TROJ_CRYPWAL.YOI
Trojan.Win32.Yakes.jzyg (Kaspersky); Trojan.Cryptodefense (Symantec); Trojan:Win32/Dynamer!ac (Microsoft); Mal/MSIL-NB (Sophos); W32/CRYPWAL.YOI!tr (Fortinet)
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
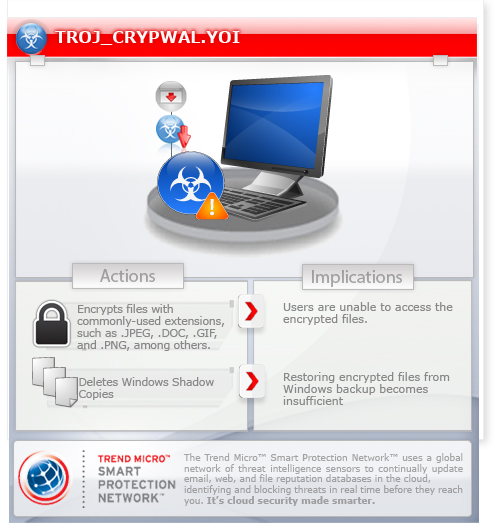
This variant is also known as CryptoWall 3.0. Apart from its encryption technique, it also deletes Windows Shadow Copies - making restoration of files difficult. This version comes together with a FAREIT spyware variant.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It modifies registry entries to disable various system services. This action prevents most of the system functions to be used.
It connects to certain websites to send and receive information.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops the following copies of itself into the affected system:
- %System Root%\{random 8 characters}\{random 8 characters}.exe
- %Application Data%\{random 8 characters}.exe
- %User Startup%\{random 8 characters}.exe
(Note: %System Root% is the Windows root folder, where it usually is C:\ on all Windows operating system versions.. %Application Data% is the Application Data folder, where it usually is C:\Documents and Settings\{user name}\Application Data on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Roaming on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %User Startup% is the current user's Startup folder, which is usually C:\Windows\Profiles\{user name}\Start Menu\Programs\Startup on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu\Programs\Startup on Windows NT, and C:\Documents and Settings\{User name}\Start Menu\Programs\Startup.)
It drops the following files:
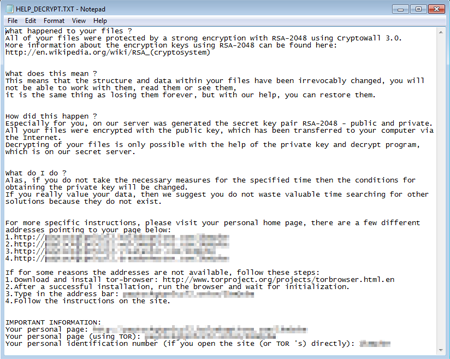
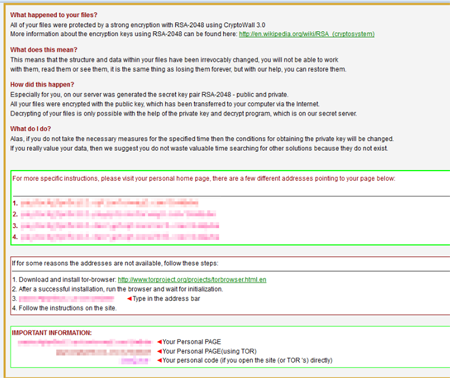
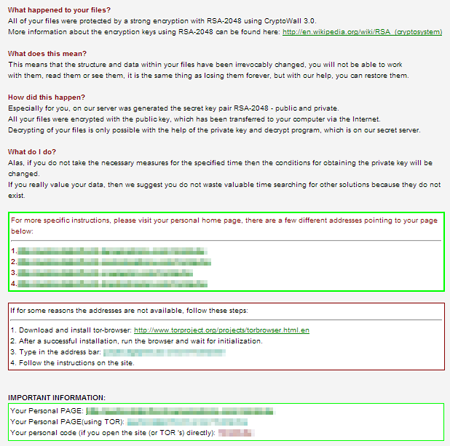
- %User Startup%\HELP_DECRYPT.HTML
- %User Startup%\HELP_DECRYPT.PNG
- %User Startup%\HELP_DECRYPT.TXT
- %User Startup%\HELP_DECRYPT.URL
(Note: %User Startup% is the current user's Startup folder, which is usually C:\Windows\Profiles\{user name}\Start Menu\Programs\Startup on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu\Programs\Startup on Windows NT, and C:\Documents and Settings\{User name}\Start Menu\Programs\Startup.)
