RANSOM_KIMCILWARE.A
Windows, Linux


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
TECHNICAL DETAILS
Arrival Details
This malware arrives via the following means:
- This PHP script may be deployed and executed in a web server
Other Details
This Trojan does the following:
- It encrypts all files in the web server using Rijndael for its file encryption routine
NOTES:
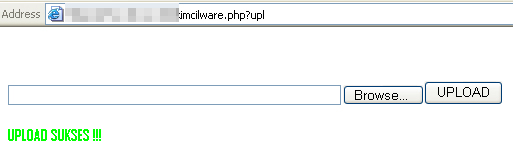
This ransomware can upload a file to the server by accessing the affected site with the variable upl:
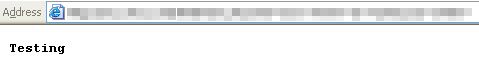
It is also capable of echoing the value inserted in the $_REQUEST variable cmd:
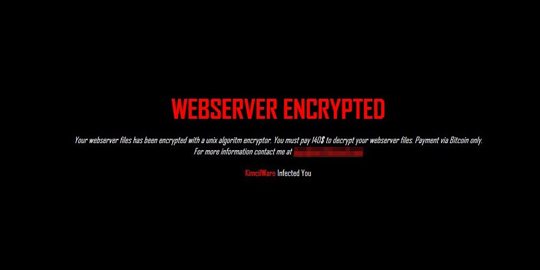
It displays the following ransom message:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Scan your computer with your Trend Micro product to delete files detected as RANSOM_KIMCILWARE.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


