Arrival Details
This Trojan arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops and executes the following files:
- %User Temp%\A9R{Random}.tmp\DOC34175250.docm ← contains malicious macro, detected as W2KM_DLOADR.YYTAV
It creates the following folders:
- %User Temp%\A9R{Random}.tmp
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Other Details
This Trojan does the following:
- It deletes the created folder and dropped file once it is closed.
NOTES:
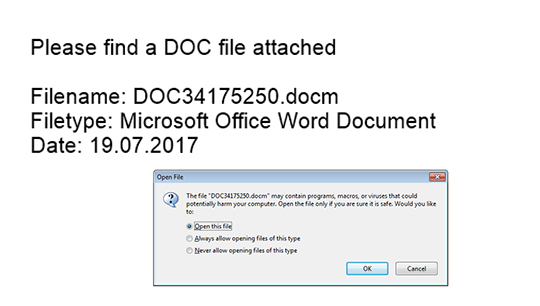
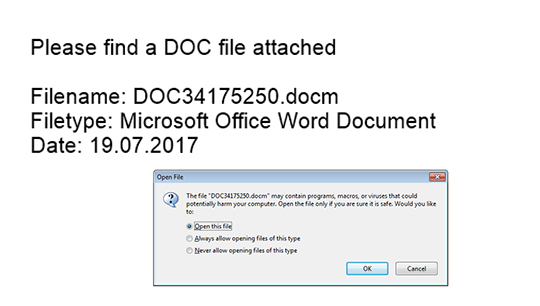
The PDF file contains the following fake details luring users to enable macro content/program:
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Remove malware/grayware files dropped/downloaded by PDF_DOCDROP.YYTAV. (Note: Please skip this step if the threats listed below have already been removed.)
Step 4
Search and delete these folders
[ Learn More ]
[ back ]
Please make sure you check the
Search Hidden Files and Folders checkbox in the More advanced options option to include all hidden folders in the search result.
- %User Temp%\A9R{Random}.tmp
To delete malware/grayware/spyware folders:
For Windows 2000, Windows XP, and Windows Server 2003:
- Right-click Start then click Search... or Find..., depending on the version of Windows you are running.
- In the File name* input box, type:
- %User Temp%\A9R{Random}.tmp
- In the Look In drop-down list, select My Computer, then press Enter.
- Once located, select the folder then press SHIFT+DELETE to permanently delete the folder.
- Repeat steps 2 to 4 for the remaining folders:
- %User Temp%\A9R{Random}.tmp
*Note: The file name input box title varies depending on the Windows version (e.g. Search for files or folders named or All or part of the file name.).
For Windows Vista, Windows 7, Windows Server 2008, Windows 8, Windows 8.1, and Windows Server 2012:
- Open a Windows Explorer window.
- For Windows Vista, 7, and Server 2008 users, click Start>Computer.
- For Windows 8, 8.1, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- %User Temp%\A9R{Random}.tmp
- Once located, select the file then press SHIFT+DELETE to permanently delete the folder.
- Repeat steps 2-3 for the remaining folders:
- %User Temp%\A9R{Random}.tmp
*Note: Read the following Microsoft page if these steps do not work on Windows 7.
Step 5
Search and delete these files
[ Learn More ]
[ back ]
There may be some files that are hidden. Please make sure you check the
Search Hidden Files and Folders checkbox in the "More advanced options" option to include all hidden files and folders in the search result.
- %User Temp%\A9R{Random}.tmp\DOC34175250.docm
To delete malware/grayware files:
For Windows 2000, Windows XP, and Windows Server 2003:
- Right-click Start then click Search....
- In the File name* input box, type
- %User Temp%\A9R{Random}.tmp\DOC34175250.docm
- In the Look In drop-down list, select My Computer then press Enter.
- Once located, select the file then press SHIFT+DELETE to delete it.
- Repeat the said steps for all files listed.
*Note: The file name input box title varies depending on the Windows version (e.g. Search for files or folders named or All or part of the file name.).
For Windows Vista, Windows 7, Windows Server 2008, Windows 8, Windows 8.1, and Windows Server 2012:
- Open a Windows Explorer window.
- For Windows Vista, 7, and Server 2008 users, click Start>Computer.
- For Windows 8, 8.1, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- %User Temp%\A9R{Random}.tmp\DOC34175250.docm
- Once located, select the file then press SHIFT+DELETE to delete it.
- Repeat the said steps for all files listed.
*Note: Read the following Microsoft page if these steps do not work on Windows 7.
Step 6
Scan your computer with your Trend Micro product to delete files detected as PDF_DOCDROP.YYTAV. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 7
Enable the macro virus protection in Microsoft Office Applications
[ Learn More ]
[ back ]
To enable macro virus protection:
• For Microsoft Office 2007 and above:
- Open a Microsoft Office application (e.g. Microsoft Word, Microsoft Excel).
- On the upper left corner, click the Office Button or File tab (for Office 2010 and 2013).
- Click Options
- In the left panel, select Trust Center.
- In the right panel, click the Trust Center Settings button.
- In the left panel, select Macro Settings.
- In the right panel, select Disable all macros without notification and click Ok.
- Close the Office application to apply the new settings.
• For Microsoft Office 2003 and below:
- Open a Microsoft Office application (e.g. Microsoft Word, Microsoft Excel).
- On the Tools menu, click Macro>Security.
- Click the Security Level tab.
- Select High, then click OK.
- Close the Microsoft Office application to apply the new settings.