It drops and executes the following files:
- %Desktop%\HELP_DECRYPT.HTML
- %Desktop%\HELP_DECRYPT.PNG
- %Desktop%\HELP_DECRYPT.TXT
- %Desktop%\HELP_DECRYPT.URL
(Note: %Desktop% is the desktop folder, where it usually is C:\Documents and Settings\{user name}\Desktop in Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\Desktop in Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It adds the following processes:
- explorer.exe
- svchost.exe
It is injected into the following processes running in memory:
- created explorer.exe
- created svchost.exe
Autostart Technique
This Trojan adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\RunOnce
*{random 6 characters} = "%System Root%\{random 8 characters}\{random 8 characters}.exe" (for Windows Vista and above only)
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\RunOnce
*{random 7 characters} = "%Application Data%\{random 8 characters}.exe" (for Windows Vista and above only)
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{random 7 characters} = "%System Root%\{random 8 characters}\{random 8 characters}.exe"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{random 8 characters} = "%Application Data%\{random 8 characters}.exe"
Other System Modifications
This Trojan adds the following registry keys:
HKEY_CURRENT_USER\Software\{UID}
HKEY_CURRENT_USER\Software\{UID}\
{random key}
It adds the following registry entries:
HKEY_CURRENT_USER\Software\{UID}
{random 2 characters} = "{RSA PUBLIC KEY}"
HKEY_CURRENT_USER\Software\{UID}
{random 2 characters} = "{contents of HELP_DECRYPT.TXT}"
HKEY_CURRENT_USER\Software\{UID}
{random 2 characters} = "{contents of HELP_DECRYPT.HTML}"
HKEY_CURRENT_USER\Software\{UID}
{random 2 characters} = "{contents of HELP_DECRYPT.URL}"
HKEY_CURRENT_USER\Software\{UID}\
{random key}
{Path and file of encrypted file} = "{hex values}"
It modifies the following registry entries:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\SystemRestore
DisableSR = "1"
(Note: The default value data of the said registry entry is 0.)
It modifies registry entries to disable the following system services:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\ERSvc
Start = "4"
(Note: The default value data of the said registry entry is 2.)
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\wscsvc
Start = "4"
(Note: The default value data of the said registry entry is 2.)
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\BITS
Start = "4"
(Note: The default value data of the said registry entry is 2.)
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\wuauserv
Start = "4"
(Note: The default value data of the said registry entry is 2.)
