SWF_ANGZIA.A
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This malware exploits an Adobe Flash zero-day vulnerability. When a system is exploited successfully, it allows a remote user to execute arbitrary code on the system.
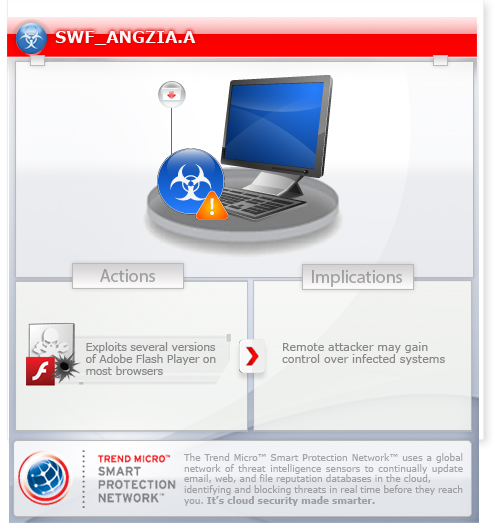
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This Trojan arrives as a component bundled with malware/grayware packages.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as a component bundled with malware/grayware packages.
Other Details
This Trojan is a zero-day exploit for the following vulnerability:
NOTES:
Once a compromised website is visited, the user's browser with a vulnerable version of Adobe Flash loads a specially-crafted Adobe Flash file. This exploit Adobe Flash file allows remote arbitrary code to execute on the affected system. Thus, allowing remote malicious users to deliver and execute payload on the affected system.
Affected software versions:
CVE-2015-0310
- Adobe Flash Player 16.0.0.257 and earlier versions
- Adobe Flash Player 13.0.0.260 and earlier 13.x versions
- Adobe Flash Player 11.2.202.429 and earlier versions for Linux
CVE-2015-0311
- Adobe Flash Player 16.0.0.287 and earlier versions for Windows and Macintosh
- Adobe Flash Player 13.0.0.262 and earlier 13.x versions
- Adobe Flash Player 11.2.202.438 and earlier versions for Linux
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Close all opened browser windows
Step 3
Scan your computer with your Trend Micro product to delete files detected as SWF_ANGZIA.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 4
Download and apply these security patches Refrain from using these products until the appropriate patches have been installed. Trend Micro advises users to download critical patches upon release by vendors.
Did this description help? Tell us how we did.


