Spammers Use Covid-19 To Spread Lemon Duck Cryptominer
While the pandemic continues to affect millions of lives, spammers have continued to use COVID-19 as subject to lure recipients. In a campaign we have observed from March to June 2020, spammers aimed to spread Lemon Duck cryptocurrency-mining malware. A full analysis can be read in our article Lemon Duck Cryptominer Spreads through Covid-19 Themed Emails.
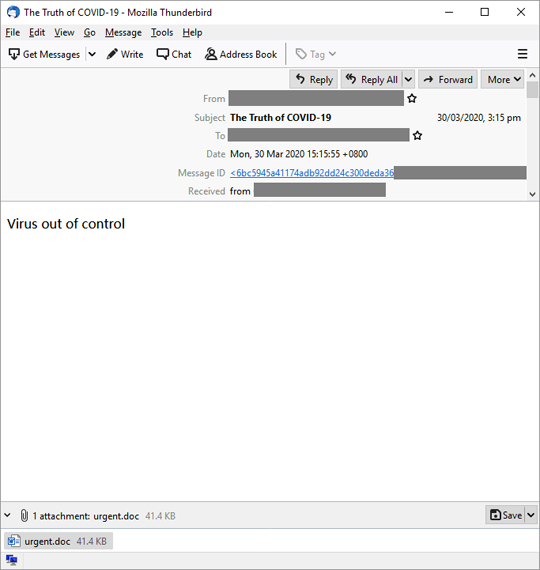
The malware comes as attachment to the spam, usually named urgent.doc (detected as Trojan.W97M.CVE20178570.AXC) or readme.zip (detected as Trojan.Win32.FLEMSDUCK.SM). These attachments contain a script file readme.js, which is detected as Trojan.JS.FLEMSDUCK.YPAD-A. Once infected with the malware, it has its own mailer script that it uses to propagate to other recipients. It does this by scraping the user's MS Outlook contact list and sends emails with the malicious attachment. This routine adds legitimacy to the email sent as it now comes from a trusted or known source, making the next recipient click on the attachments.
A multi-layered approach to security is needed for campaigns like this. Users can benefit from anti-spam protection as well as anti-malware solutions in place. Trend Micro users are already protected from these spam emails.
- ENGINE:8.5
- PATTERN:5506