Information Theft
This Trojan gathers the following data:
- Unique Identifier (UID)
- Machine Screenshot
Other Details
This Trojan connects to the following URL(s) to get the affected system's IP address:
- ip-addr.es
- curlmyip.com
- myexternalip.com
It connects to the following website to send and receive information:
- {BLOCKED}a.com/img3.php
- {BLOCKED}de.com/img2.php
- {BLOCKED}wohnungen-diana.com/img1.php
- {BLOCKED}easset.com/img5.php
- {BLOCKED}c.us/img4.php
- {BLOCKED}dtile.net/img3.php
- {BLOCKED}bjx.com/img2.php
- {BLOCKED}talmd.com/img1.php
- {BLOCKED}alaria.org/img5.php
- {BLOCKED}9.com/img3.php
- {BLOCKED}on.com/img2.php
- {BLOCKED}oft.com/img1.php
- {BLOCKED}iaunited.com/img5.php
- {BLOCKED}oosphoto.com/img4.php
- {BLOCKED}orld.com/img3.php
- {BLOCKED}urch.com/img2.php
- {BLOCKED}rofreshional.com/img1.php
- {BLOCKED}hae.com/img4.php
- {BLOCKED}9.com/img2.php
- 90.{BLOCKED}nd.info/img1.php
- {BLOCKED}an.com/img1.php
- {BLOCKED}muslim-online.com/img5.php
- {BLOCKED}m.com/img4.php
- {BLOCKED}zateonline.com/img3.php
- {BLOCKED}yber.com/img2.php
- {BLOCKED}et.com/img1.php
- {BLOCKED}-ng.com/img5.php
- {BLOCKED}8.com/img5.php
- {BLOCKED}n-guvenlik.com/img4.php
It encrypts files with the following extensions:
- 3dm
- 3ds
- 3fr
- 3g2
- 3gp
- 3pr
- 7z
- ab4
- accdb
- accde
- accdr
- accdt
- ach
- acr
- act
- adb
- ads
- agdl
- ai
- ait
- al
- apj
- arw
- asf
- asm
- asp
- asx
- avi
- awg
- back
- backup
- backupdb
- bak
- bank
- bay
- bdb
- bgt
- bik
- bkp
- blend
- bpw
- c
- cdf
- cdr
- cdr3
- cdr4
- cdr5
- cdr6
- cdrw
- cdx
- ce1
- ce2
- cer
- cfp
- cgm
- cib
- class
- cls
- cmt
- cpi
- cpp
- cr2
- craw
- crt
- crw
- cs
- csh
- csl
- csv
- dac
- db
- db3
- dbf
- db-journal
- dc2
- dcr
- dcs
- ddd
- ddoc
- ddrw
- dds
- der
- des
- design
- dgc
- djvu
- dng
- doc
- docm
- docx
- dot
- dotm
- dotx
- drf
- drw
- dtd
- dwg
- dxb
- dxf
- dxg
- eml
- eps
- erbsql
- erf
- exf
- fdb
- ffd
- fff
- fh
- fhd
- fla
- flac
- flv
- fpx
- fxg
- gray
- grey
- gry
- h
- hbk
- hpp
- ibank
- ibd
- ibz
- idx
- iif
- iiq
- incpas
- indd
- java
- jpe
- jpeg
- jpg
- kc2
- kdbx
- kdc
- key
- kpdx
- lua
- m
- m4v
- max
- mdb
- mdc
- mdf
- mef
- mfw
- mmw
- moneywell
- mos
- mov
- mp3
- mp4
- mpg
- mrw
- msg
- myd
- nd
- ndd
- nef
- nk2
- nop
- nrw
- ns2
- ns3
- ns4
- nsd
- nsf
- nsg
- nsh
- nwb
- nx2
- nxl
- nyf
- oab
- obj
- odb
- odc
- odf
- odg
- odm
- odp
- ods
- odt
- oil
- orf
- ost
- otg
- oth
- otp
- ots
- ott
- p12
- p7b
- p7c
- pab
- pages
- pas
- pat
- pcd
- pct
- pdb
- pdd
- pef
- pem
- pfx
- php
- pl
- plc
- pot
- potm
- potx
- ppam
- pps
- ppsm
- ppsx
- ppt
- pptm
- pptx
- prf
- ps
- psafe3
- psd
- pspimage
- pst
- ptx
- py
- qba
- qbb
- qbm
- qbr
- qbw
- qbx
- qby
- r3d
- raf
- rar
- rat
- raw
- rdb
- rm
- rtf
- rw2
- rwl
- rwz
- s3db
- sas7bdat
- say
- sd0
- sda
- sdf
- sldm
- sldx
- sql
- sqlite
- sqlite3
- sqlitedb
- sr2
- srf
- srt
- srw
- st4
- st5
- st6
- st7
- st8
- std
- sti
- stw
- stx
- svg
- swf
- sxc
- sxd
- sxg
- sxi
- sxi
- sxm
- sxw
- tex
- tga
- thm
- tlg
- txt
- vob
- wallet
- wav
- wb2
- wmv
- wpd
- wps
- x11
- x3f
- xis
- xla
- xlam
- xlk
- xlm
- xlr
- xls
- xlsb
- xlsm
- xlsx
- xlt
- xltm
- xltx
- xlw
- ycbcra
- yuv
- zip
- +MuhD
NOTES:
This Trojan searches all drives for files to encrypt except CD_ROM drive. It avoids encrypting files inside the following folders:
- .
