Last month, we have seen cybercriminals use the popularity of apps like Instagram and Angry Birds Space to deliver malware on Android phones. This time, we spotted the same social engineering tactic using Adobe's name.
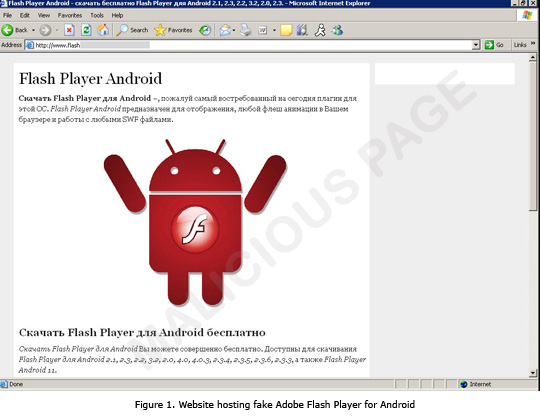
This webpage is also found to be hosted on Russian domains, similar to the fake Instagram and Angry Birds Space apps that we previously reported. To further entice users into downloading the fake Adobe Flash Player app, the text on the webpage claims that it is fully compatible with any Android OS version:
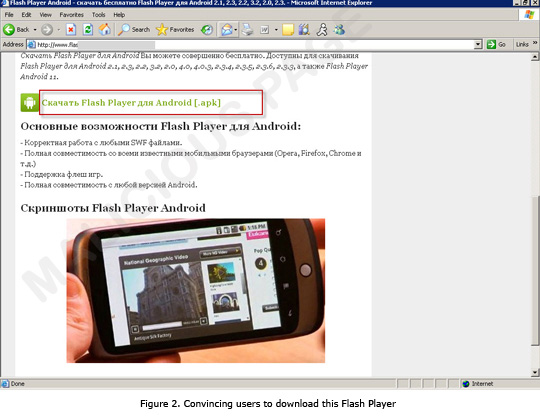
When users opt to download and install the said fake app, the site connects to another URL to download malicious .APK file, which Trend Micro detects as ANDROIDOS_BOXER.A. ANDROIDOS_BOXER.A is a premium service abuser, which means it sends messages to premium numbers without the user's permission, thus leading to unwanted charges. This type of Android malware is just one of the types we were able to identify in our infographic, A Snapshot of Android Threats.
Upon further investigation, we have seen a bunch of URLs that are hosted on the same IP as this particular website. Based on the naming alone used in these URLs, it appears that Android is a favorite target for cybercriminals behind this scheme.
Trend Micro protects your Android phones from accessing these malicious sites and from downloading malicious .APK files on your phones via the Mobile Security Personal Edition app. Apart from blocking access to malicious sites, our app scans each app you install to ensure your safety.
For your reference, Adobe Flash Player from Adobe Systems can be downloaded via the Google Play store.

