AUTORUN.INF files created by PE_SALITY.BV-O that contain these strings
- ;{garbage characters}
[AutoRun]
;{garbage characters}
;{garbage characters}
open = {Random Filename}.{pif/cmd/exe}
;
ShElL\eXPLOre\coMMAnD={Random Filename}.{pif/cmd/exe}
;
shElL\opEn\Default=1
;{garbage characters}
sHell\Open\cOMMAnD= {Random Filename}.{pif/cmd/exe}
sHElL\AuToplAy\cOMmAnD ={Random Filename}.{pif/cmd/exe}
Step 6
Scan your computer with your Trend Micro product to delete files detected as PE_SALITY.BV-O. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