- ..
- cache
- games
- nvidia
- packages
- Temp
- uvOyR
- Windows
- Y@Cs
It terminates and uninstalls itself if geo-location of the affected machine matches any of the following country codes:
- AM (ARMENIA)
- BY (BELARUS)
- IR (IRAN)
- KZ (KAZAKHSTAN)
- RS (SERBIA)
- RU (RUSSIA)
- UA (UKRAINE)
It deletes shadow copies by executing the following command:
- vssadmin.exe Delete Shadows /All /Quiet
It drops HELP_DECRYPT.HTML, HELP_DECRYPT.PNG, HELP_DECRYPT.TXT and HELP_DECRYPT.URL to all folders where files are encrypted.
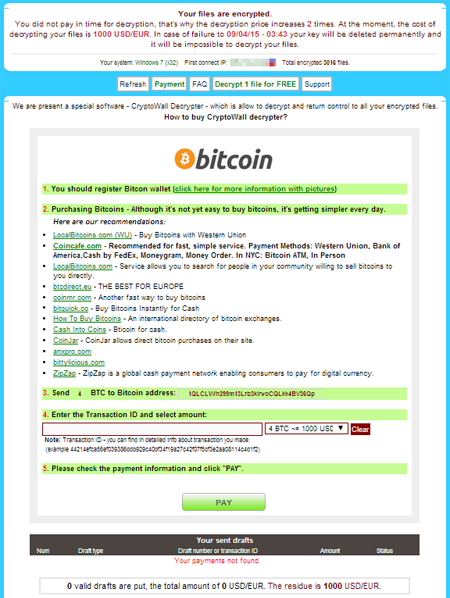
It opens the dropped ransom notes HELP_DECRYPT.TXT, HELP_DECRYPT.PNG and HELP_DECRYPT.HTML:
It demands payment for using decryption service:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product and note files detected as TROJ_CRYPWAL.YOI
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {random 7 characters} = "%System Root%\{random 8 characters}\{random 8 characters}.exe"
- {random 7 characters} = "%System Root%\{random 8 characters}\{random 8 characters}.exe"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {random 8 characters} = "%Application Data%\{random 8 characters}.exe"
- {random 8 characters} = "%Application Data%\{random 8 characters}.exe"
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- *{random 6 characters} = "%System Root%\{random 8 characters}\{random 8 characters}.exe" (for Windows Vista and above only)
- *{random 6 characters} = "%System Root%\{random 8 characters}\{random 8 characters}.exe" (for Windows Vista and above only)
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- *{random 7 characters} = "%Application Data%\{random 8 characters}.exe" (for Windows Vista and above only)
- *{random 7 characters} = "%Application Data%\{random 8 characters}.exe" (for Windows Vista and above only)
Step 6
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software
- {UID}
- {UID}
Step 7
Search and delete this file
- HELP_DECRYPT.HTML
- HELP_DECRYPT.PNG
- HELP_DECRYPT.TXT
- HELP_DECRYPT.URL
Step 8
Restore these modified registry values
Important:Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this only if you know how to or you can seek your system administrator's help. You may also check out this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore
- From: DisableSR = "1"
To: DisableSR = 0
- From: DisableSR = "1"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\ERSvc
- From: Start = "4"
To: Start = 2
- From: Start = "4"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\wscsvc
- From: Start = "4"
To: Start = 2
- From: Start = "4"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\BITS
- From: Start = "4"
To: Start = 2
- From: Start = "4"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\wuauserv
- From: Start = "4"
To: Start = 2
- From: Start = "4"
Step 9
Restart in normal mode and scan your computer with your Trend Micro product for files detected as TROJ_CRYPWAL.YOI. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.